50 min
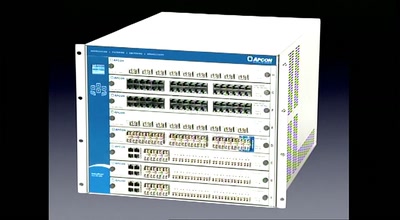
Solutions for monitoring and lawful interception within a…
39 min
implants, sensory extension and silicon - all for you!
57 min
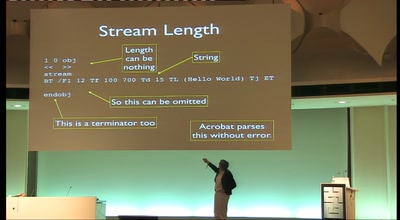
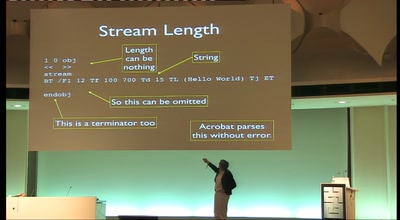
What you didn't know about Acrobat

55 min
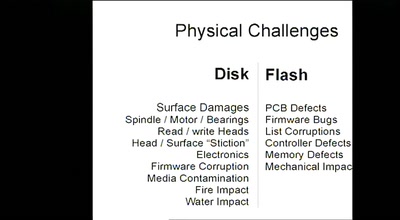
Mitigating cold-boot attacks for Full-Disk-Encryption…
58 min
Corporations enabling citizens to print digital money
57 min
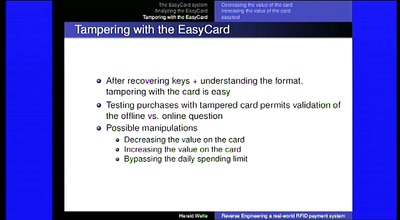
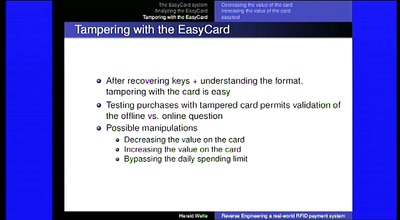
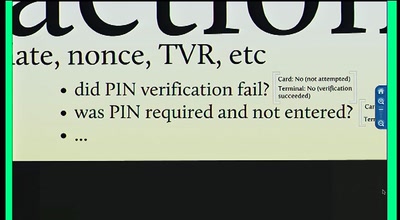
Vulnerabilities in the EMV Protocol
25 min
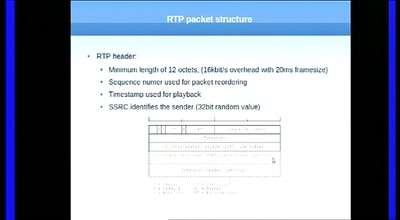
Source routing attacks applied to SIP
65 min
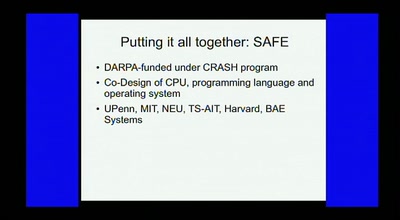
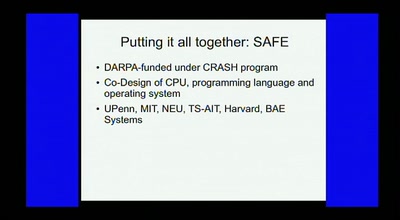
Applications of theorem proving for securing the windows…
61 min
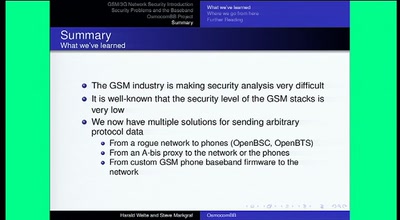
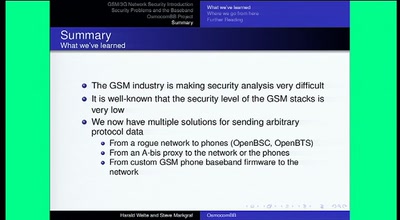
Introducing Project OsmocomBB
34 min
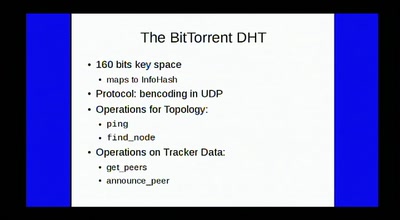
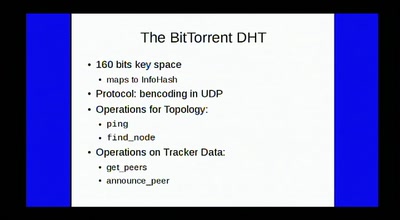
Nasty effects with tracker-less BitTorrent
51 min
3510 transistors in 60 minutes
64 min
Why we will have more secure computers - tomorrow
47 min
