Events for tag "Hacking"
46 min
A collection of random things
Look what I found under the carpet

64 min
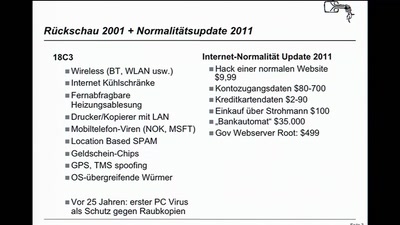
Security Nightmares 2006
Oder: worüber wir nächstes Jahr lachen werden
62 min
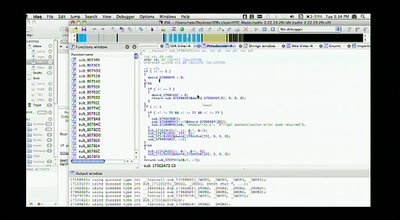
Post Memory Corruption Memory Analysis
Automating exploitation of invalid memory writes

45 min
Introduction to matrix programming: trance codes
How to recognize trance coded communication patterns
52 min
I know who you clicked last summer
A swiss army knife for automatic social investigation

55 min
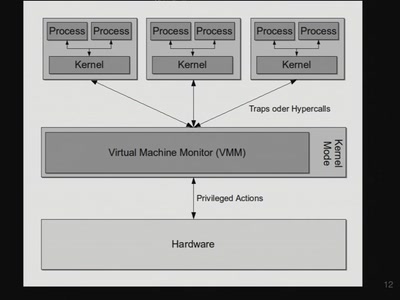
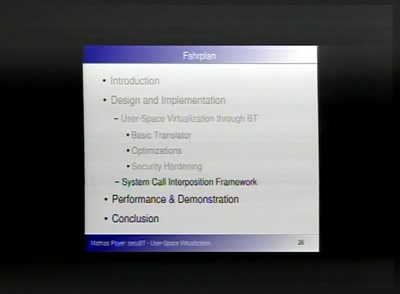
The Future of Virtualization
The "anyOS" paradigm and its implications through…
38 min
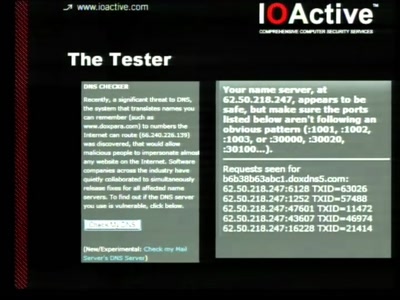
Squeezing Attack Traces
How to get useable information out of your honeypot

72 min
Security Nightmares 2007
Oder: worüber wir nächstes Jahr lachen werden
65 min
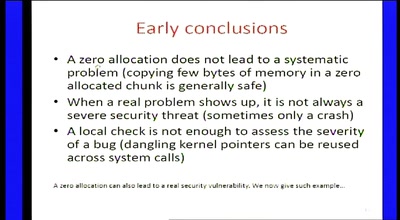
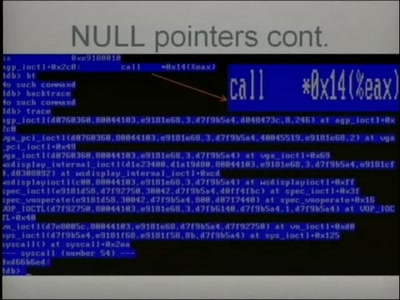
Zero-sized heap allocations vulnerability analysis
Applications of theorem proving for securing the windows…

51 min
Advanced microcontroller programming
Getting deeper into AVR programming

59 min
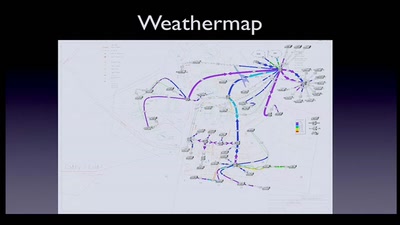
10GE monitoring live!
How to find that special one out of millions

58 min
Cybercrime 2.0
Storm Worm

46 min
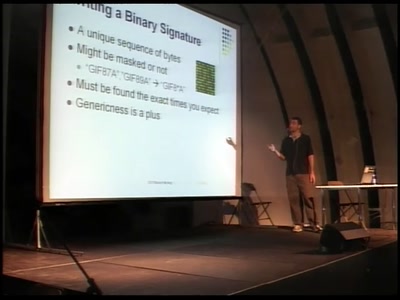
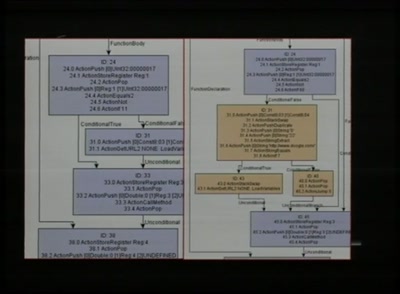
Automated Exploit Detection in Binaries
Finding exploitable vulnerabilities in binaries

55 min
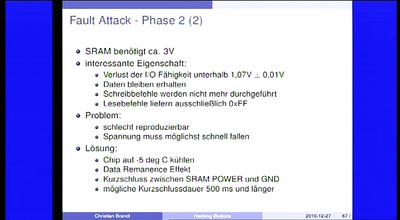
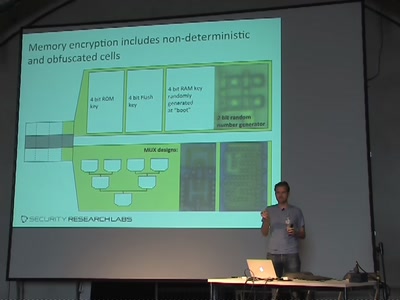
FrozenCache
Mitigating cold-boot attacks for Full-Disk-Encryption…

58 min
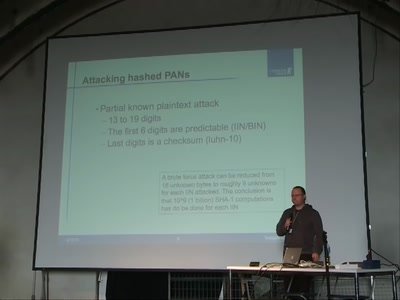
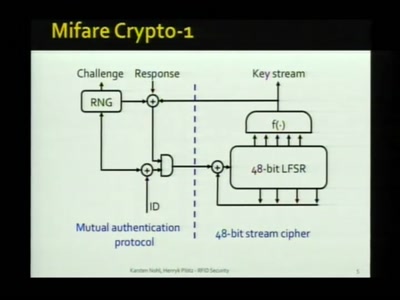
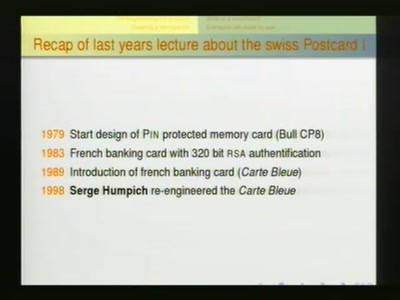
Security Failures in Smart Card Payment Systems
Tampering the Tamper-Proof

66 min
COMPLETE Hard Disk Encryption with FreeBSD
Learn how to effectively protect not only your data but…
46 min
Paper-Prototyping Workshop
Eine Usability-Methode
44 min
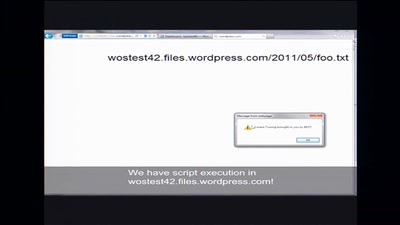
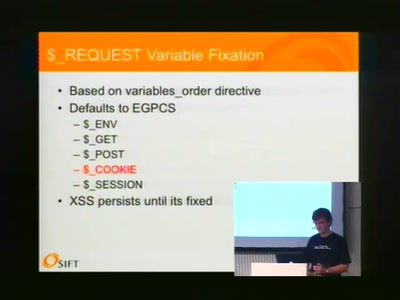
Unusual Web Bugs
A Web Hacker's Bag O' Tricks

53 min
Know your compiler
...and what the optimizer does so you don't have to

55 min
Black Ops 2006 Viz Edition
Pixel Fuzzing and the Bioinformatic Bindiff
48 min
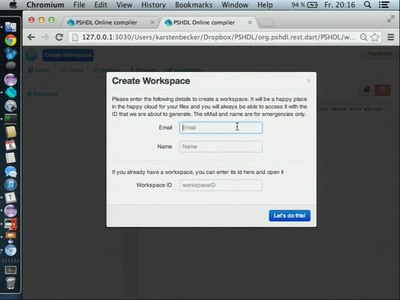
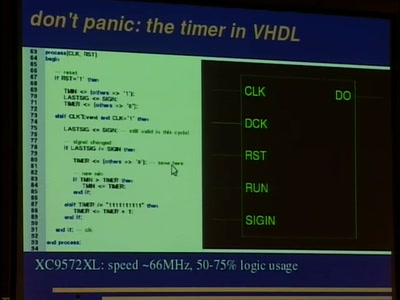
Programming FPGAs with PSHDL
Lets create the Arduino for FPGAs

