60 min
The worst part of censorship is XXXXX
Investigating large-scale Internet content filtering

71 min
Sie haben das Recht zu schweigen
Durchsuchung, Beschlagnahme, Vernehmung - Strategien für…

40 min
Pornography and Technology
a love affair

61 min
Fnord Jahresrückblick
Wir helfen Euch, die Fnords zu sehen

51 min
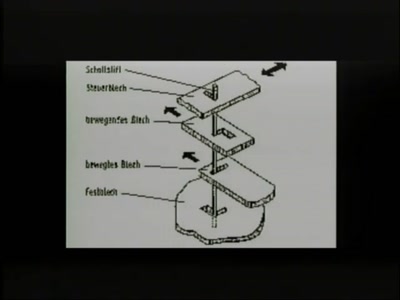
Schlossöffnung bei der Staatssicherheit der DDR
Werkzeuge und Vorgehen der STASI

50 min
Console Hacking 2006
Xbox 360, Playstation 3, Wii
54 min
To live outside the law you gotta be honest
Ist nicht jedes Passwort eine Manifestation des Mißtrauens?

72 min
Security Nightmares 2007
Oder: worüber wir nächstes Jahr lachen werden

107 min
Hacker Jeopardy
The one and only hacker quizshow

60 min
Hacking fingerprint recognition systems
Kann ich dir ein Bier ausgeben?
54 min
Building an Open Source PKI using OpenXPKI
Take a lot of Perl, add some OpenSSL, sprinkle it with a…

47 min
How to implement bignum arithmetic
A short look at my pet project implementation
51 min
Konrad Zuse - Der rechnende Raum
Ein audiovisuelles Live-Feature
51 min
Kritik an den Illuminaten zwischen 1787 und 2006
Der Stand der Auseinandersetzung zwischen Discordiern und…

47 min
Chaos und Kritische Theorie
Adorno, Wilson und Diskordianismus

54 min
Unlocking FileVault
An analysis of Apple's encrypted disk storage system

43 min
Nintendo DS
Introduction and hacking

34 min
Jabber-Showcase
XMPP ist viel mehr als nur Instant Messaging

78 min
Stealth malware - can good guys win?
Challenges in detecting system compromises and why we’re so…

68 min
Inside VMware
How VMware, VirtualPC and Parallels actually work
65 min
Body hacking
Functional body modification
74 min
Digitale Bildforensik
Spuren in Digitalfotos

60 min
Ego Striptease - Ich zeig dir, wer du bist
Blogs, flickr, etc: warum machen wir es ihnen so einfach?
47 min
A not so smart card
How bad security decisions can ruin a debit card design

87 min
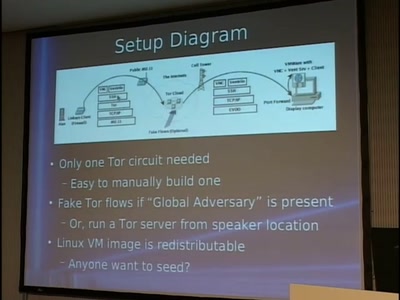
Tor and China
Design of a blocking-resistant anonymity system

64 min
Who can you trust?
Opening Ceremony and Keynote

55 min
Black Ops 2006 Viz Edition
Pixel Fuzzing and the Bioinformatic Bindiff
58 min
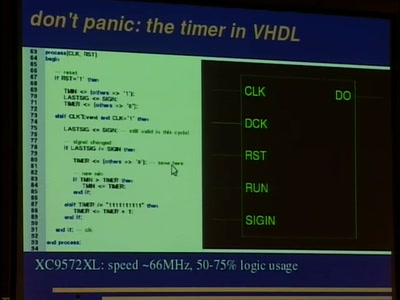
DVB-T - From Pixeldata to COFDM Transmission
How to build a complete FPGA-based DVB-T transmitter

138 min
We don't trust voting computers
The story of the dutch campaign against black-box voting to…

69 min
Mobile phone call encryption
Encrypting (GSM) mobile phone calls over VPN with an…

59 min
CCC Jahresrückblick
Ein Überblick über die Aktivitäten des Clubs 2006

95 min
Analysis of a strong Random Number Generator
by anatomizing Linux' CPRNG

60 min
An Introduction to Traffic Analysis
Attacks, Defences and Public Policy Issues...
58 min
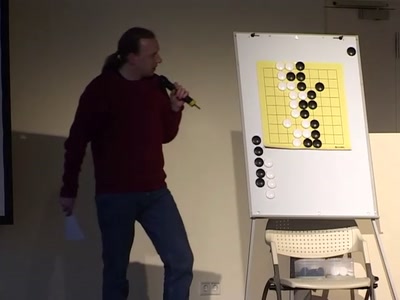
Go - Das Spiel für die Menschen
Auch für Computer? - Nicht beim Go!

