Search for ".had" returned 5540 results
47 min
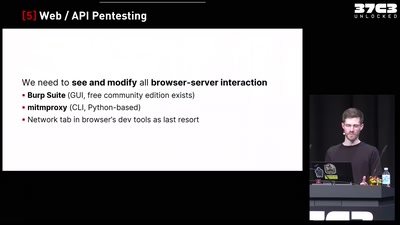
Finding Vulnerabilities in Internet-Connected Devices
A Beginner’s Guide

56 min
Household, Totalitarianism and Cyberspace
Philosophical Perspectives on Privacy Drawing on the…
57 min
TrustZone-M(eh): Breaking ARMv8-M's security
Hardware attacks on the latest generation of ARM Cortex-M…
60 min
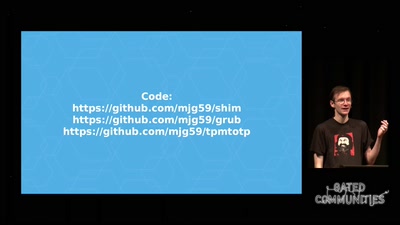
Beyond Anti Evil Maid
Making it easier to avoid low-level compromise, and why…
29 min
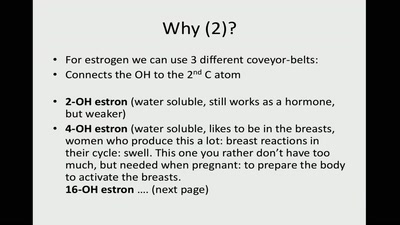
Hormones and Hysteria - what every person should know
are you not curious now? ;)
60 min

![TVLuke: Touch Board und Conductive Paint [FreiTalk N8]](https://static.media.ccc.de/media/regional/luebeck/chaotikum/190215597-16d598db-96cb-4214-9a6f-c7db49dd37d2.jpg)