51 min
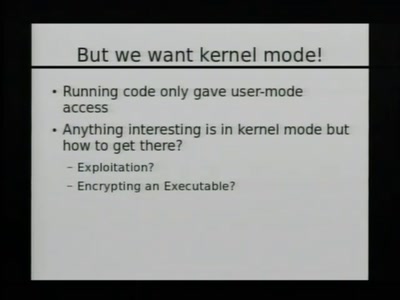
EFI Rootkits
Abusing your Firmware to backdoor the kernel
57 min
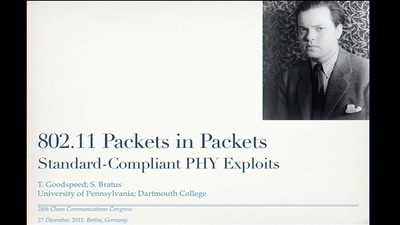
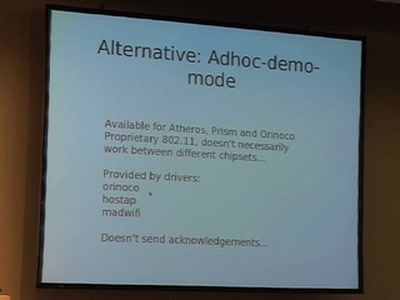
802.11 Packets in Packets
A Standard-Compliant Exploit of Layer 1
55 min
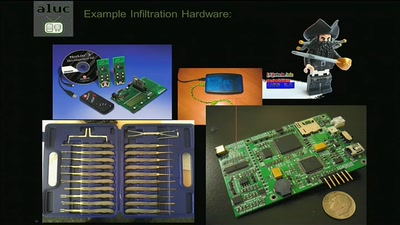
Steal Everything, Kill Everyone, Cause Total Financial Ruin!
Or: How I walked in and misbehaved
55 min
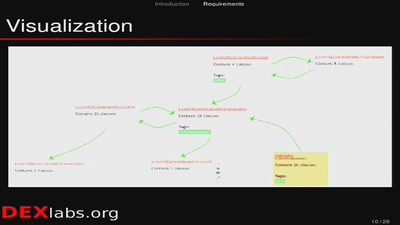
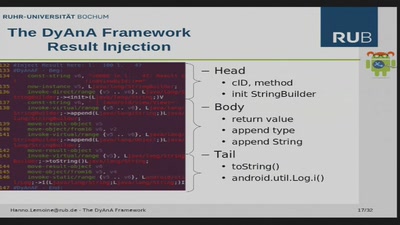
Android Analysis Framework
dex reversing in deep
50 min
Data Analysis in Terabit Ethernet Traffic
Solutions for monitoring and lawful interception within a…

43 min
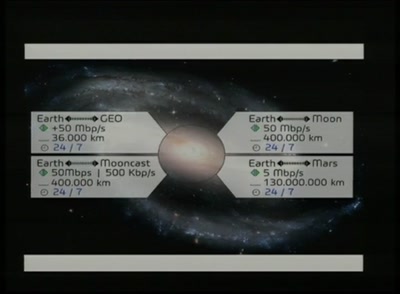
Anonymous Data Broadcasting by Misuse of Satellite ISPs
An open-source project to develop a tool for broadband…
45 min
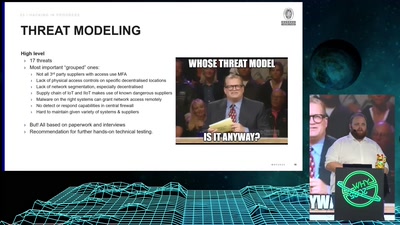
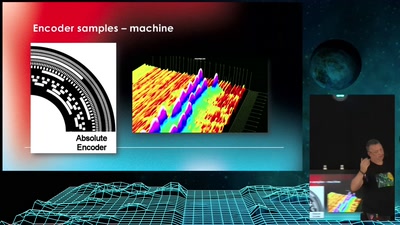
Machine-to-machine (M2M) security
When physical security depends on IT security

43 min
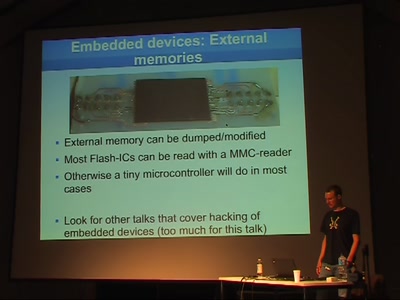
Fudging with Firmware
Firmware reverse-engineering tactics
45 min
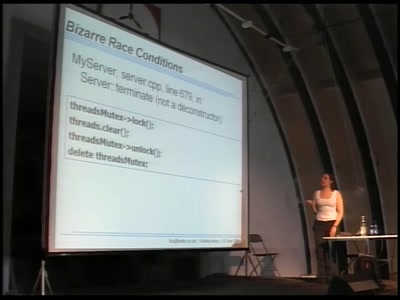
Secure Network Server Programming on Unix
Techniques and best practices to securely code your network…

60 min
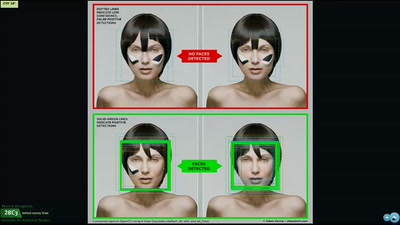
Hacking fingerprint recognition systems
Kann ich dir ein Bier ausgeben?

62 min
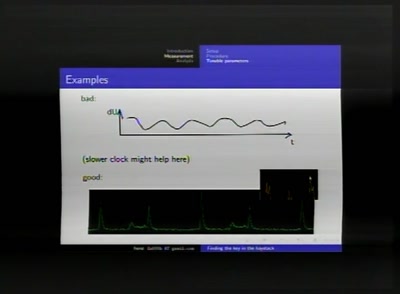
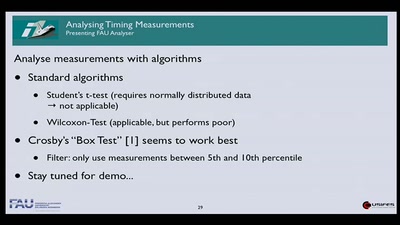
Detecting temperature through clock skew
Hot or Not: Defeating anonymity by monitoring clock skew to…

43 min
Nintendo DS
Introduction and hacking
52 min
The engineering part of social engineering
Why just lying your way in won't get you anywhere
53 min
Private investigations in searching
How to find any book (and many other roadkills) on the…

52 min
Hacking into TomTom Go
Reverse-Engineering des Embedded-Linux-Navigationssystems
58 min
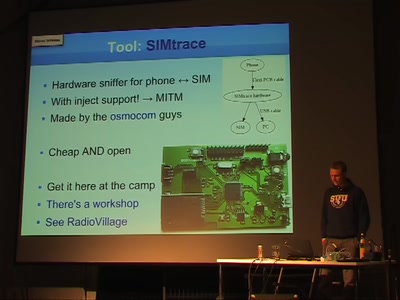
The blackbox in your phone
Some details about SIM cards
59 min
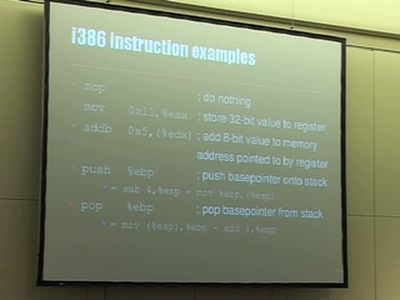
Understanding buffer overflow exploitation
The fascinating interplay of CPU, stack, C-compiler and…
54 min
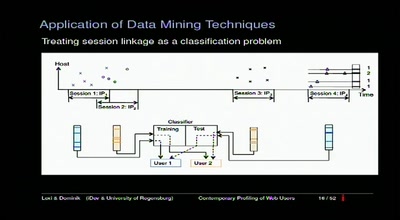
Contemporary Profiling of Web Users
On Using Anonymizers and Still Get Fucked

