Search for "Takt" returned 1939 results
61 min
Untrusting the CPU
A proposal for secure computing in an age where we cannot…
53 min
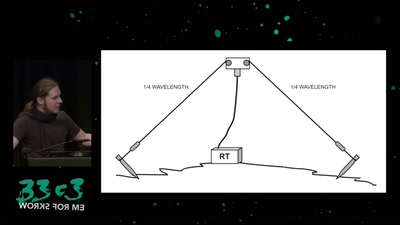
Surveilling the surveillers
About military RF communication surveillance and other…
30 min
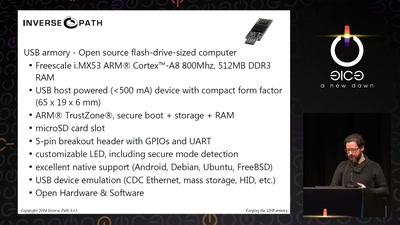
Forging the USB armory
Creating an open source secure flash-drive-sized computer
58 min
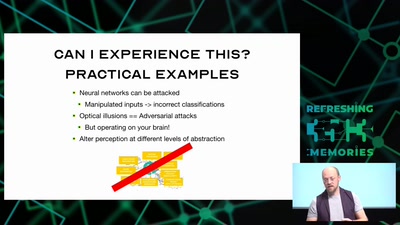
Hacking how we see
A way to fix lazy eye?
38 min
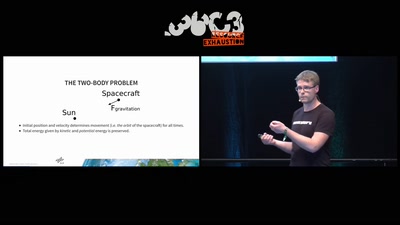
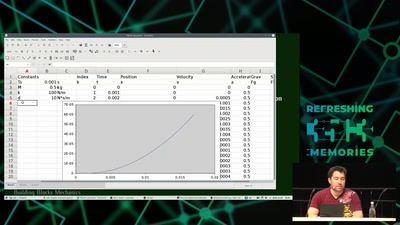
Modeling and Simulation of Physical Systems for Hobbyists
Essential Tools for Developing, Testing and Debugging…
33 min
Hacking as Artistic Practice
!Mediengruppe Bitnik about their recent works

32 min
Finding the Weak Crypto Needle in a Byte Haystack
Automatic detection of key-reuse vulnerabilities
38 min
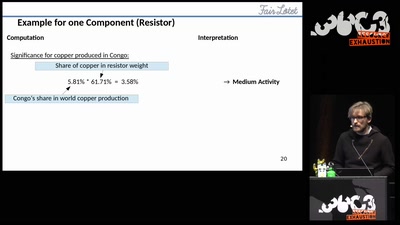
Fairtronics
A Tool for Analyzing the Fairness of Electronic Devices
28 min
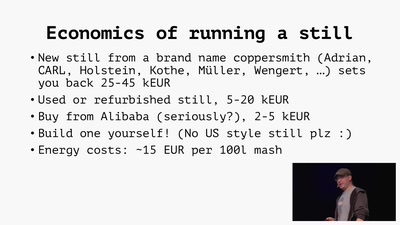
Home Distilling
Theory and practice of moonshining and legal distilling
32 min
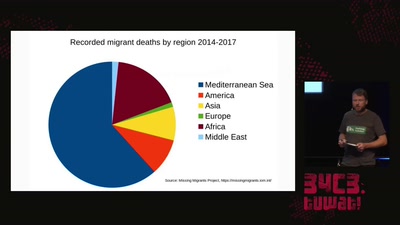
The seizure of the Iuventa
How search and rescue in the mediterranean was criminalized
72 min
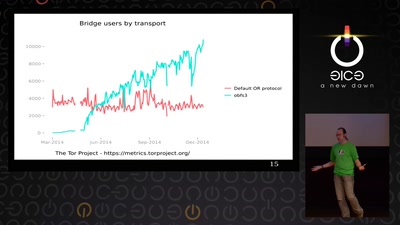
State of the Onion
Neuland
59 min
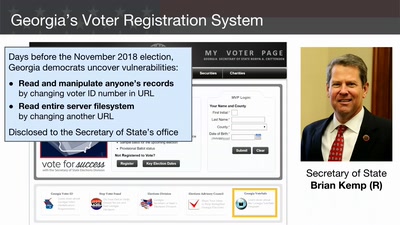
Election Cybersecurity Progress Report
Will the U.S. be ready for 2020?
42 min
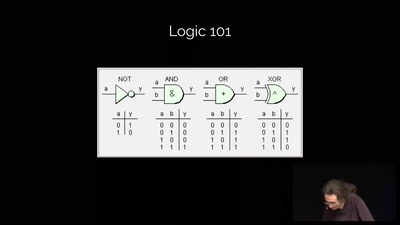
Reverse engineering FPGAs
Dissecting FPGAs from bottom up, extracting schematics and…
32 min
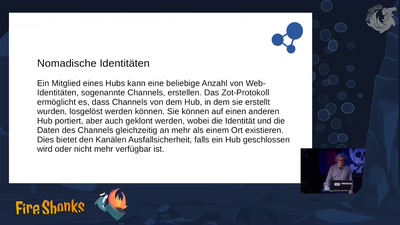
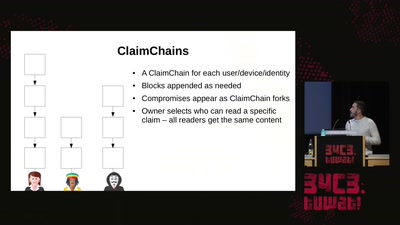
Modern key distribution with ClaimChain
A decentralized Public Key Infrastructure that supports…
58 min