51 min
Smart Home - Smart Hack
Wie der Weg ins digitale Zuhause zum Spaziergang wird
57 min
Du kannst alles hacken – du darfst dich nur nicht erwischen lassen.
OpSec für Datenreisende

61 min
wallet.fail
Hacking the most popular cryptocurrency hardware wallets
46 min
What The Fax?!
Hacking your network likes it's 1980 again
39 min
Venenerkennung hacken
Vom Fall der letzten Bastion biometrischer Systeme
61 min
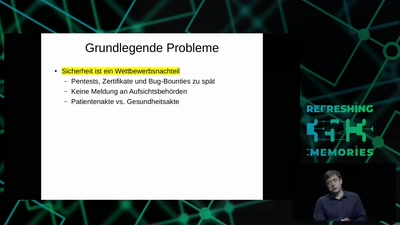
All Your Gesundheitsakten Are Belong To Us
"So sicher wie beim Online-Banking": Die elektronische…
32 min
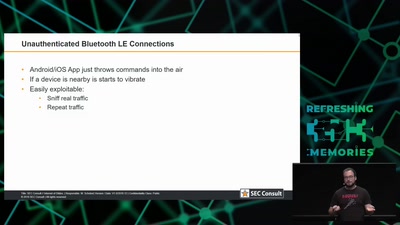
Internet of Dongs
A long way to a vibrant future
37 min
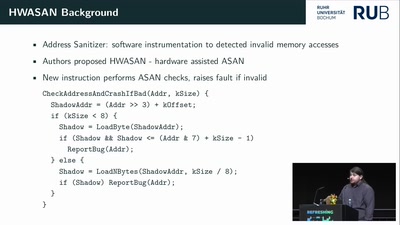
Inside the AMD Microcode ROM
(Ab)Using AMD Microcode for fun and security
52 min
SiliVaccine: North Korea's Weapon of Mass Detection
How I Learned to Stop Worrying and Love the Backdoor
38 min
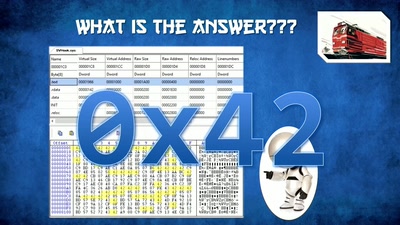
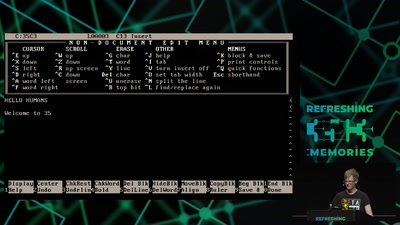
A deep dive into the world of DOS viruses
Explaining in detail just how those little COM files…
56 min
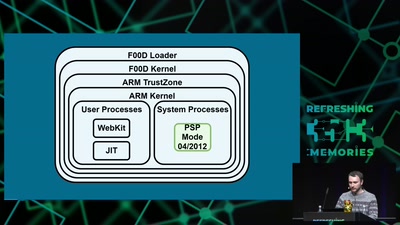
Viva la Vita Vida
Hacking the most secure handheld console

60 min
Attacking end-to-end email encryption
Efail, other attacks and lessons learned.
54 min
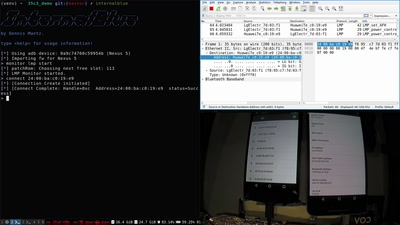
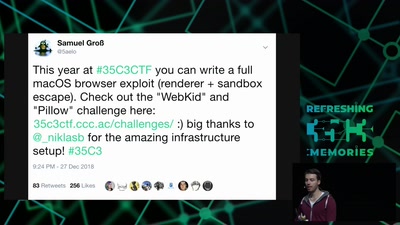
Attacking Chrome IPC
Reliably finding bugs to escape the Chrome sandbox