60 min
Benutze Krake mit Gerät
Programmierbare Logik für Deinen Hardware…
61 min
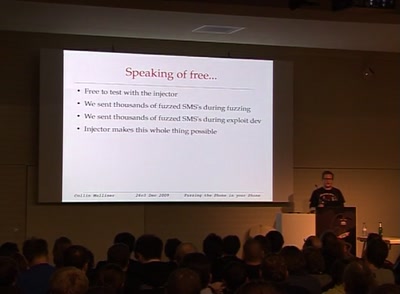
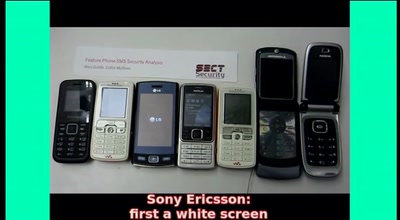
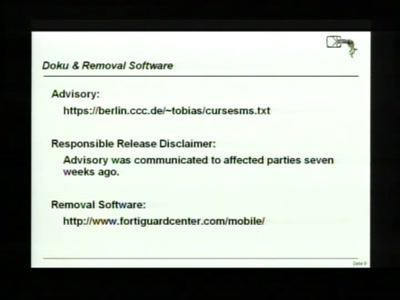
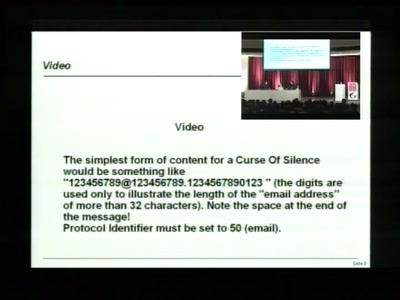
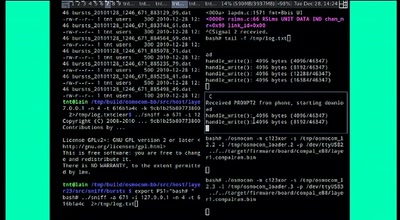
SMS-o-Death
From analyzing to attacking mobile phones on a large scale.

41 min
DC+, The Protocol
Technical defense against data retention law
90 min
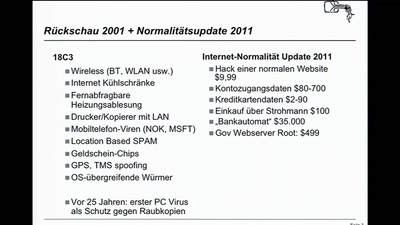
Security Nightmares 2008
Oder: worüber wir nächstes Jahr lachen werden

36 min
Drohnen züchten
UAVs und andere spannende Dinge
44 min
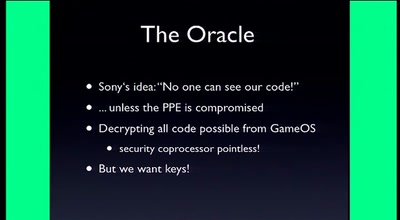
Console Hacking 2010
PS3 Epic Fail

64 min
Covert Communication in a Dark Network
A major new version of freenet
43 min
Twisting timing in your favour
Finding and exploiting concurrency issues in software

50 min
Console Hacking 2006
Xbox 360, Playstation 3, Wii
60 min
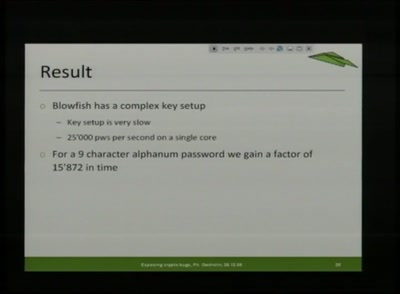
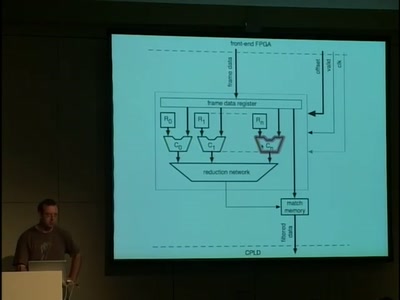
Faster PwninG Assured
Hardware Hacks and Cracks with FPGAs
57 min
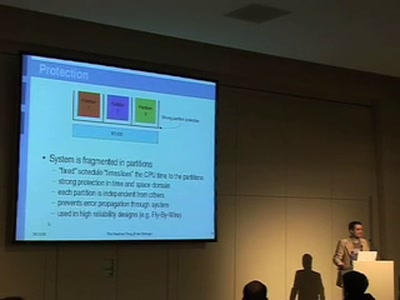
Software Reliability in Aerospace
An overview on design and generation of safe and reliable…
47 min
The Hidden Nemesis
Backdooring Embedded Controllers

68 min
Software Protection and the TPM
The Mac OS X Story

61 min
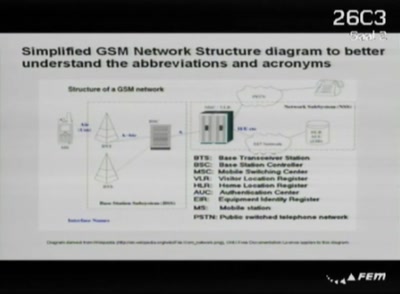
The A5 Cracking Project
Practical attacks on GSM using GNU Radio and FPGAs

119 min
CR217 - Professional Hackers
Ein Einblick in die Security-Industrie

69 min
Mobile phone call encryption
Encrypting (GSM) mobile phone calls over VPN with an…
40 min
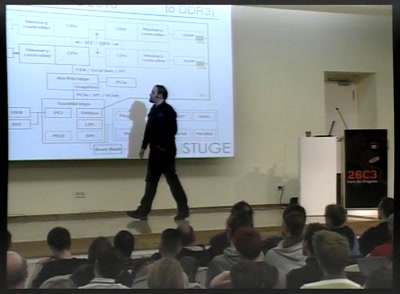
Latest developments around the Milkymist System-on-Chip
A roundup of one the most advanced open hardware projects

60 min
Exploring Protocols and Services on Internet Connected Embedded Devices
Looking for Insecurities
46 min
Signal Intelligence und Electronic Warfare
Wie man nach Hause telefoniert, ohne von einer Rakete…

110 min
SPAM Workshop
SPAM- und Zombie-Abwehr bei hohem Mail-Volumen am Beispiel…
50 min
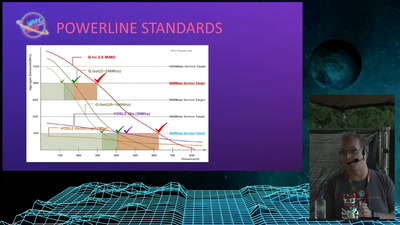
FAIFA: A first open source PLC tool
PowerLineCommunications has now their open source tool
52 min
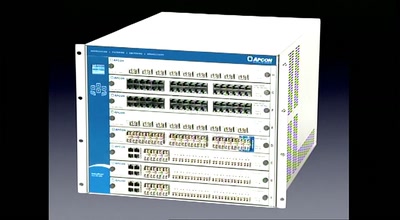
A 10GE monitoring system
Hacking a 10 Gigabit Intrusion detection and prevention…

34 min
Jabber-Showcase
XMPP ist viel mehr als nur Instant Messaging

61 min
Design and Implementation of an object-oriented, secure TCP/IP Stack
Ethereal^W Wireshark without remote exploits - a proof of…
64 min
Sicherheitsanalyse von IT-Großprojekten der öffentlichen Hand
Untersuchung eines Austauschsystems für hochsensible…
34 min
Playstation Portable Cracking
How In The End We Got It All!
62 min
Cellular protocol stacks for Internet
GPRS, EDGE, UMTS, HSPA demystified
53 min
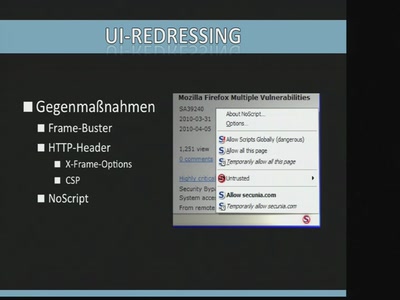
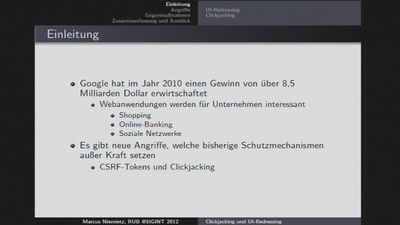
Clickjacking und UI-Redressing
Wie Hacker vorgehen und wie man sich schützen kann

68 min
Inside VMware
How VMware, VirtualPC and Parallels actually work
66 min
Cisco IOS attack and defense
The State of the Art
![Advanced Buffer Overflow Methods [or] Smack the Stack](https://static.media.ccc.de/media/congress/2005/22C3-491-en-advanced_buffer_overflow_methods.jpg)
11 min
Advanced Buffer Overflow Methods [or] Smack the Stack
Cracking the VA-Patch
113 min
"Xbox" and "Xbox 360" Hacking
17 Mistakes Microsoft Made in the Xbox Security System &…