51 min
Culture Jamming & Discordianism
Illegal Art & Religious Bricolage

68 min
Überwachungsdruck - einige Experimente
Wie wirkt Überwachung?

45 min
Router and Infrastructure Hacking
"First we take Manhattan, then we take Berlin..."

46 min
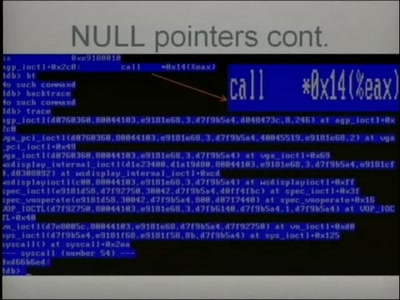
Automated Exploit Detection in Binaries
Finding exploitable vulnerabilities in binaries
79 min
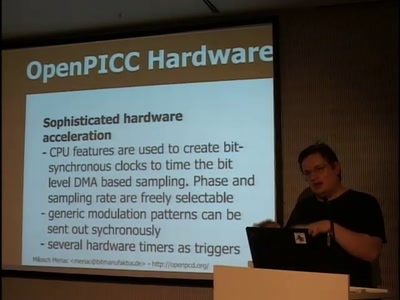
OpenPCD / OpenPICC
Free RFID reader and emulator
64 min
Tracking von Personen in Videoszenen
Wie trackt man automatisch sich bewegende Objekte?

53 min
Nerds und Geeks zwischen Stereotyp und Subkultur
Eine kulturanthropologische Untersuchung

62 min
Vehicular Communication and VANETs
The future and security of communicating vehicles

49 min
Ethernet mit Mikrocontrollern
Wie funktioniert TCP mit 2kb RAM?
56 min
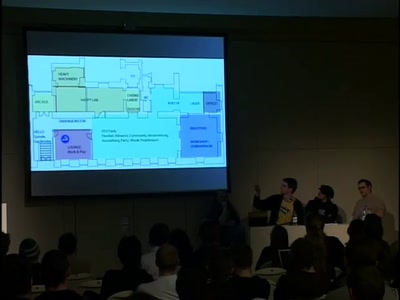
Hackerspaces
How we built ours - How you can build yours
52 min
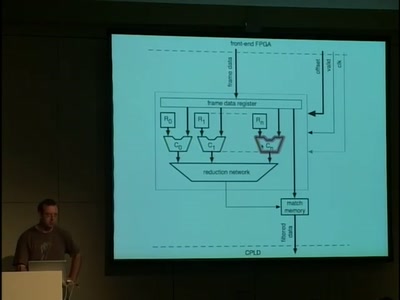
A 10GE monitoring system
Hacking a 10 Gigabit Intrusion detection and prevention…
55 min
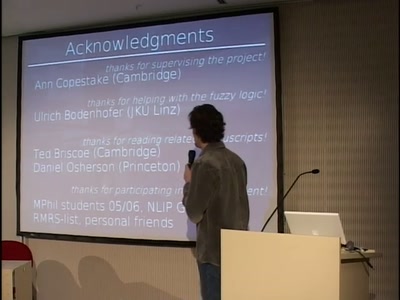
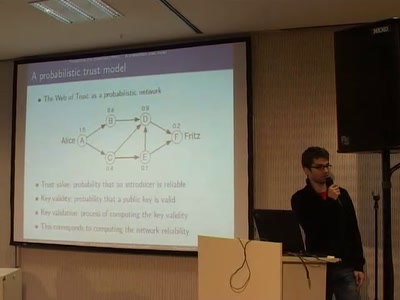
A Probabilistic Trust Model for GnuPG
A new way of evaluating a PGP web of trust by using a…

53 min
Automated Botnet Detection and Mitigation
How to find, invade and kill botnets automated and…

56 min
Elektronische Reisedokumente
Neue Entwicklungen beim ePass

135 min
Project Sputnik
Realtime in-building location tracking at the 23C3

68 min
Software Protection and the TPM
The Mac OS X Story
61 min
Kollaboratives Wissensmanagement im Bildungsbereich
Die Zitierfähigkeit von Wiki-Wissen

43 min
Fudging with Firmware
Firmware reverse-engineering tactics
52 min
Funkerspuk
radio politics in the USA and Germany in the first half of…

71 min
Security in the cardholder data processing?!
Experiences and lessons learned with the Payment Card…
52 min
Void the warranty!
How to start analyzing blackboxes
57 min
How To Design A Decent User Interface
Take a look at software from a user's point of view and…

52 min
4+2+1 Jahre BigBrotherAwards Deutschland
Eine Lesung aus dem Buch "Schwarzbuch Datenschutz"