36 min
Modchips of the State
Hardware implants in the supply-chain
47 min
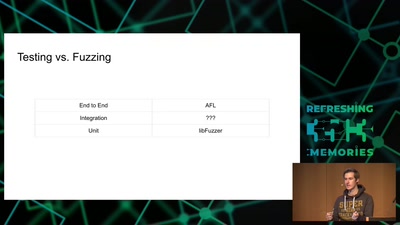
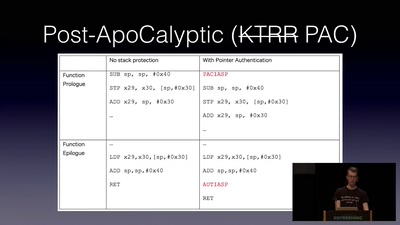
Jailbreaking iOS
From past to present
58 min
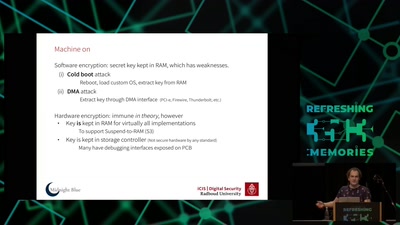
Self-encrypting deception
weaknesses in the encryption of solid state drives (SSDs)
57 min
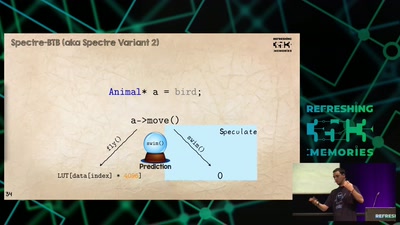
The Layman's Guide to Zero-Day Engineering
A demystification of the exploit development lifecycle
60 min
Sneaking In Network Security
Enforcing strong network segmentation, without anyone…
54 min
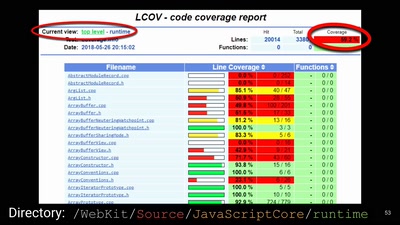
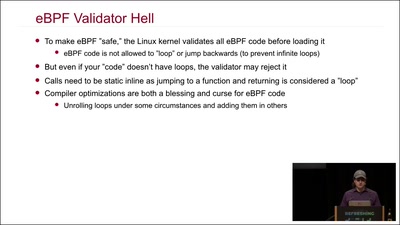
Kernel Tracing With eBPF
Unlocking God Mode on Linux
49 min
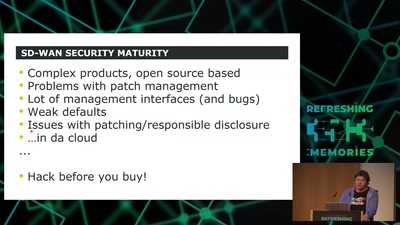
SD-WAN a New Hop
How to hack software defined network and keep your sanity?
35 min
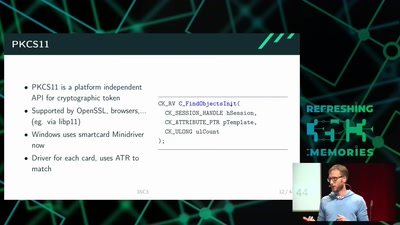
Wallet Security
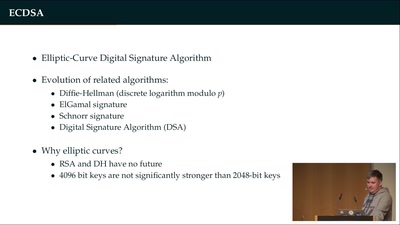
How (not) to protect private keys
42 min
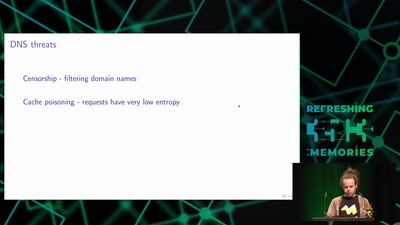
Domain Name System
Hierarchical decentralized naming system used since 30 years
59 min
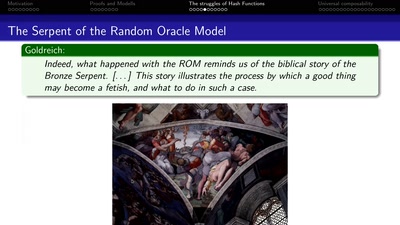
Provable Security
How I learned to stop worrying and love the backdoor
39 min
Web-based Cryptojacking in the Wild
When your browser is mining coins for other people
61 min