A deep dive into the world of DOS viruses
Explaining in detail just how those little COM files infected and played with us back in the day
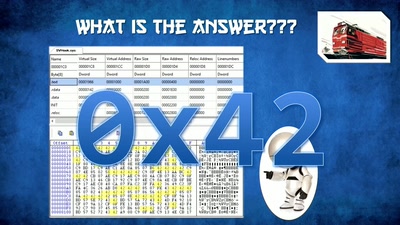
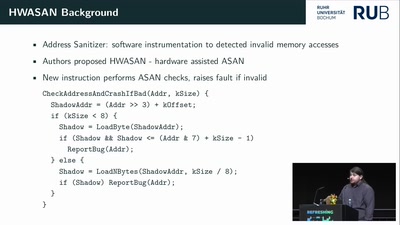
It is now 27 years since MS-DOS 5.0 was released. During its day there was the threat of viruses breaking your system or making it act in unpredictable ways. Due to its age and near total lack of consumer use it is safe to assume that all of the viruses for MS-DOS have been written. Using community archives and modern analysis methods we can uncover how they worked and reflect on how things have changed.
Computers have come a long way in the last 27 years, and so has malware too. This talk will start off with some of the most famous and widely known payloads. A basic guide on how MS-DOS runs applications, and we will work up from there to analysing all 17k+ samples with that are in the archives using automatic tooling to pick out some of the most interesting ones.
If you don’t have reverse engineering skills, don’t be afraid! We will start off with the basics of how the IBM PC works, MS DOS execution, binary runtime, and how we automatically run/disassemble/trace/fuzz malware on mass.
Download
Video
These files contain multiple languages.
This Talk was translated into multiple languages. The files available for download contain all languages as separate audio-tracks. Most desktop video players allow you to choose between them.
Please look for "audio tracks" in your desktop video player.