Search for "Ari" returned 5363 results
62 min
Cellular protocol stacks for Internet
GPRS, EDGE, UMTS, HSPA demystified
65 min
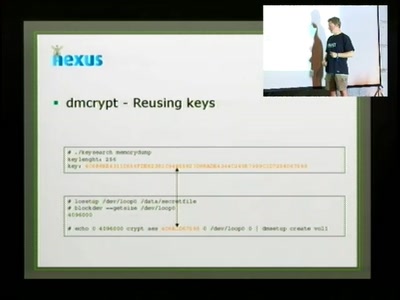
Cryptographic key recovery from Linux memory dumps
Does dm-crypt and cryptoloop provide expected security when…
38 min
Quantum Entanglement
An introduction
57 min
Why favour Icinga over Nagios?
How we think enterprise-grade open source monitoring works

50 min
coreboot: Beyond The Final Frontier
Open source BIOS replacement with a radical approach to…
52 min
Void the warranty!
How to start analyzing blackboxes
56 min
Hacking ideologies, part 2: Open Source, a capitalist movement
Free Software, Free Drugs and an ethics of death

32 min
Cryptokids
empower kids and provide tools for them to be more secure…

61 min
The Invisible Committee Returns with "Fuck Off Google"
Cybernetics, Anti-Terrorism, and the ongoing case against…
61 min
How to Hack Your Way to Space
Bringing the Hacker Mindset to the Space Ecosphere - The…
57 min
The Precariat: A Disruptive Class for Disruptive Times.
Why and How the Precariat will define the Global…
29 min