Search for "Adam Wight"
prev
next
61 min
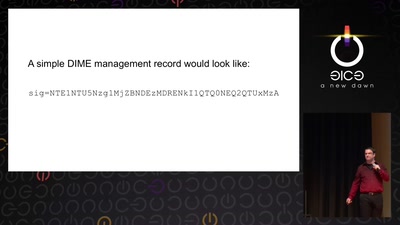
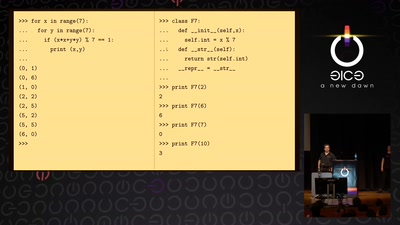
Internet reengineering session
55 min
A gentle introduction to elliptic-curve cryptography
53 min
Uncovering Nation-State Mobile Espionage in the Wild
33 min
50 most unwanted retail surveillance technologies / 50 most…
45 min
Hacking industrial control gateways
33 min
What can be done to protect the term, the notion and the…
46 min
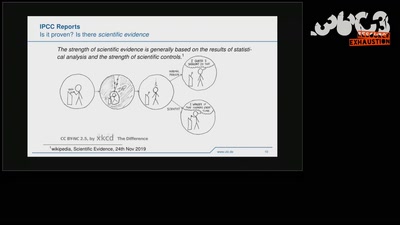
The Science Behind Climate Reports
43 min
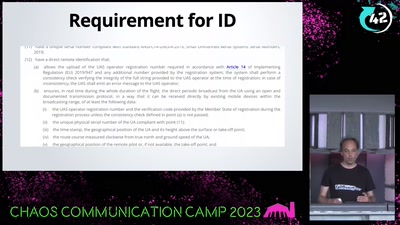
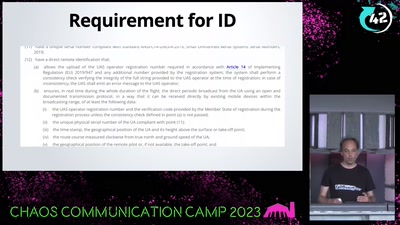
A hacker's view at commercial drone security

58 min
What You Get When Attack iPhones of Researchers

30 min
Afrofuturism, Telling tales of speculative futures
46 min
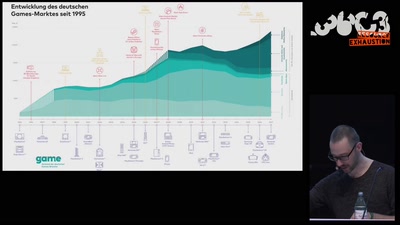
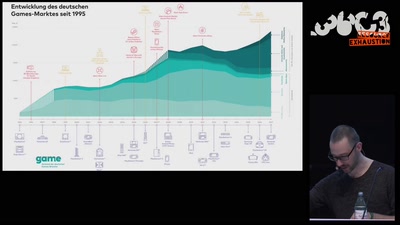
Wie die radikale Rechte (ihre) Politik gamifiziert
29 min
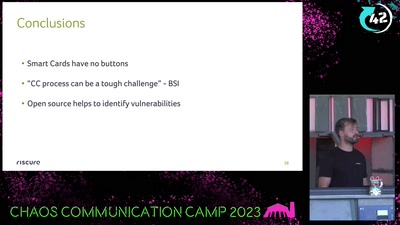
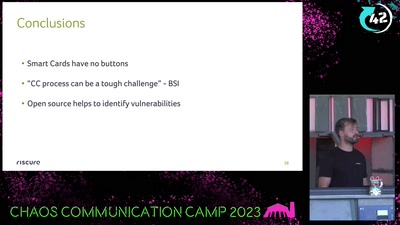
Attacking an opensource U2F device in 30 minutes or less
32 min
Approaches to working with sound and network data…
prev
next