87 min
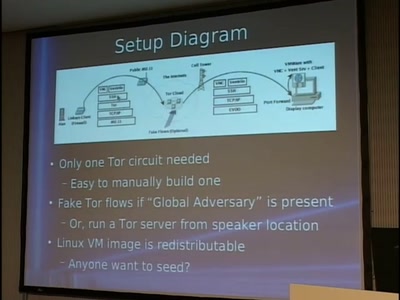
Tor and China
Design of a blocking-resistant anonymity system
59 min
Grundlagen der sicheren Programmierung
Typische Sicherheitslücken

49 min
Hacking Data Retention
How bureaucrats fail to fight terror

61 min
The Realtime Podcast
Everything you need to know about Podcasting
40 min
Wolpertinger. Ein verteilter Portscanner.
Schneller scannen!
46 min
Let's tear down these walls
"Mit Links" die Mauern Sozialer Netzwerke überwinden.
55 min
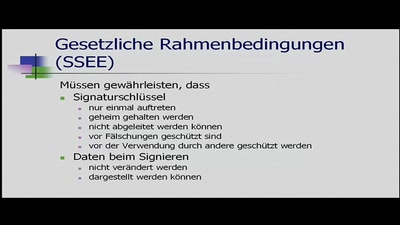
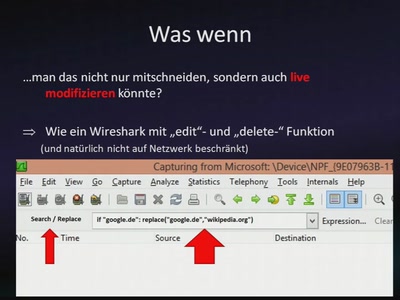
Ein Mittelsmannangriff auf ein digitales Signiergerät
Bachelorarbeit Informatik Uni Kiel SS 2011
85 min
How to find *anything* on the Web
Advanced internet searching strategies & "wizard seeking"…
51 min
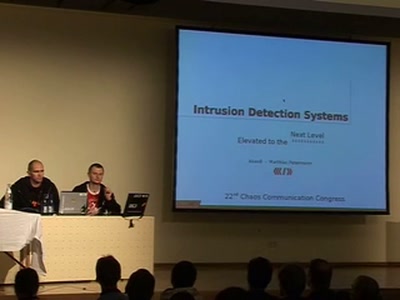
Intrusion Detection Systems
Elevated to the Next Level
59 min
Why Silicon-Based Security is still that hard: Deconstructing Xbox 360 Security
Console Hacking 2007
44 min
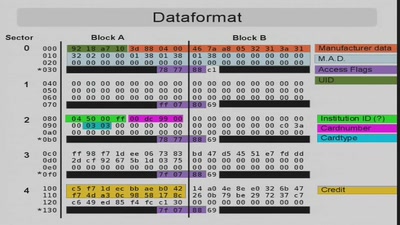
Men who stare at bits
Die abenteuerliche Analyse des Datenformats eines real…
48 min
Advanced Attacks Against PocketPC Phones
0wnd by an MMS
65 min
ZERT: VML, ANI and Third-party Patches
Assembly - lots of it.
92 min
Security Nightmares 2009 (English interpretation)
Or: about what we will laugh next year
37 min
Cracking the MSP430 BSL
Part Two

46 min
Honeymonkeys
Chasing hackers with a bunch of monkeys
57 min
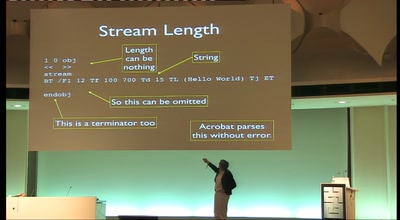
OMG WTF PDF
What you didn't know about Acrobat
53 min
Building a Distributed Satellite Ground Station Network - A Call To Arms
Hackers need satellites. Hackers need internet over…

38 min
Autodafé: An Act of Software Torture
Presentation of an innovative buffer overflow uncovering…
98 min
Hardware Hacking for Software Geeks
Essential Tips and Tricks
61 min
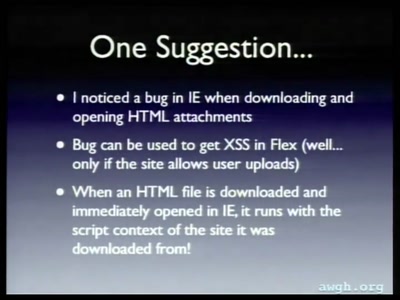
Attacking Rich Internet Applications
Not your mother's XSS bugs
55 min
Cuckoo Sandbox - malware beware
Open Source Dynamic Malware Analysis

128 min
Der Staatstrojaner
Vom braunen Briefumschlag bis zur Publikation

65 min
Blinkenlights Stereoscope
Behind the scenes of the new light installation

53 min
A Case Against C++
Why C++ is bad for the environment, causes global warming…
45 min
Your Disaster/Crisis/Revolution just got Pwned
Telecomix and Geeks without Bounds on Security and Crisis…
39 min
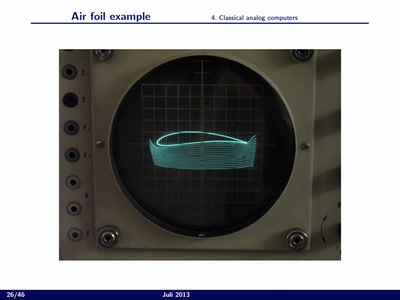
Analog Computing
High performance/low power computing based on the analog…

42 min
Inside the Mac OS X Kernel
Debunking Mac OS Myths
54 min
Collateral Damage
Consequences of Spam and Virus Filtering for the E-Mail…
57 min
How To Design A Decent User Interface
Take a look at software from a user's point of view and…
39 min
Cybernetics for the Masses
implants, sensory extension and silicon - all for you!
46 min
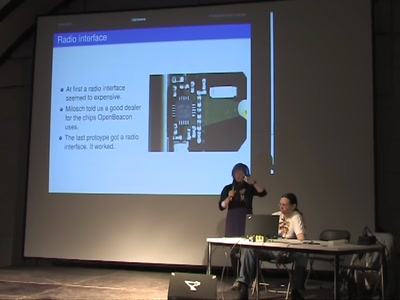
Inside Sputnik & OpenBeacon - Smart Dust for the Masses
a hackers guide into homebrewn 2.4GHz hardware & peripherals
60 min
Macro dragnets: Why trawl the river when you can do the whole ocean
What happens when data collection goes awry in the 21st…

52 min
3G Investigations
Scanning your GPRS/UMTS IP network for fun and profit
63 min
Banking Malware 101
Overview of Current Keylogger Threats
54 min
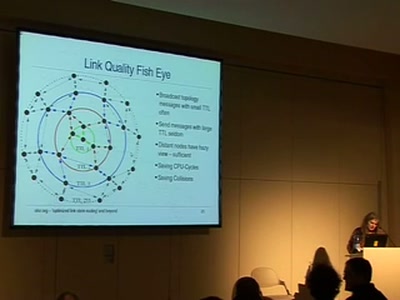
Community mesh networking
Ubiquitous wireless mesh clouds with olsrd from olsr.org

49 min
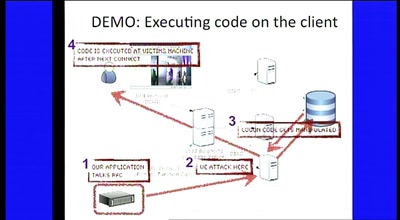
Syscall proxying fun and applications
Introduction to syscall proxying and applications for in…
48 min
GPS-Trackers
How they track you when your mobile is switched off
52 min
Void the warranty!
How to start analyzing blackboxes

48 min
SWF and the Malware Tragedy
Hide and Seek in A. Flash
45 min
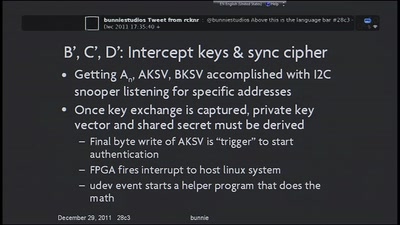
Implementation of MITM Attack on HDCP-Secured Links
A non-copyright circumventing application of the HDCP…
32 min
"Haste ma'n netblock?"
Layer 8 based IP Address hijacking in the end of the days…

56 min
Console Hacking 2008: Wii Fail
Is implementation the enemy of design?
48 min
Vertex Hacking
Reverse Engineering von 3D-Dateiformaten
25 min
Security Log Visualization with a Correlation Engine
What's inside your network?

