Search for "AKO" returned 1184 results
67 min
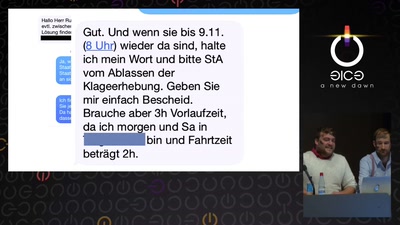
Mit Kunst die Gesellschaft hacken
Das Zentrum für politische Schönheit

38 min
Kickstart the Chaos: Hackerspace gründen für Anfänger
Ein Erfahrungsbericht aus unbetreuter Vereinsmeierei
58 min
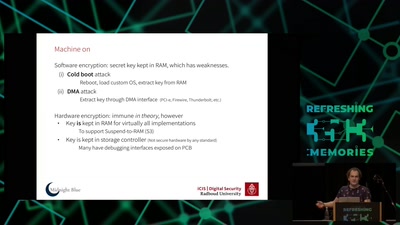
Self-encrypting deception
weaknesses in the encryption of solid state drives (SSDs)
44 min
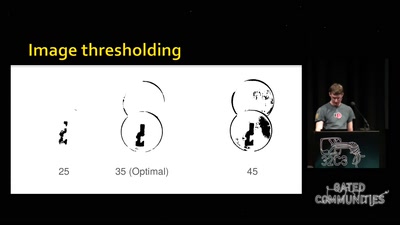
Replication Prohibited
3D printed key attacks
54 min
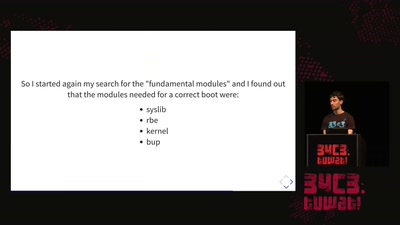
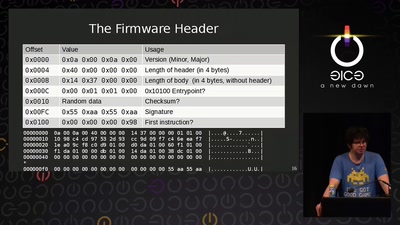
AMD x86 SMU firmware analysis
Do you care about Matroshka processors?
53 min
Million Dollar Dissidents and the Rest of Us
Uncovering Nation-State Mobile Espionage in the Wild
59 min
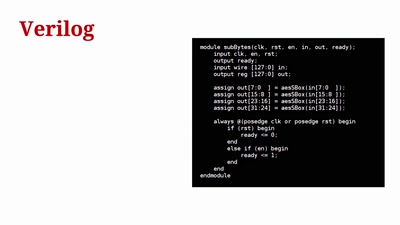
Towards General Purpose Reconfigurable Computing on Novena
FPGAs for Everybody with Novena

57 min
Everything you want to know about x86 microcode, but might have been afraid to ask
An introduction into reverse-engineering x86 microcode and…

63 min
The Global Assassination Grid
The Infrastructure and People behind Drone Killings
59 min
Top X* usability obstacles
*(will be specified later based on usability test with…
49 min
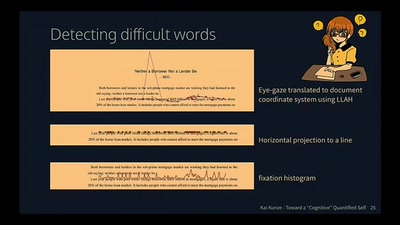
Toward a Cognitive "Quantified Self"
Activity Recognition for the Mind
120 min
Hacken, dass...?
Ack, die Wette gilt!
53 min
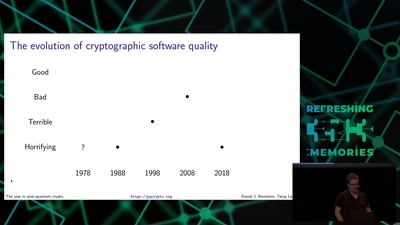
Cryptography demystified
An introduction without maths
60 min
Prediction and Control
Watching Algorithms
55 min
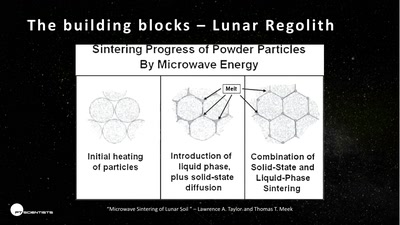
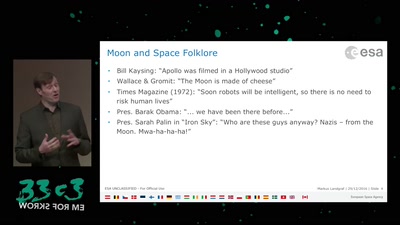
3D printing on the moon
The future of space exploration
61 min