Search for "Sec" returned 2748 results

32 min
Finding the Weak Crypto Needle in a Byte Haystack
Automatic detection of key-reuse vulnerabilities
60 min
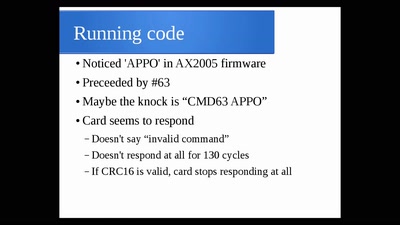
The Exploration and Exploitation of an SD Memory Card
by xobs & bunnie
60 min
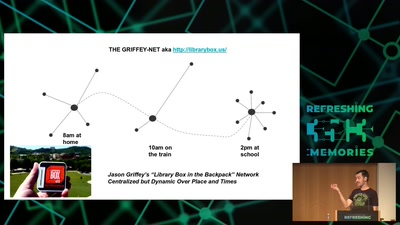
Wind: Off-Grid Services for Everyday People
Integrating nearby and offline connectivity with the…
41 min
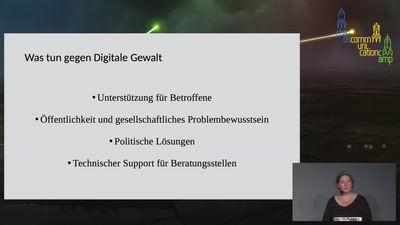
Was tun gegen Digitale Gewalt gegen Frauen
"Nicht dem Phänomen Cybercrime im engeren Sinne zuzuordnen"…

34 min
Lightning Talks I
Routenplanung durch Flächen - Interaktive Visualisierung…

54 min
Understanding and fixing cross-compilation requirements
How to make your FOSS project cross-compilation friendly
36 min
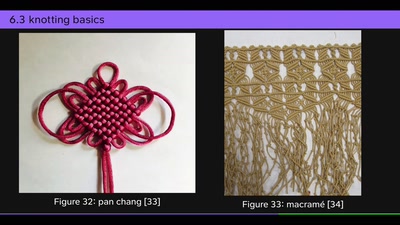
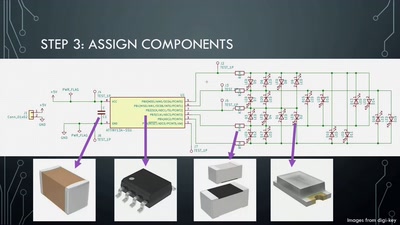
Artistic PCB Design and Fabrication
From doodle to manufacture: how I make mechanically…
58 min
Firebird Open Source Database Quick Start
Why Firebird is a powerful alternative database system
41 min
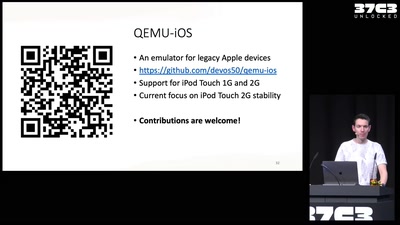
Breathing Life into Legacy: An Open-Source Emulator of Legacy Apple Devices
A Dive into Reverse Engineering and Understanding the iPod…
53 min
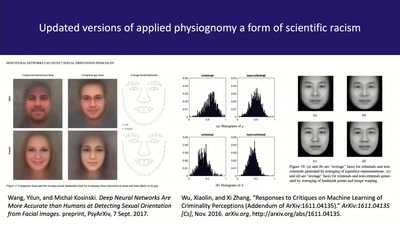
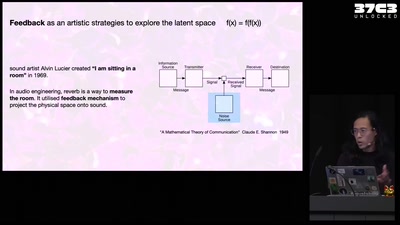
Self-cannibalizing AI
Artistic Strategies to expose generative text-to-image…
58 min
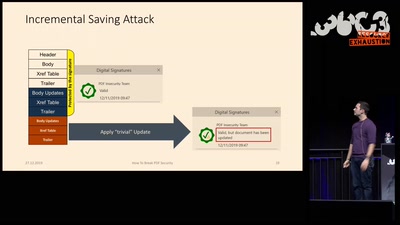
How to Break PDFs
Breaking PDF Encryption and PDF Signatures
41 min
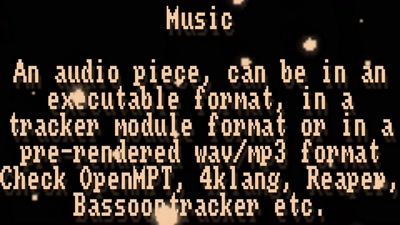
Demoscene now and then
The demoscene is an underground computer art culture.
63 min
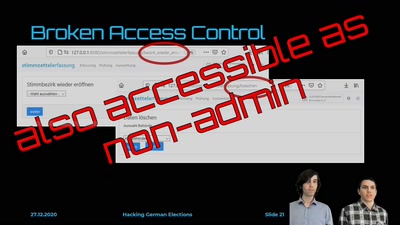
Hacking German Elections
Insecure Electronic Vote Counting - How It Returned and Why…
40 min
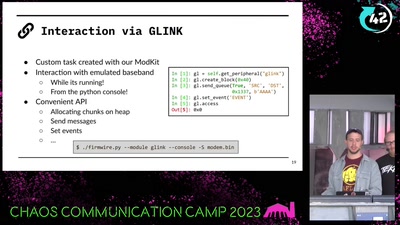
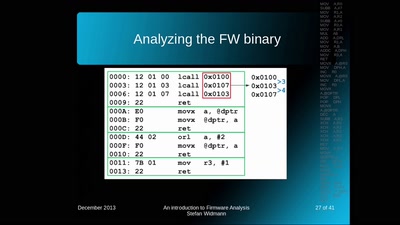
An introduction to Firmware Analysis
Techniques - Tools - Tricks
44 min
Why Nobody cares, and only You can save the World
Technology, Intuitions & Moral Expertise
61 min