Search for "sap" returned 2957 results

46 min
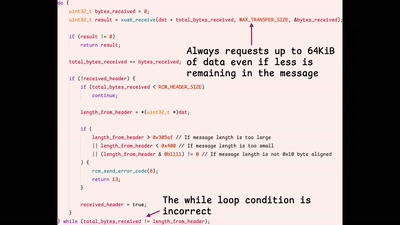
SELECT code_execution FROM * USING SQLite;
--Gaining code execution using a malicious SQLite database
49 min
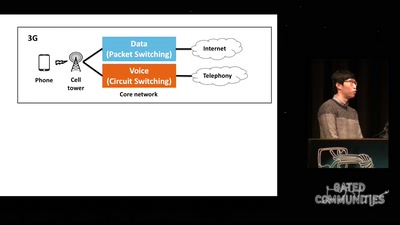
Dissecting VoLTE
Exploiting Free Data Channels and Security Problems
53 min
DG112: Wer hat den kleinsten Anhang?
Erste Hilfe für sinnvolle Mediendateigrößen

58 min
Uncertain Concern
How Undocumented Immigrants in the US Navigate Technology
65 min
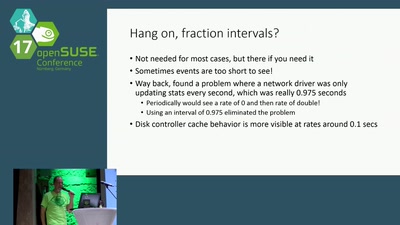
collectl - a system monitoring tool like no other
Collectl is a comprehensive, fine-grained monitoring tool…
25 min
Saving the World with Space Solar Power
or is it just PEWPEW?!
36 min