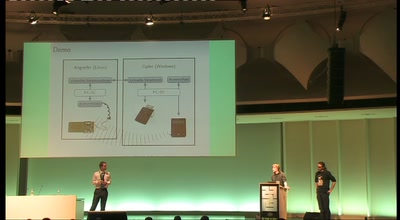
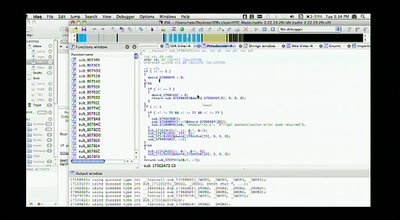
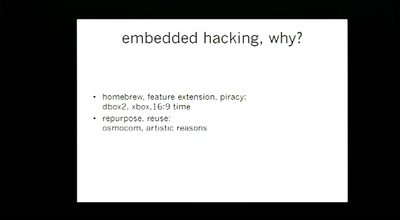
Backdooring Embedded Controllers
56 min
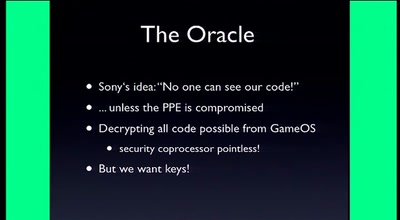
How we obtained the equivalent power of a Deep Crack for a…
62 min
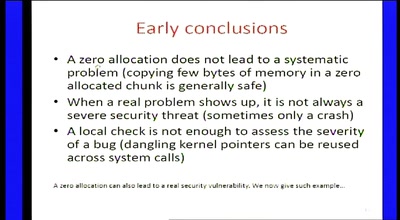
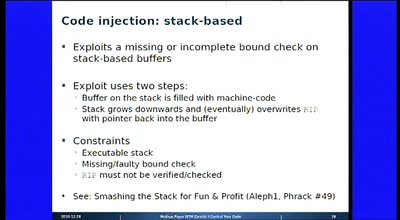
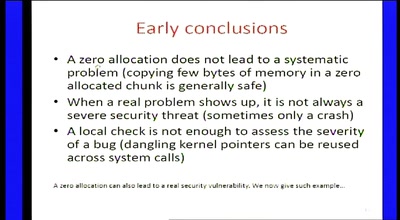
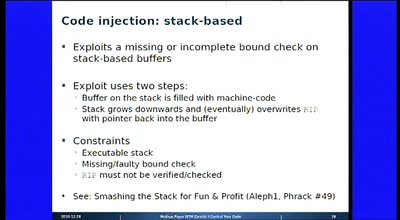
Attack Vectors Through the Eyes of Software-based Fault…

59 min
One year of Rocket Science!
57 min
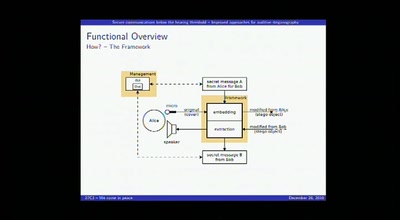
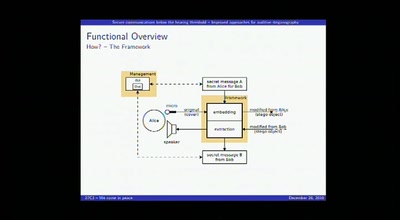
Improved approaches for auditive steganography
66 min
all your baseband are belong to us
61 min
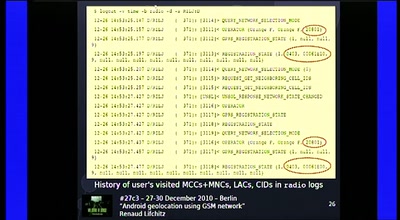
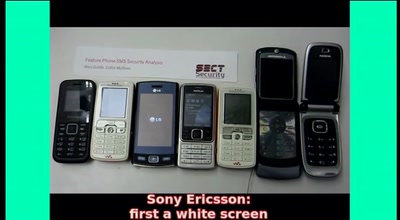
From analyzing to attacking mobile phones on a large scale.
54 min
On Using Anonymizers and Still Get Fucked
76 min
SAP Security and the Enterprise
73 min
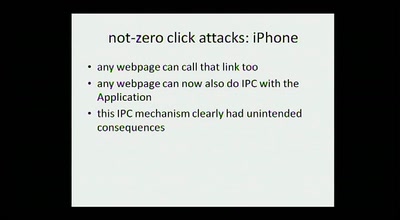
expanding the attack surface and then some
60 min
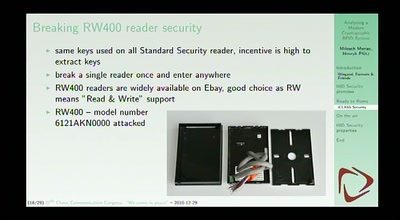
Besitz und Wissen: Relay-Angriffe auf den neuen…
56 min
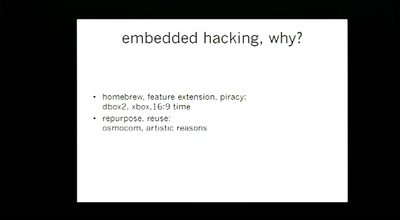
a dump of simple tools for embedded analysis at many layers