Search for "Lisa" returned 990 results
64 min
"Exploit" in theater
post-existentialism is the question, not post-privacy
39 min
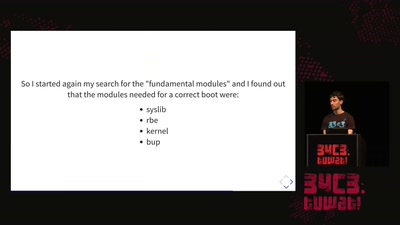
Tales of old: untethering iOS 11
Spoiler: Apple is bad at patching
60 min
Concepts for global TSCM
getting out of surveillance state mode
56 min
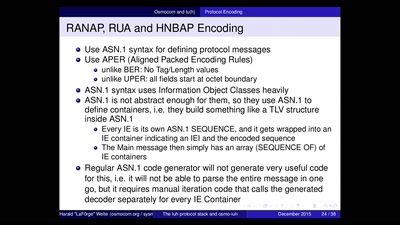
Running your own 3G/3.5G network
OpenBSC reloaded
59 min
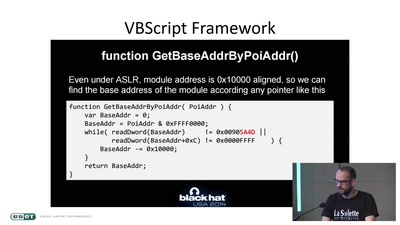
Visiting The Bear Den
A Journey in the Land of (Cyber-)Espionage

68 min
#afdwegbassen: Protest, (Club-)Kultur und antifaschistischer Widerstand
Über kreative Organisation, poltische Aktionen und das…
72 min
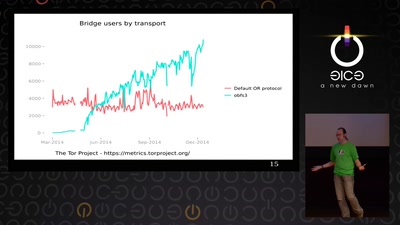
State of the Onion
Neuland
47 min
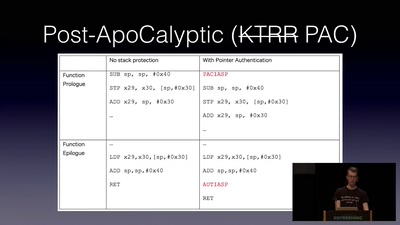
Jailbreaking iOS
From past to present
31 min
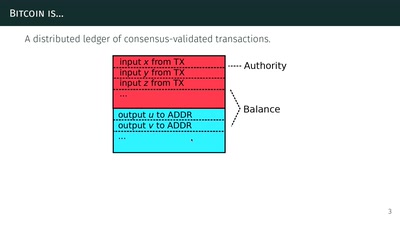
The Zcash anonymous cryptocurrency
or zero-knowledge succinct non-interactive arguments of…
61 min
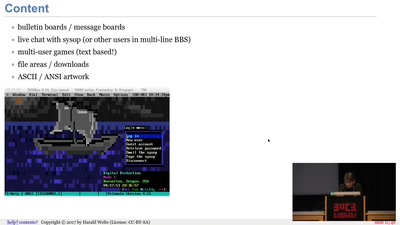
BBSs and early Internet access in the 1990ies
Modems, FIDO, Z-Netz, Usenet, UUCP, SLIP and ISDN
43 min
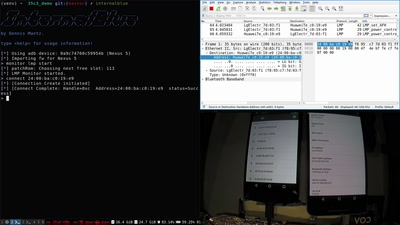
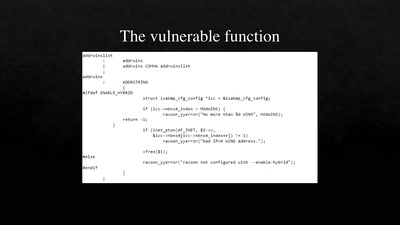
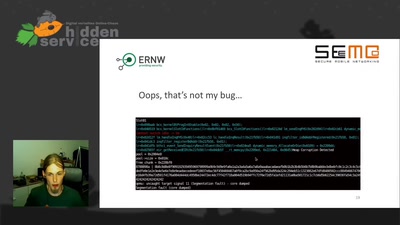
No PoC? No Fix! - A sad Story about Bluetooth Security
It is just a broken memcpy in the Bluetooth stack. Do we…
32 min