Search for "Ben H." returned 5952 results

9 min
Identitätsbildung bei Persona 5 Royal
Über das Seele-Kultur-Problem mit Persona 5 Royal

32 min
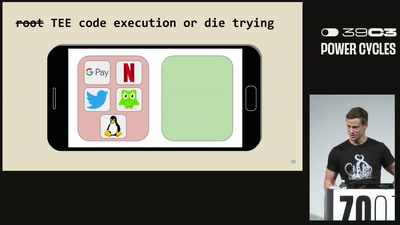
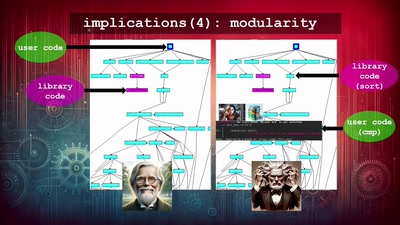
Finding the Weak Crypto Needle in a Byte Haystack
Automatic detection of key-reuse vulnerabilities
39 min


![Malte über den Halbgeviertstrich [5 Minuten Termine]](https://static.media.ccc.de/media/regional/luebeck/chaotikum/887-C4AA30D6-E3E8-434A-B754-D927F4C8108E.jpg)






![Thomas über den Energieverbrauch einer privaten Nextcloud-Instanz [5 Minuten Termine]](https://static.media.ccc.de/media/regional/luebeck/chaotikum/1451-06030a32-b6c3-4998-b8f7-b7fd8be472e2.jpg)
![NeoRaider über Linux User-Namespaces und den unshare-Befehl [5 Minuten Termine]](https://static.media.ccc.de/media/regional/luebeck/chaotikum/1350-1fc7db56-5c9d-452b-ad51-b43894f77c42.jpg)