Search for "Kat" returned 5621 results
60 min
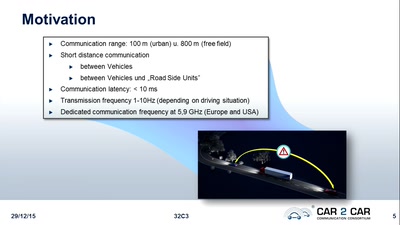
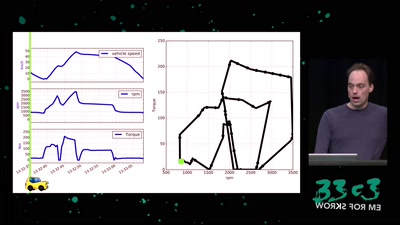
Software Defined Emissions
A hacker’s review of Dieselgate

41 min
Framing digital industry into planetary limits and transition policies
The environmental costs of digital industry and pathways to…
31 min
The Economic Consequences of Internet Censorship
Why Censorship is a Bad Idea for Everyone
60 min
Why is GPG "damn near unusable"?
An overview of usable security research

46 min
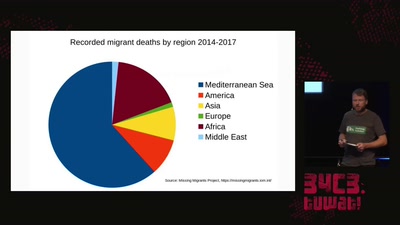
The Mission of the MV Louise Michel
"Feminism will be anti-racist or it won´t be"
32 min
The seizure of the Iuventa
How search and rescue in the mediterranean was criminalized

60 min
Attacking end-to-end email encryption
Efail, other attacks and lessons learned.
62 min
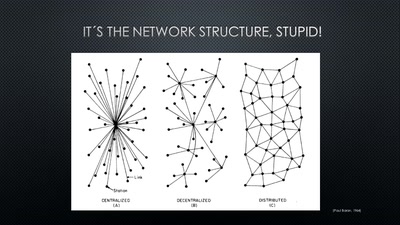
A New Kid on the Block
Conditions for a Successful Market Entry of Decentralized…
31 min
BGP and the Rule of Custom
How the internet self-governs without international law
30 min
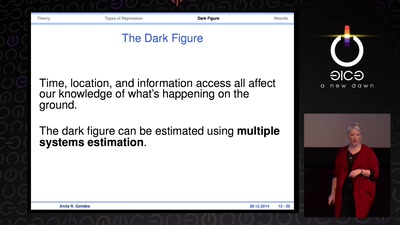
Information Control and Strategic Violence
How governments use censorship and surveillance as part of…
59 min
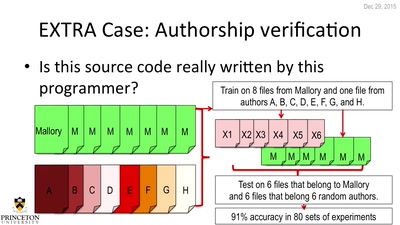
De-anonymizing Programmers
Large Scale Authorship Attribution from Executable Binaries…
60 min
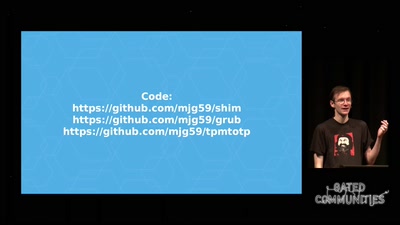
Beyond Anti Evil Maid
Making it easier to avoid low-level compromise, and why…

56 min
Reality Check! Basel/Lagos?? In virtual reality?
An African tale of art, culture and technology
31 min
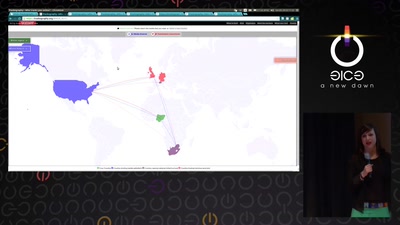
Trackography
You never read alone
32 min