59 min
Part-Time Scientists
One year of Rocket Science!
54 min
Vier Fäuste für ein Halleluja
Geschichten aus dem API-und Protokollkrieg von zwei…

71 min
Security in the cardholder data processing?!
Experiences and lessons learned with the Payment Card…
54 min
Datamining for Hackers
Encrypted Traffic Mining
55 min
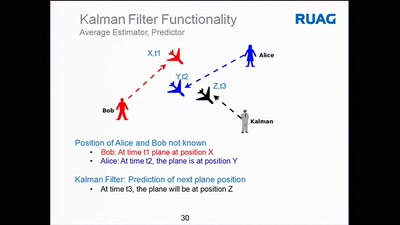
Introducing Osmo-GMR
Building a sniffer for the GMR satphones

60 min
Black Ops Of TCP/IP 2005.5
New Explorations: Large Graphs, Larger Threats

63 min
Virtuelle Sicherheit
Mandatory Access Control und TPM in Xen
25 min
SIP home gateways under fire
Source routing attacks applied to SIP

52 min
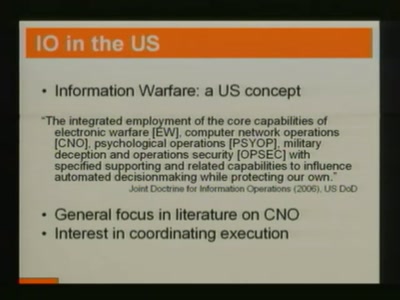
Military intelligence for terrorists(tm)
A lamer's introduction to retrieving "sensitive"…
63 min
Exploiting Symbian
Symbian Exploit and Shellcode Development

135 min
Project Sputnik
Realtime in-building location tracking at the 23C3
65 min
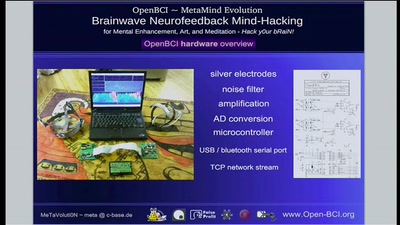
Quantified-Self and OpenBCI Neurofeedback Mind-Hacking
Transhumanism, Self-Optimization and Neurofeedback for…
37 min
Reverse-Engineering DisplayLink devices
USB to DVI for Hackers

56 min
Desperate House-Hackers
How to Hack the Pfandsystem
58 min
Physical Security
The Good, the Bad and the Ugly
61 min
CSRF, the Intranet and You
Causes, Attacks and Countermeasures
58 min
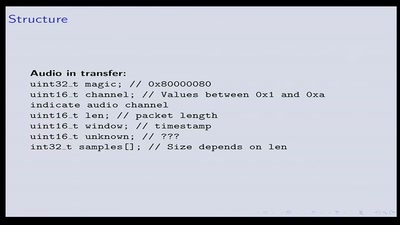
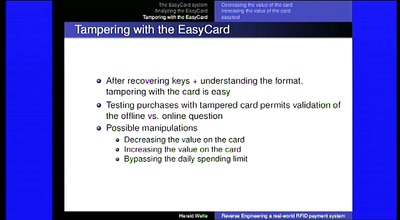
Reverse Engineering a real-world RFID payment system
Corporations enabling citizens to print digital money
64 min
Defense is not dead
Why we will have more secure computers - tomorrow

49 min
Ethernet mit Mikrocontrollern
Wie funktioniert TCP mit 2kb RAM?
56 min
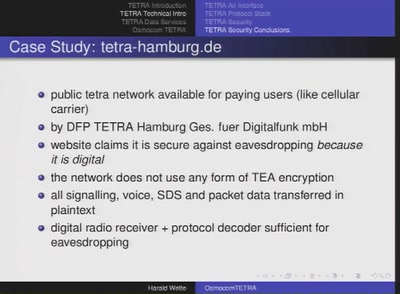
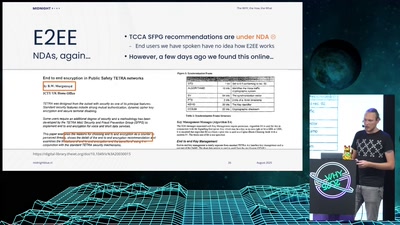
Applied Research on security of TETRA radio
digital radio technology beyond GSM

49 min
Old Skewl Hacking - InfraRed updated
MMIrDA - Major Malfunction's InfraRed Discovery Application
_forget_your_secret_crypto_key.jpg)
34 min
How to (really) forget your secret crypto key
What you always wanted to know about Flash memory - but…
56 min
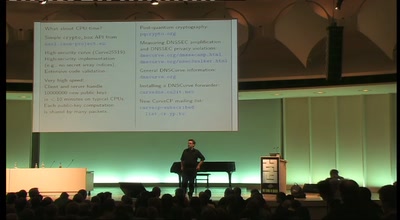
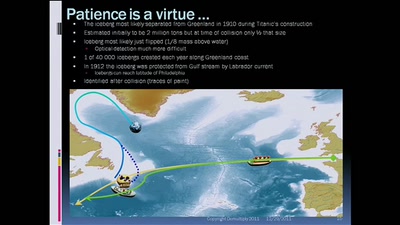
The future of cryptology: which 3 letters algorithm(s) could be our Titanic?
RMS Olympic, RMS Titanic, HMHS Britannic vs Discrete…
64 min
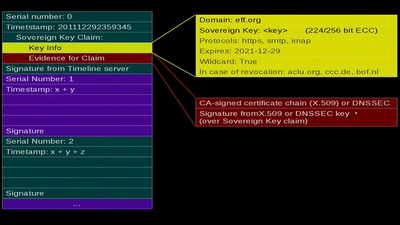
Sovereign Keys
A proposal for fixing attacks on CAs and DNSSEC
56 min
JTAG/Serial/FLASH/PCB Embedded Reverse Engineering Tools and Techniques
a dump of simple tools for embedded analysis at many layers
63 min
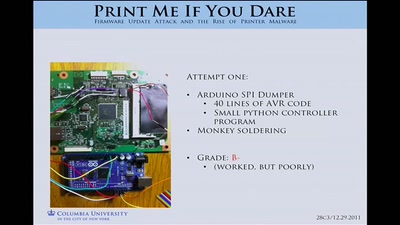
Print Me If You Dare
Firmware Modification Attacks and the Rise of Printer…
36 min
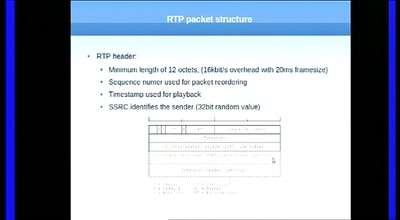
Having fun with RTP
„Who is speaking???“
52 min
Practical Mac OS X Insecurity
Security Concepts, Problems, and Exploits on Your Mac
73 min
hacking smart phones
expanding the attack surface and then some
57 min
Secure Code
Why developing Secure Software is like playing Marble…

53 min
Making music with a C compiler
(also introducing libglitch)
48 min
Full-Disk-Encryption Crash-Course
Everything to hide
45 min
Hopalong Casualty
On automated video analysis of human behaviour

78 min
Stealth malware - can good guys win?
Challenges in detecting system compromises and why we’re so…
53 min
WarTracking
Satellite Tracking, harvesting and security
28 min
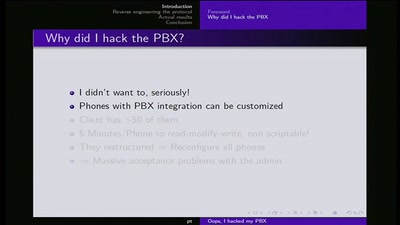
Ooops I hacked my PBX
Why auditing proprietary protocols matters
51 min
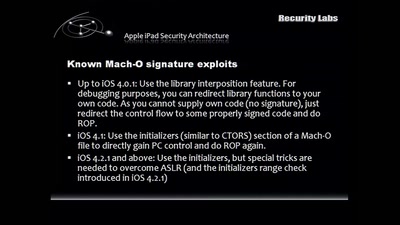
Apple vs. Google Client Platforms
How you end up being the Victim.
26 min
Don't scan, just ask
A new approach of identifying vulnerable web applications
62 min
Automatic Algorithm Invention with a GPU
Hell Yeah, it's rocket science
30 min
TCP Denial of Service Vulnerabilities
Accepting the Partial Disclosure Challenge
49 min
Lawful Interception in VoIP networks
Old Laws and New Technology the German Way
53 min
Crouching Powerpoint, Hidden Trojan
An analysis of targeted attacks from 2005 to 2007
58 min
Advanced memory forensics: The Cold Boot Attacks
Recovering keys and other secrets after power off
50 min
Finding the key in the haystack
A practical guide to Differential Power Analysis
44 min
Dynamic Malware Analysis on Android Phones
Presentation of the DyAnA Framework (Dynamic Android…
47 min
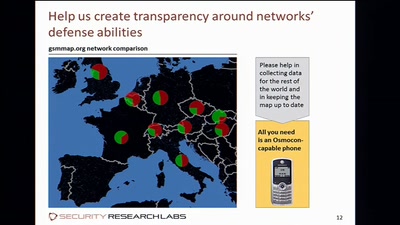
Playing with the GSM RF Interface
Doing tricks with a mobile phone

