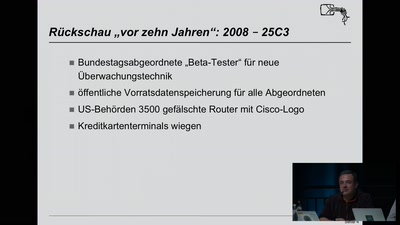
Every year since 2011 on the 28C3 we organize a Capture the Flag contest for people on the Congress and from all over the world. This year we want to give you an overview about what a CTF is, the challenges, the players, the community and how much fun it is to play (not only our) CTF.
Capture the Flag competitions started to become a thing in the infosec community more than 20 years ago. When we started playing they were casual games to improve our skill set every now and then on weekends with a bunch of friends. In recent years, the CTF community grew much bigger and nowadays you can play a CTF every weekend if you want to. So what is it all about?
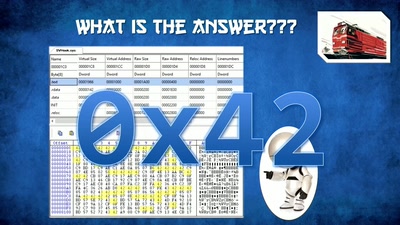
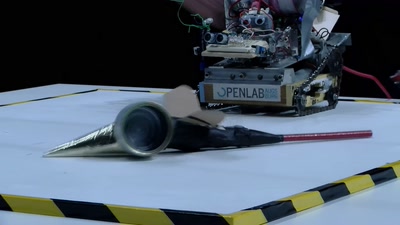
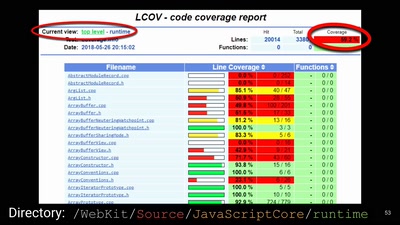
For the past 7 years, we organized the C3 CTF with a variety of challenges that try to be oriented towards real-world scenarios. The range of topics include reverse engineering, crypto(graphy) and web, and of course good old binary exploitation. If you solve a task, you get a flag. As simple as that. For the second time this year, we also run a separate, entry-level CTF designed for folks who do not like spending 48 hours on a single challenge. We are honored that over a thousand teams are playing with us every year from every corner of the world, and trolling our IRC channels.
We will present some challenges from this year's contest to give you an idea what you are up to when you decide to play. You will see how to solve our challenges even if you never played a CTF before. We realize that everybody needs to start somewhere and would love to motivate even more people to join our lovely community.
Download
Video
These files contain multiple languages.
This Talk was translated into multiple languages. The files available for download contain all languages as separate audio-tracks. Most desktop video players allow you to choose between them.
Please look for "audio tracks" in your desktop video player.