Search for "sven" returned 2155 results
66 min
31C3 Keynote
A New Dawn
60 min
Why is GPG "damn near unusable"?
An overview of usable security research

60 min
My Robot Will Crush You With Its Soft Delicate Hands!
How to design and fabricate soft robots using everyday…
60 min
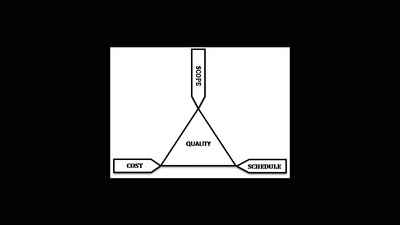
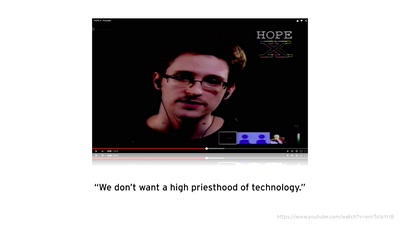
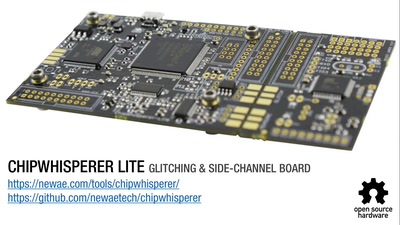
Opening Closed Systems with GlitchKit
'Liberating' Firmware from Closed Devices with Open Source…
60 min
G’scheitern
The art of failure taught by improv theatre

61 min
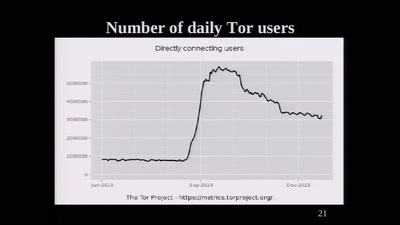
Ten years after ‚We Lost The War‘
The future does not look much brighter than ten years ago.…
30 min
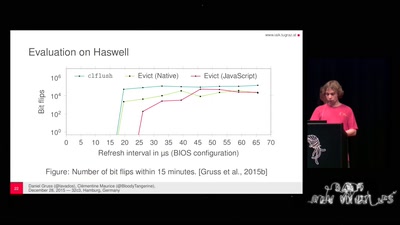
Rowhammer.js: Root privileges for web apps?
A tale of fault attacks on DRAM and attacks on CPU caches
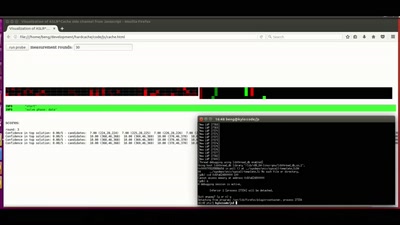
44 min
ASLR on the line
Practical cache attacks on the MMU
61 min
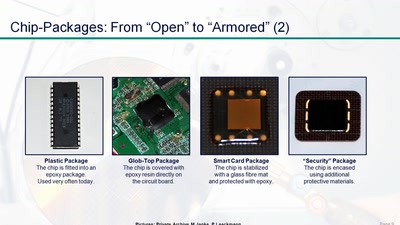
Uncaging Microchips
Techniques for Chip Preparation
65 min
35C3 Infrastructure Review
Up and to the right: All the statistics about this event…
38 min
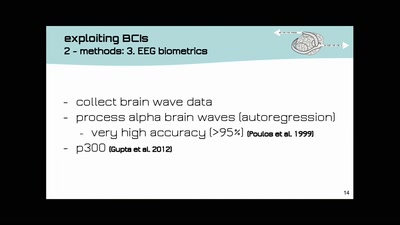
Open-BCI DIY-Neuroscience Maker-Art Mind-Hacking
open source DIY brain-computer-interfaces | technology and…
35 min
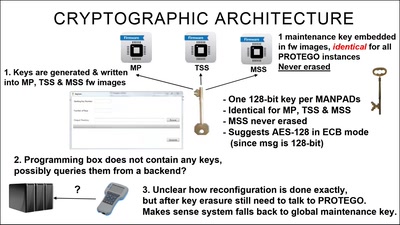
Harry Potter and the Not-So-Smart Proxy War
Taking a look at a covert CIA virtual fencing solution
48 min
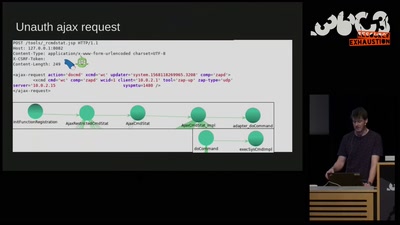
Don't Ruck Us Too Hard - Owning Ruckus AP Devices
3 different RCE vulnerabilities on Ruckus Wireless access…

32 min
Finding the Weak Crypto Needle in a Byte Haystack
Automatic detection of key-reuse vulnerabilities
62 min