Search for "AKO" returned 1184 results
53 min
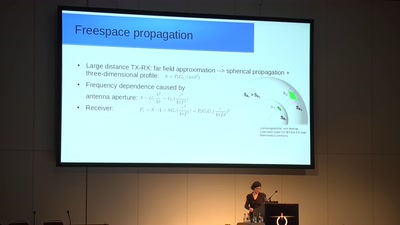
From Maxwell to antenna arrays
How 150 year old equations still help to communicate
44 min
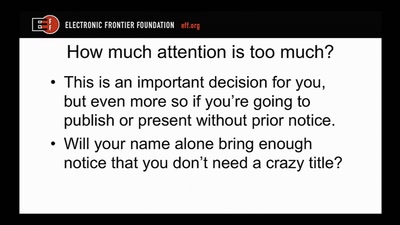
Disclosure DOs, Disclosure DON'Ts
Pragmatic Advice for Security Researchers
46 min
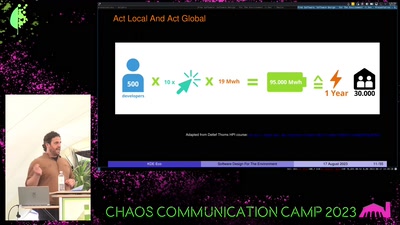
Free Software
Software Design For The Environment
62 min
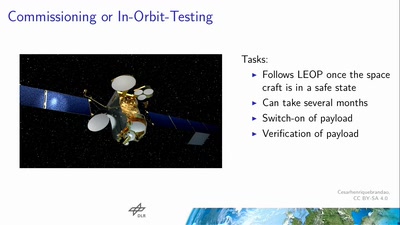
Space Ops 101
An introduction to Spacecraft Operations

54 min
A la recherche de l'information perdue
some technofeminist reflections on Wikileaks
38 min
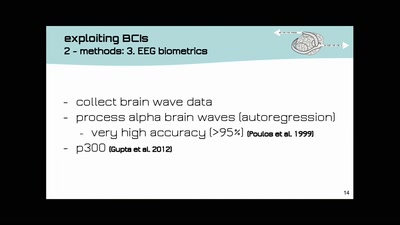
Open-BCI DIY-Neuroscience Maker-Art Mind-Hacking
open source DIY brain-computer-interfaces | technology and…
44 min
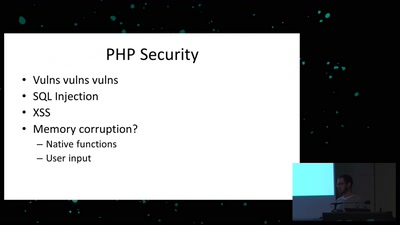
Exploiting PHP7 unserialize
teaching a new dog old tricks
49 min
C2X: The television will not be revolutionized.
From Cyberfeminism to XenoFeminism
31 min
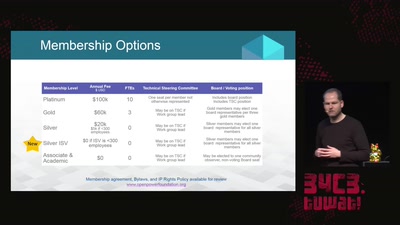
openPower - the current state of commercial openness in CPU development
is there no such thing as open hardware?
59 min
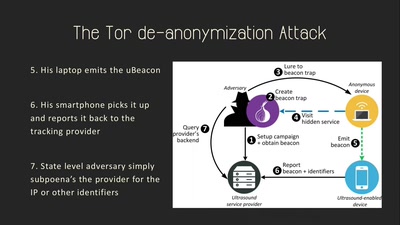
Talking Behind Your Back
On the Privacy & Security of the Ultrasound Tracking…

33 min
Open source experimental incubator build up
call for participation in project and product development

34 min
Scuttlebutt
The decentralized P2P gossip protocol
22 min
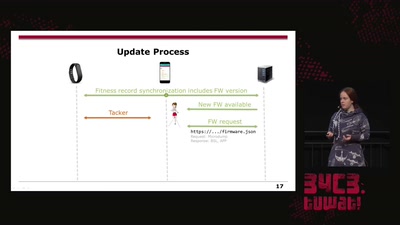
Doping your Fitbit
On Fitbit Firmware Modifications and Data Extraction
42 min