Search for "tor" returned 10358 results

44 min
Open Source Machine Translation
From tools, to tricks, to projects: build a translation…
29 min
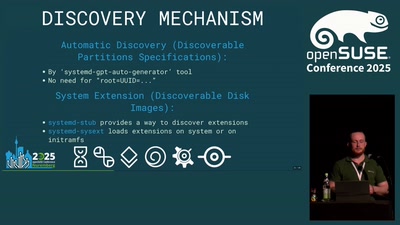
The Unified Kernel Image in openSUSE distribution
How to secure the initramfs
29 min
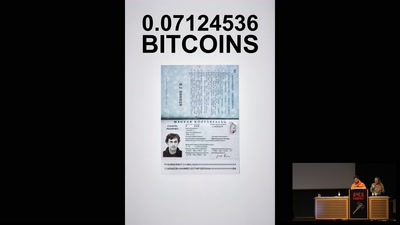
Ecstasy 10x yellow Twitter 120mg Mdma
Shipped from Germany for 0.1412554 Bitcoins
15 min
Build yourself a SNMP replacement
And make SSH pay for it
45 min
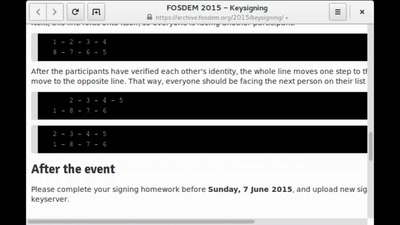
Two decades later - Keysigning in the 2000s
Micro keysigning parties for the masses

61 min
Yes we can! Yes we will!
Free Software for a new society

76 min
Trustbased P2P exchange on the semantic web and the WYMIWYG KnoBot project
An agent for decentralised knowledge exchange

56 min
"The Concert"
a disconcerting moment for free culture
51 min
The GNU Name System
A Decentralized PKI For Social Movements

47 min
Software Patenting
Adequate means of protection for software.
65 min
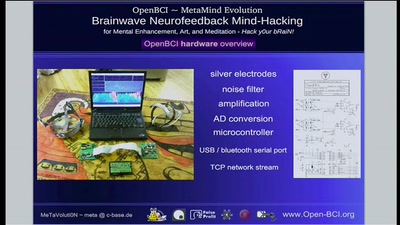
Quantified-Self and OpenBCI Neurofeedback Mind-Hacking
Transhumanism, Self-Optimization and Neurofeedback for…

34 min
Digital Musical Instruments
Evolution and design of new interfaces for musical…
36 min
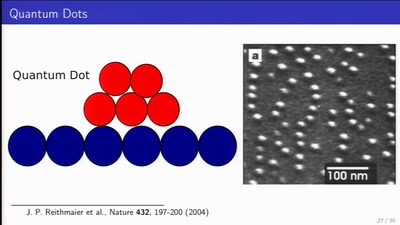
Long Distance Quantum Communication
Concepts and components for intercontinal communication…
64 min
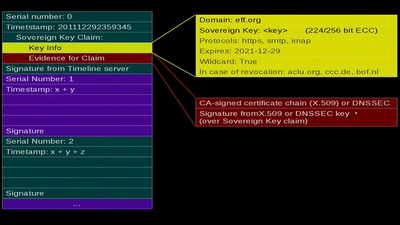
Sovereign Keys
A proposal for fixing attacks on CAs and DNSSEC

55 min
FrozenCache
Mitigating cold-boot attacks for Full-Disk-Encryption…
59 min
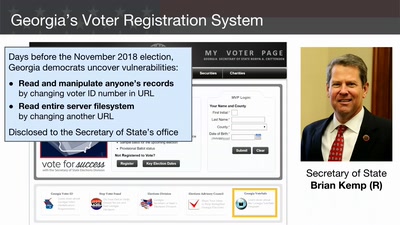
Election Cybersecurity Progress Report
Will the U.S. be ready for 2020?
63 min
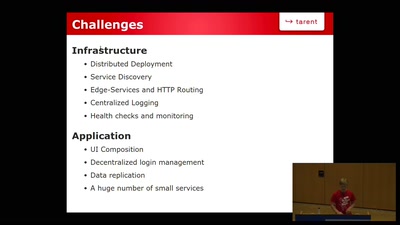
Microservice Toolbox
Building blocks for your next microservice platform
60 min
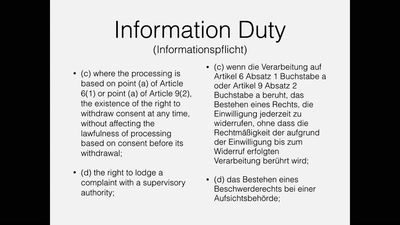
General Data Protection Regulation is coming
What does it mean for your software?

64 min
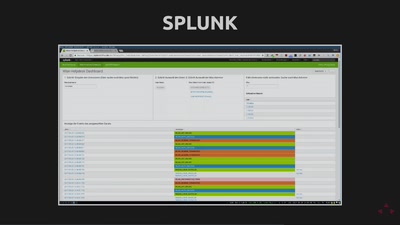
Who can you trust?
A trust metric for the openSUSE buildservice
41 min
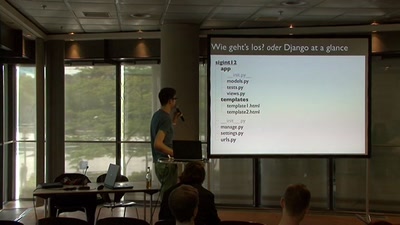
Einführung in Django
"The Web Framework for perfectionists with deadlines."
147 min
Hacker Jeopardy
Zahlenraten für Geeks [Number guessing for geeks]
58 min
Thwarting Evil Maid Attacks
Physically Unclonable Functions for Hardware Tamper…
60 min
Check your privileges!
How to drop more of your privileges to reduce attack…
30 min
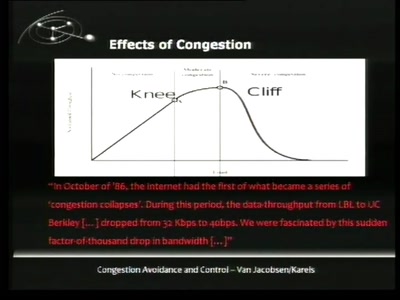
TCP Denial of Service Vulnerabilities
Accepting the Partial Disclosure Challenge

58 min