49 min
VoIPhreaking
Introduction to SIP Hacking
53 min
GNU/Linux für Blinde und Sehbehinderte
Erfahrungen aus der Praxis
61 min
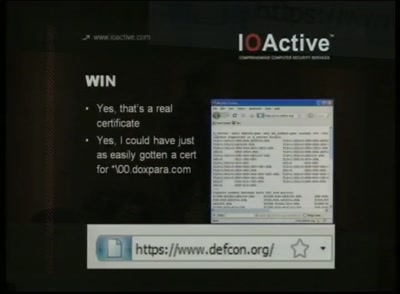
MD5 considered harmful today
Creating a rogue CA Certificate
52 min
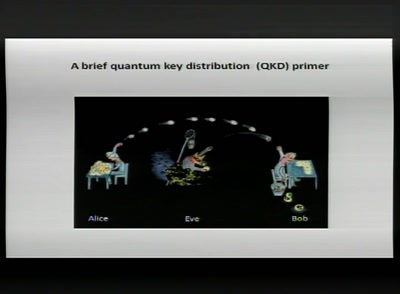
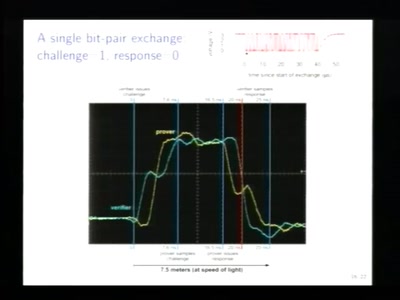
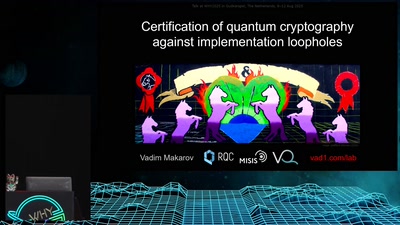
How you can build an eavesdropper for a quantum cryptosystem
hardware demo during the lecture
57 min
Hacking SCADA
how to own critical infrastructures
56 min
Hacking CCTV
Watching the watchers, having fun with cctv cameras, making…
60 min
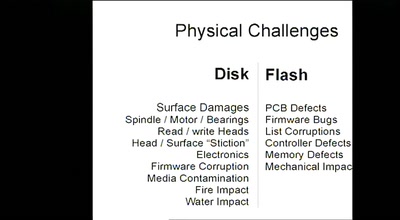
Data Recovery Techniques
Fun with Hard Drives
82 min
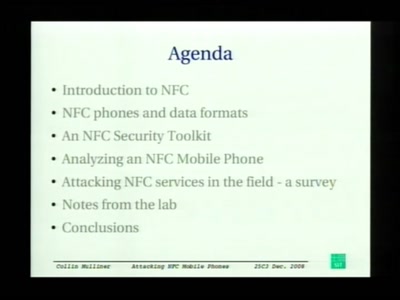
Attacking NFC mobile phones
First look at the security of NFC mobile phones
32 min
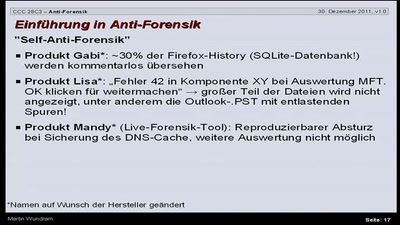
Antiforensik
Einführung in das Thema Antiforensik am Beispiel eines…
56 min
Towards the first Free Software GSM Phone
Reverse Engineering the Motorola EZX (A768,A780,E680)…

63 min
Wireless Kernel Tweaking
or how B.A.T.M.A.N. learned to fly
64 min
The Cell Processor
Computing of Tomorrow or Yesterday

57 min
C64-DTV Hacking
Revisiting the legendary computer in a joystick
62 min
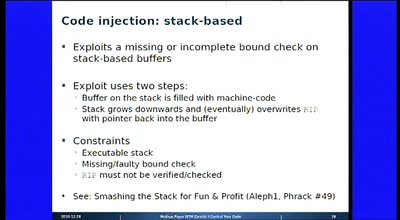
I Control Your Code
Attack Vectors Through the Eyes of Software-based Fault…
52 min
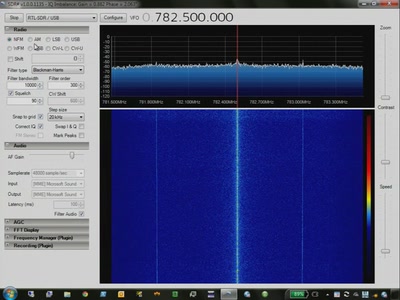
SDR, GSM/OpenBTS
New RF technology - exciting for good guys, bad guys,…
94 min
Security Nightmares 2009
Oder: worüber wir nächstes Jahr lachen werden
51 min
I See Airplanes!
How to build your own radar system
70 min
coreboot: Adding support for a system near you
Working with the open source BIOS replacement and getting a…
59 min
Deceiving Authorship Detection
Tools to Maintain Anonymity Through Writing Style & Current…
51 min
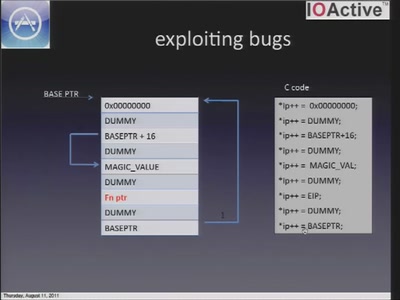
iOS application security
A look at the security of 3rd party iOS applications
47 min
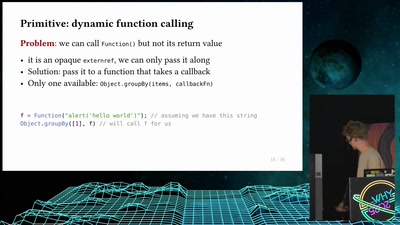
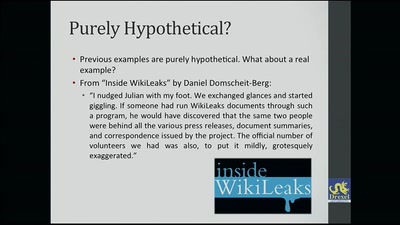
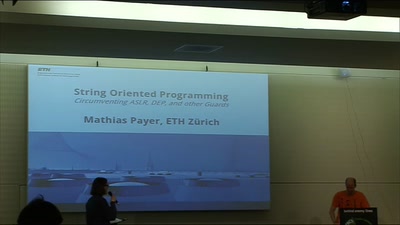
String Oriented Programming
Circumventing ASLR, DEP, and Other Guards
51 min
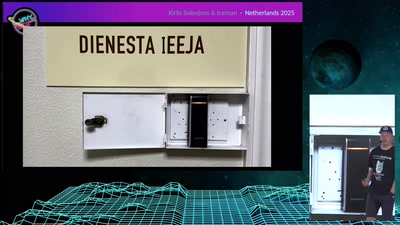
SCADA and PLC Vulnerabilities in Correctional Facilities
Tiffany Rad, Teague Newman, John Strauchs
46 min
Secure Instant Messaging
Suppression of secure communications by governments
34 min
NOC Review
NOC Review about the Camp 2011 and the 28C3

42 min
Just in Time compilers - breaking a VM
Practical VM exploiting based on CACAO
79 min
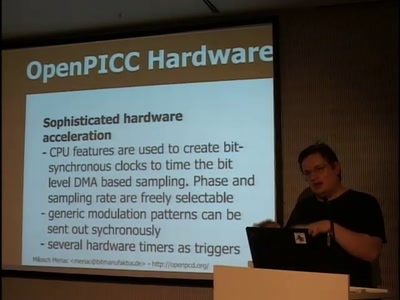
OpenPCD / OpenPICC
Free RFID reader and emulator
50 min
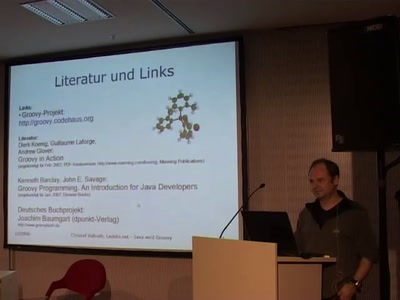
Java wird Groovy
Eine Einführung in die neue, dynamische Sprache für das…

