Search for "tor" returned 10373 results

43 min
The ecosystem is moving
Challenges for distributed and decentralized technology…
48 min
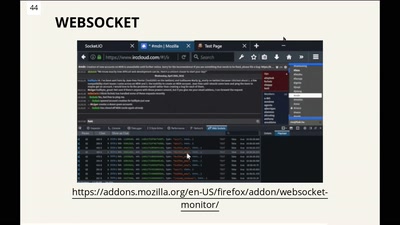
Demolish the web with the Firefox Dev Tools!
Do you know what you can do with Firefox for frontend…
42 min
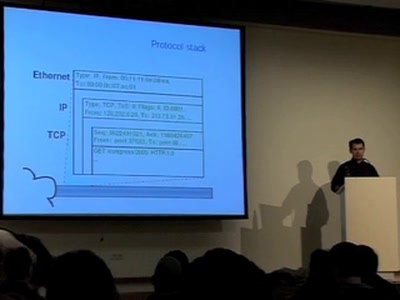
Covert channels in TCP/IP: attack and defence
Creation and detection of IP steganography for covert…
55 min
Graphs, Drones & Phones
The role of social-graphs for Drones in the War on Terror.
43 min
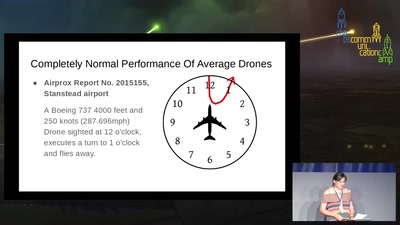
The Great British Drone Panic
Asking for better standards of official investigation and…
40 min
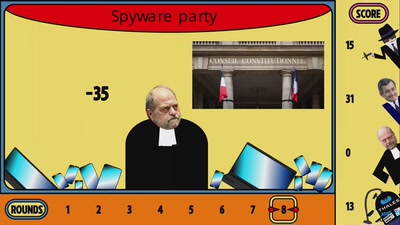
A year of surveillance in France: a short satirical tale by La Quadrature du Net
From the so-called Country of human rights to a…
25 min
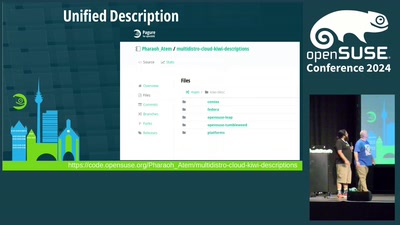
Sweetening heterogeneous Linux deployments in the Cloud with KIWI
Using KIWI to easily support multiple distributions in the…
50 min
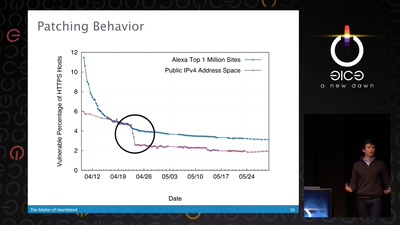
The Matter of Heartbleed
What went wrong, how the Internet reacted, what we can…

53 min
Offshoreleaks - the how and why of a global investigation
How we tried to prove tax evasion and money laundering…

58 min
Counterlobbying EU institutions
How to attempt to counter the influence of industry…
29 min
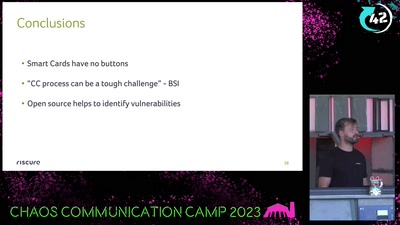
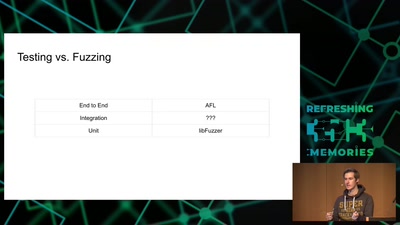
What de.fac2?
Attacking an opensource U2F device in 30 minutes or less
54 min
Attacking Chrome IPC
Reliably finding bugs to escape the Chrome sandbox
43 min
Artist Talk
We Show You What You Want To See
35 min
Weaponized Social
Understanding and tools to mitigate network-scale violences

41 min
MySQL Plugins - what are they ?
how can you use them to do wonders
28 min
Hardware attacks: hacking chips on the (very) cheap
How to retrieve secret keys without going bankrupt

30 min
Mobile devices and openSUSE, is it posible?
It is time to check if we can use a mobile device with a…
24 min
Security alerting made easy using Python
Sending real-time notifications to Discord and other…
27 min