Search for "crypto" returned 406 results
101 min
DG73: Hacking with Care
Tactical and ethical care for all
69 min
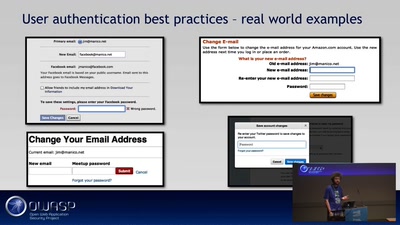
OWASP ProActive Controls
Sichere Anwendungen erstellen?
59 min
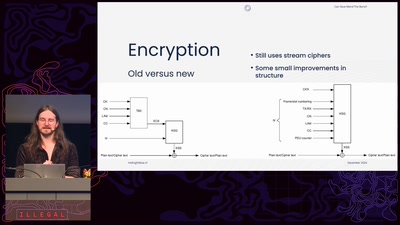
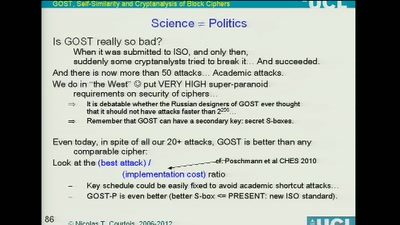
Security Evaluation of Russian GOST Cipher
Survey of All Known Attacks on Russian Government…

62 min
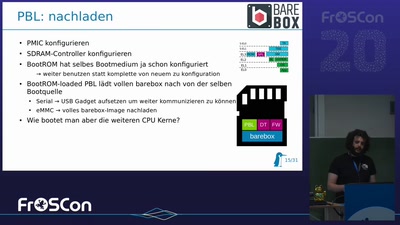
Gestatten: The Flash
Security von Embedded Systemen pimpen - Wieso? Weshalb? Wow!
57 min
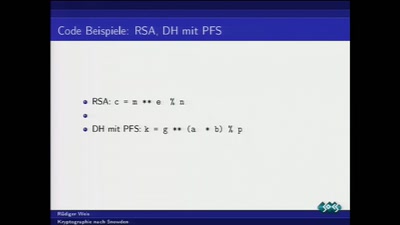
Kryptographie nach Snowden
Was tun nach der mittelmäßigen Kryptographie-Apokalypse?
69 min