61 min
Der Hackerparagraph 202c StGB
Bestandsaufnahme und Auswirkungen

34 min
XMPP/Jabber
Introducing the 'lingua franca' of Instant Messaging

32 min
Freedom from the web's monopolies
A better architecture for the web, beneficial to both…
53 min
Blackberry: call to arms, some provided
Teach yourself upper management in 22 days
60 min
The Atari 2600 Video Computer System: The Ultimate Talk
The history, the hardware and how to write programs
47 min
RFID - overview of protocols, librfid implementation and passive sniffing
ISO14443, ISO15693, their GPL librfid implementation and…
56 min
Blackbox JTAG Reverse Engineering
Discovering what the hardware architects try to hide from…
46 min
Atmel AVR für Dummies
Was ist denn nun eigentlich so ein 'Interrupt'?
47 min
Fun with NFC Mobile Phones
Near Field Communication
46 min
Tits & Bits
pr0n 2.0
63 min
Power gadgets with your own electricity
escape the basement and make the sun work for you
56 min
Rootkits in your Web application
Achieving a permanent stealthy compromise of user accounts…
48 min
One Token to Rule Them All
Post-Exploitation Fun in Windows Environments
58 min
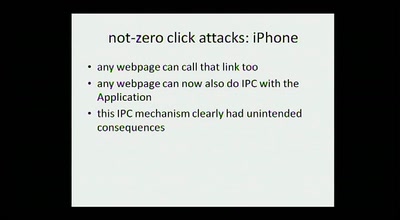
Hacking the iPhone
Pwning Apple's Mobile Internet Device
76 min
Rootkits and Trojans on Your SAP Landscape
SAP Security and the Enterprise

45 min
Router and Infrastructure Hacking
"First we take Manhattan, then we take Berlin..."
55 min
Building a Debugger
Open JTAG with Voltage Glitching
83 min
I/O Capture Treiber Framework
Maßgeschneiderte Geräte-Filtertreiber auf Knopfdruck
56 min
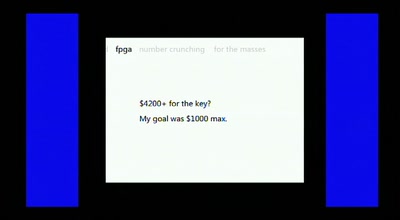
Distributed FPGA Number Crunching For The Masses
How we obtained the equivalent power of a Deep Crack for a…
57 min
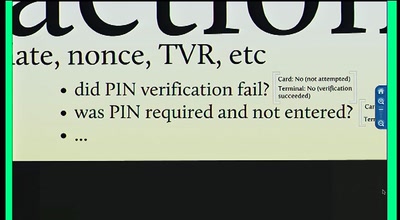
Chip and PIN is Broken
Vulnerabilities in the EMV Protocol

39 min
media.ccc.de
Das YouTube des CCC
71 min
Defending the Poor
Preventing Flash Exploits
35 min
Tricks: makes you smile
A clever or ingenious device or expedient; adroit…
57 min
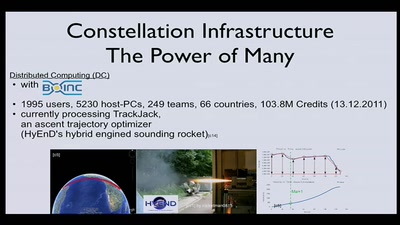
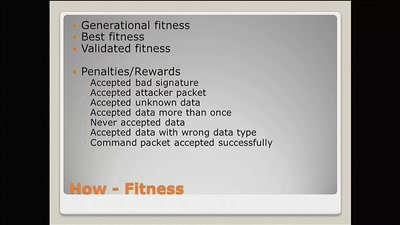
Evolving custom communication protocols
Hell Yeah, it's rocket science
61 min
Time is on my Side
Exploiting Timing Side Channel Vulnerabilities on the Web

61 min
Handschellen hacken
Essentielles Grundwissen für alle, die nichts zu verbergen…

44 min
OnionCat – A Tor-based Anonymous VPN
Building an anonymous Internet within the Internet
59 min
Writing better code (in Dylan)
Fast development of object-oriented functional programs

57 min
Android Security
bringing x86 fuckups to dalvik
26 min
ChokePointProject - Quis custodiet ipsos custodes?
Aggregating and Visualizing (lack of) Transparancy Data in…
53 min
Subverting AJAX
Next generation vulnerabilities in 2.0 Web Applications
45 min
The Convergence of Anti-Counterfeiting and Computer Security
Reverse-engineering currency detection systems

29 min
Mehr Sicherheit für HostAP-WLANs
WLANs mit Wi-Fi Protected Access (WPA) betreiben

61 min
DECT (part II)
What has changed in DECT security after one year
50 min
To be or I2P
An introduction into anonymous communication with I2P
42 min
Covert channels in TCP/IP: attack and defence
Creation and detection of IP steganography for covert…
128 min
A part time scientists' perspective of getting to the moon
presenting the first German Team participating in the…
63 min
Rootkits as Reversing Tools
An Anonymous Talk

45 min
Finding and Preventing Buffer Overflows
An overview of static and dynamic approaches
67 min
Datenvieh oder Daten-Fee
Welchen Wert haben Trackingdaten?
20 min
Introduction to SecureShare
A peer-to-peer, end-to-end encrypted social networking…
Security.jpg)
62 min
Antivirus (In)Security
Bugs in Antivirus Software
50 min
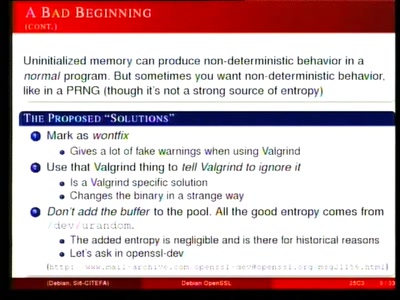
Predictable RNG in the vulnerable Debian OpenSSL package
the What and the How
65 min
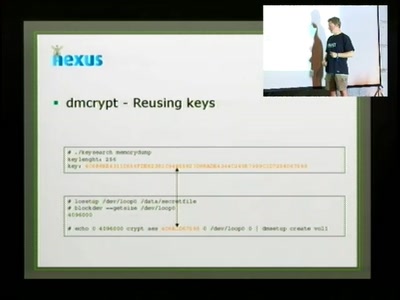
Cryptographic key recovery from Linux memory dumps
Does dm-crypt and cryptoloop provide expected security when…
56 min
Corp vs. Corp
Profiling Modern Espionage
56 min
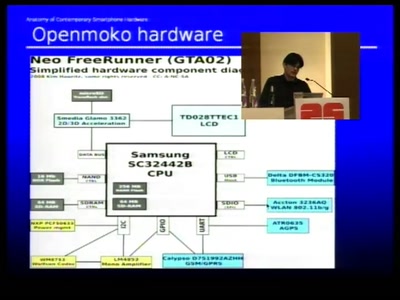
Anatomy of smartphone hardware
Dissecting contemporary cellphone hardware
51 min
GPRS Intercept
Wardriving phone networks

31 min
The DRM Of Pacman
Copy protection schemes of way back then and how they…
46 min
Embedded device security nightmares
An Introduction to the usual mistakes
66 min
The Baseband Apocalypse
all your baseband are belong to us
61 min
The Ultimate Commodore 64 Talk
Everything about the C64 in 64 Minutes
48 min
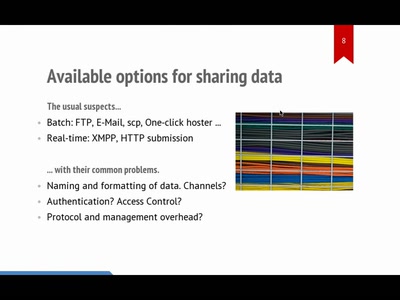
hpfriends: real-time social data-sharing
publish-subscribe feeds + trust relationship network

44 min
Port Scanning improved
New ideas for old practices
44 min
The Realtime thing
What the heck is realtime - and what to do with it

65 min
Practical RFID Attacks
writing, sniffing & emulating 13.56MHz RFID tags with…
34 min
Lying To The Neighbours
Nasty effects with tracker-less BitTorrent

47 min
Peer-to-peer under the hood
An in-depth look at p2p algorithmics
56 min
Effective Denial of Service attacks against web application platforms
We are the 99% (CPU usage)

47 min
How to implement bignum arithmetic
A short look at my pet project implementation
64 min
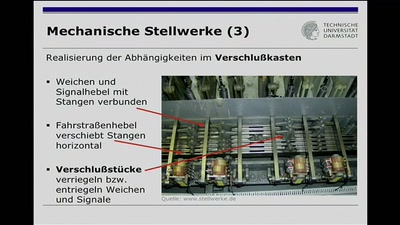
Can trains be hacked?
Die Technik der Eisenbahnsicherungsanlagen
41 min
Einführung in Django
"The Web Framework for perfectionists with deadlines."
48 min
Breaking WEP in less than 60 Seconds
the next level