61 min
Design and Implementation of an object-oriented, secure TCP/IP Stack
Ethereal^W Wireshark without remote exploits - a proof of…
58 min
How to squeeze more performance out of your wifi
Cross-layer optimization strategies for long-range IEEE…
62 min
Warum wir uns so gerne überwachen lassen…
Erhellendes aus Philosophie und Soziologie zur Klärung des…

45 min
Introduction to matrix programming: trance codes
How to recognize trance coded communication patterns

63 min
Virtuelle Sicherheit
Mandatory Access Control und TPM in Xen

46 min
Freie Software - Eine Chance für Afrika?
Ein Erfahrungsbericht aus Malawi
48 min
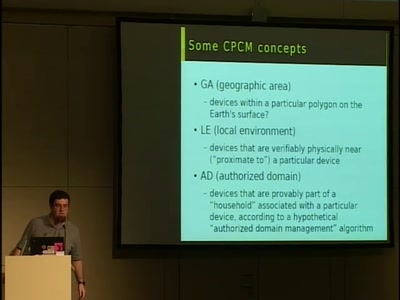
DRM comes to European digital TV
How the DVB project is locking down TV standards and…
48 min
Advanced Attacks Against PocketPC Phones
0wnd by an MMS
62 min
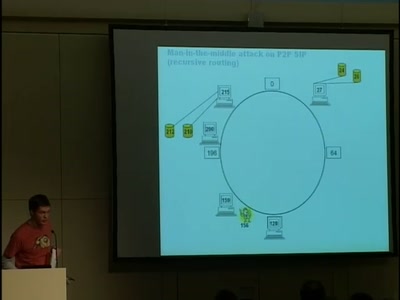
SIP Security
Status Quo and Future Issues
61 min
CSRF, the Intranet and You
Causes, Attacks and Countermeasures

62 min
Detecting temperature through clock skew
Hot or Not: Defeating anonymity by monitoring clock skew to…
63 min
Güter und Personen "tracken" - Lokalisierung im Pizzamann-Universum
Technische Mittel und soziale Aspekte des "Tracking &…

31 min
Closing Ceremony
Who did you trust?
63 min
Biometrics in Science Fiction
2nd Iteration
53 min
Revenge of the Female Nerds
Busting Myths about Why Women Can't Be Technical
45 min
Secure Network Server Programming on Unix
Techniques and best practices to securely code your network…

98 min
The Grim Meathook Future
How The Tech Culture Can Maintain Relevance In The 21st…
50 min
Java wird Groovy
Eine Einführung in die neue, dynamische Sprache für das…

44 min
Open Source Machine Translation
From tools, to tricks, to projects: build a translation…
57 min
Software Reliability in Aerospace
An overview on design and generation of safe and reliable…
46 min
The Rise and Fall of Open Source
The Million Eyeball Principle and forkbombs
36 min
Trust Your Eyes
Grundlagen der Visualisierung und wie man mit…

64 min
Das neue gesetzliche Verbot des Hackings
Praktische Auswirkungen des neuen Strafrechtes, das in…
61 min
Hacking a Country: FOSS in India
An Overview Free and Open Source Software efforts and…
54 min
Juristische Fragen um die Mitbenutzung fremder WLANs
Zivilrechtliche und strafrechtliche Haftung
45 min
Homegrown Interactive Tables
Any Technology Sufficiently Advanced is Indistinguishable…
53 min
Fuzzing in the corporate world
The use of fuzzing in the corporate world over the years…
63 min
Rootkits as Reversing Tools
An Anonymous Talk
53 min
Subverting AJAX
Next generation vulnerabilities in 2.0 Web Applications
56 min
Dying Giraffe Recordings: A non-evil recordlabel
Using the power of creative commons to create an…
63 min
Transparency and Privacy
The 7 Laws of Identity and the Identity Metasystem
97 min
Tap the Electronic Frontier Foundation
EFF staffers answer your questions!
57 min
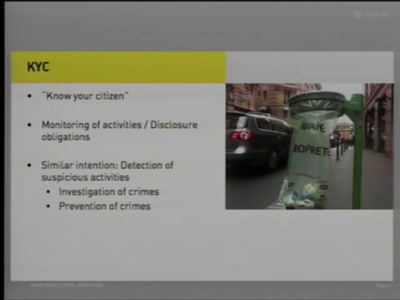
Know Your Citizens
State Authorities' Access to Sensitive Information
62 min
The Story of The Hacker Foundation
Challenges of Organizing a Foundation for Hackers in the USA
60 min
Faster PwninG Assured
Hardware Hacks and Cracks with FPGAs
68 min
Data Retention Update
News and Perspectives on Implementation and Opposition
76 min
Information Operations
Sector-Oriented Analysis of the Potential Impact and…
49 min
Mining Search Queries
How to discover additional knowledge in the AOL query logs

63 min
Counter-Development
The Accessibility of Technology as an Addendum to…

48 min
The gift of sharing
A critical approach to the notion of gift economy within…

66 min