Search for "邯.byx" returned 4327 results

39 min
Neuroexploitation by Design
Wie Algorithmen in Glücksspielprodukten sich Wirkweisen des…
38 min
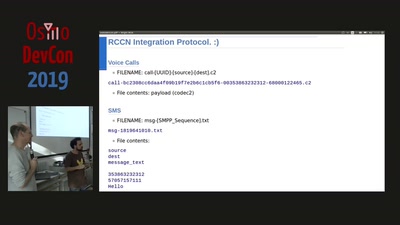
What your phone won’t tell you
Uncovering fake base stations on iOS devices

55 min
Because "use urandom" isn't everything: a deep dive into CSPRNGs in Operating Systems &…
Implementation, hazards and updates on use of RNGs in…
60 min
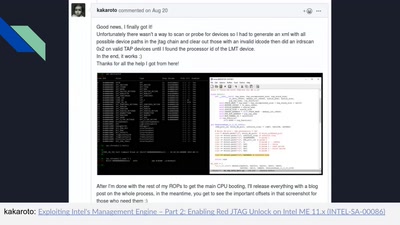
Intel Management Engine deep dive
Understanding the ME at the OS and hardware level
61 min
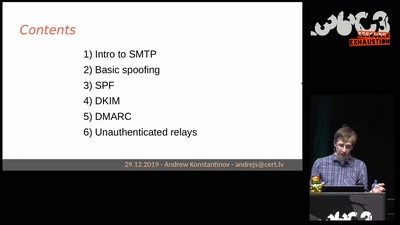
Email authentication for penetration testers
When SPF is not enough
43 min
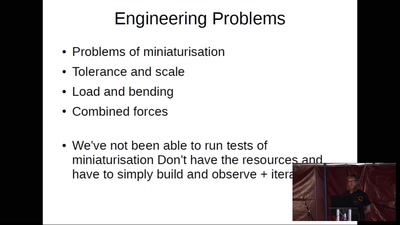
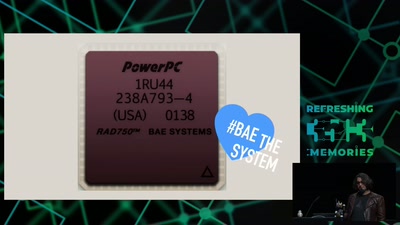
The Mars Rover On-board Computer
How Curiosity's Onboard Computer works, and what you can…

55 min
What is Good Technology?
Answers & practical guidelines for engineers.

60 min
Attacking end-to-end email encryption
Efail, other attacks and lessons learned.
55 min