Search for "Ben H." returned 6003 results

31 min
Buffered Daemons
Sound art performance exploring the concept of translation…
63 min
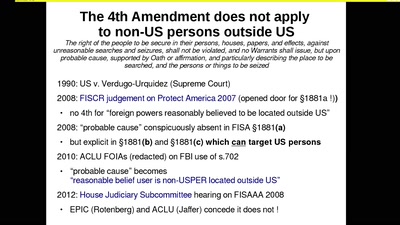
The Cloud Conspiracy 2008-2014
how the EU was hypnotised that the NSA did not exist
44 min
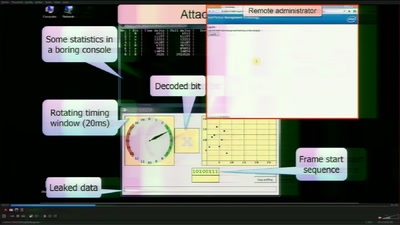
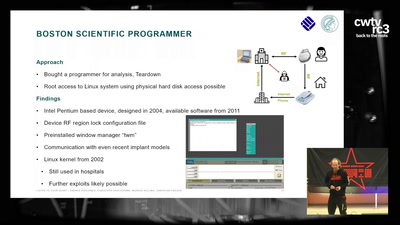
Disclosure DOs, Disclosure DON'Ts
Pragmatic Advice for Security Researchers
39 min
DISNOVATION.ORG
Disobedient Innovation
31 min
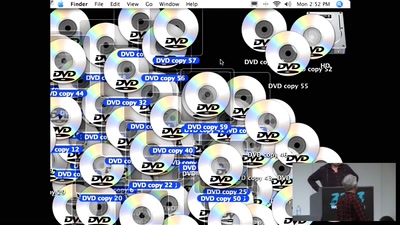
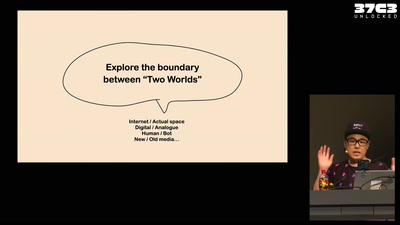
JODI - Apache is functioning normally
A net.art collective since 1995. Understanding the browser…
44 min
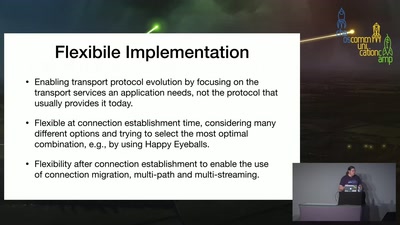
TAPS Transport Services API
Retiring the BSD Socket API
55 min
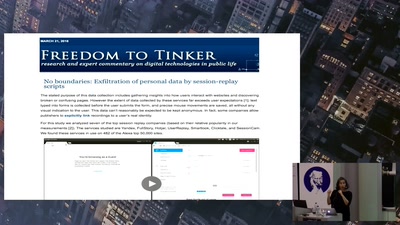
POTs: The revolution will not be optimized?
Protective Optimization Technologies
26 min
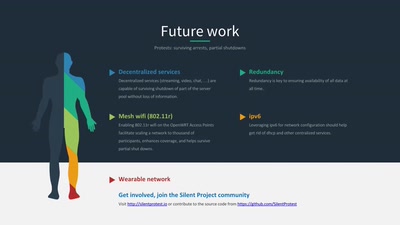
Silent Protest
DIY wearable protest network
20 min
Introduction to SecureShare
A peer-to-peer, end-to-end encrypted social networking…
27 min