Rootkits in your Web application
Achieving a permanent stealthy compromise of user accounts with XSS and JS injection attacks.
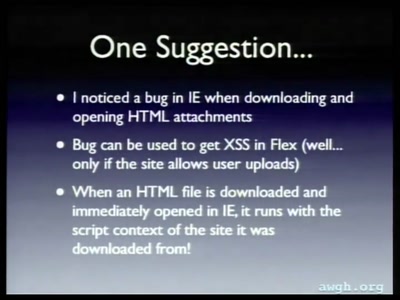
XSS bugs are the most widely known and commonly occurring Web vulnerability,
but their impact has often been limited to cookie theft and/or simple actions,
such as setting malicious email filters, stealing some data, or
self-propagation via an XSS worm. In this work, I discuss practical approaches
for exploiting XSS and other client-side script injection attacks, and introduce
novel techniques for maintaining and escalating access within the victim's
browser. In particular, I introduce the concept of _resident XSS_ where
attacker-supplied code is running in the context of an affected user's main
application window and describe its consequences. I also draw analogies between
such persistent Web threats and the traditional rootkit model, including
similarities in the areas of embedding malicious code, maintaining access,
stealthy communication with a C&C server, and the difficulty of detecting and
removing attacker-supplied code.