53 min
Automated Botnet Detection and Mitigation
How to find, invade and kill botnets automated and…

26 min
Data Mining the Israeli Census
Insights into a publicly available registry
45 min
OpenSER SIP Server
VoIP-Systeme mit OpenSER
62 min
Relay attacks on card payment: vulnerabilities and defences
Keeping your enemies close
58 min
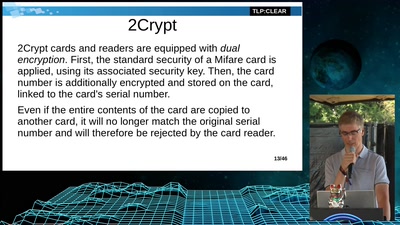
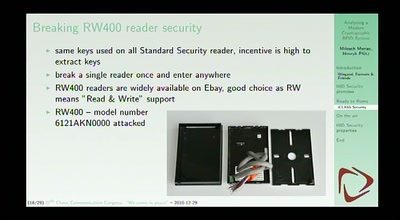
Analyzing a modern cryptographic RFID system
HID iClass demystified
44 min
GNU Radio & the Universal Software Radio Peripheral
Current Capabilities and Future Directions
115 min
Passive covert channels in the Linux kernel
Implementation and detection of kernel based backdoors and…
57 min
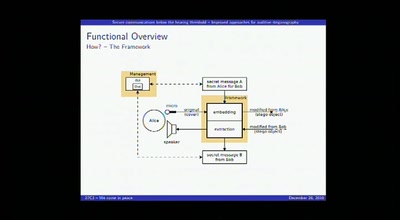
Secure communications below the hearing threshold
Improved approaches for auditive steganography
62 min
Security and anonymity vulnerabilities in Tor
Past, present, and future

48 min
Transcending Places
Programming With Values
57 min
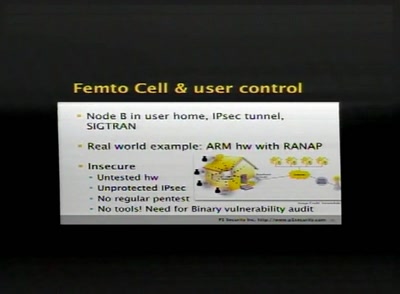
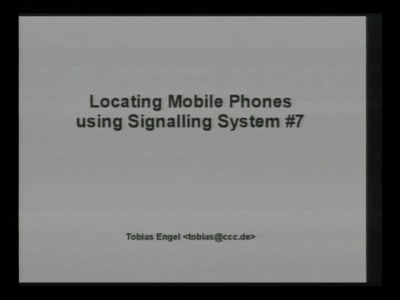
SCCP hacking, attacking the SS7 & SIGTRAN applications one step further and mapping the…
Back to the good old Blue Box?
54 min
Building an Open Source PKI using OpenXPKI
Take a lot of Perl, add some OpenSSL, sprinkle it with a…
57 min
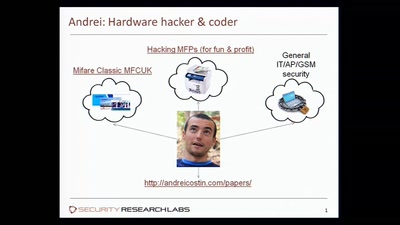
Hacking MFPs
Part2 - PostScript: Um, you've been hacked

93 min
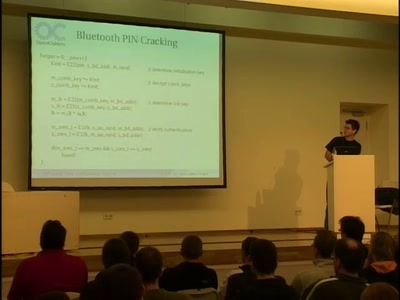
Bluetooth Hacking - The State of The Art
A roundup and live demonstrations of all currently known…
46 min
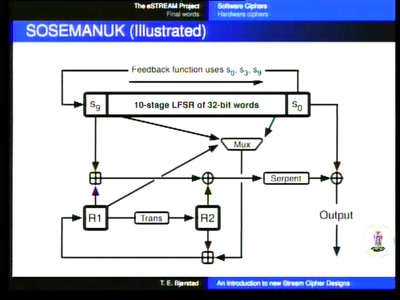
An introduction to new stream cipher designs
Turning data into line noise and back

76 min
Messing Around with Garage Doors
Breaking Remote Keyless Entry Systems with Power Analysis
60 min
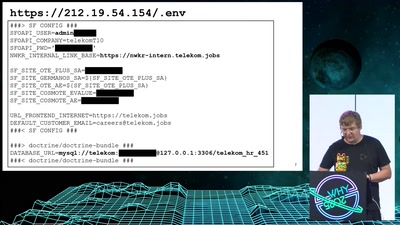
"Die gesamte Technik ist sicher"
Besitz und Wissen: Relay-Angriffe auf den neuen…
51 min
Reverse Engineering the MOS 6502 CPU
3510 transistors in 60 minutes

95 min
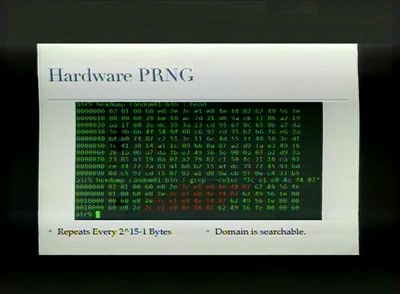
Analysis of a strong Random Number Generator
by anatomizing Linux' CPRNG
62 min
Bionic Ears
Introduction into State-of-the-Art Hearing Aid Technology
63 min
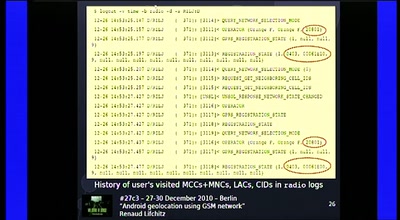
Android geolocation using GSM network
"Where was Waldroid?"
51 min
Strong encryption of credit card information
Attacks on common failures when encrypting credit card…

47 min
What you thought you knew about C
Impacts of undefined behaviour and other C oddities
61 min
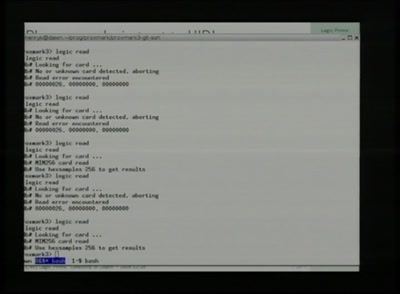
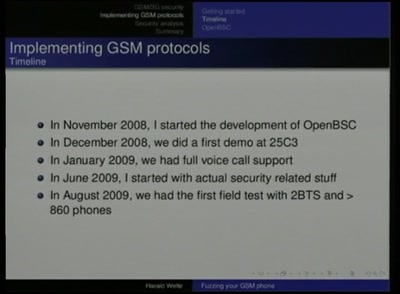
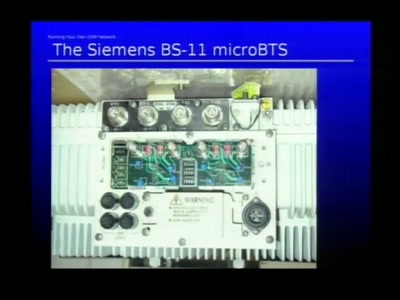
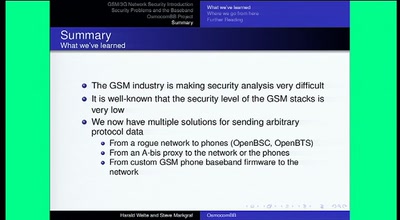
Running your own GSM stack on a phone
Introducing Project OsmocomBB

75 min
Tracker fahrn
We Track Harder - We Track More! Take the pain out of…
52 min
WiFi Long Shots
Wireless connections of 20km and more

50 min
coreboot: Beyond The Final Frontier
Open source BIOS replacement with a radical approach to…

60 min
An Introduction to Traffic Analysis
Attacks, Defences and Public Policy Issues...
53 min
Short Attention Span Security
A little of everything

61 min
PyPy - the new Python implementation on the block
Language/VM R&D, whole program type inference, translation…

117 min
Honeypot Forensics
No stone unturned or: logs, what logs?

42 min
From Ring Zero to UID Zero
A couple of stories about kernel exploiting

45 min
The Kernel Accelerator Device
Reconfigurable computing for the kernel

54 min
Unlocking FileVault
An analysis of Apple's encrypted disk storage system
47 min














![How (not) to configure your domainname [internet.nl]](https://static.media.ccc.de/media/events/why2025/258-ad19d388-2d06-5784-882b-b77588596bb4.jpg)