Search for "Lisa" returned 990 results
30 min
On Computing Numbers, with an Application to Problems of our Society
Journalism ♥ Computer Science
35 min
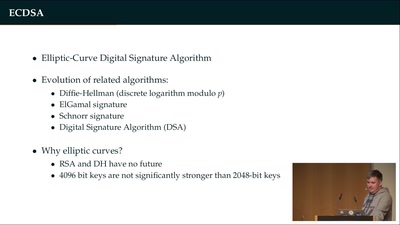
Wallet Security
How (not) to protect private keys
64 min
3 Years After Snowden: Is Germany fighting State Surveillance?
A Closer Look at the Political Reactions to Mass…
61 min
Programming FPGAs with PSHDL
Let's create the Arduino for FPGAs
44 min
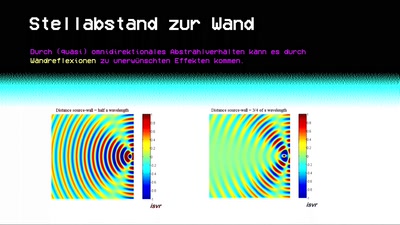
Sonic Alchemy
Mehr als nur Lärm: Ein Sprint vom kleinen Audio-Einmaleins…

46 min
Sendezentrum: Who Killed The Internet?
And a promising alternative for Public Communication and…
64 min
On the Security and Privacy of Modern Single Sign-On in the Web
(Not Only) Attacks on OAuth and OpenID Connect
60 min
Why is GPG "damn near unusable"?
An overview of usable security research
63 min
Human Rights at a Global Crossroads
Whistleblowers and the Cases of The Snowden Refugees and…

59 min
Security of the IC Backside
The future of IC analysis

40 min
Das Mauern muss weg
Best of Informationsfreiheit
27 min
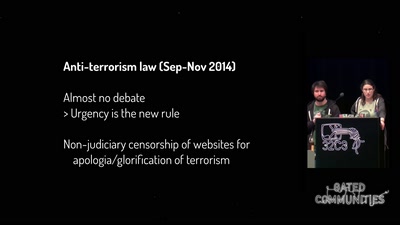
One year of securitarian drift in France
From the Bill on Intelligence to the State of Emergency
26 min
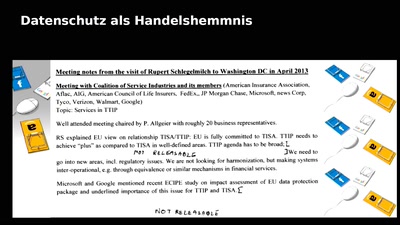
Technomonopolies
How technology is used to subvert and circumvent…
64 min
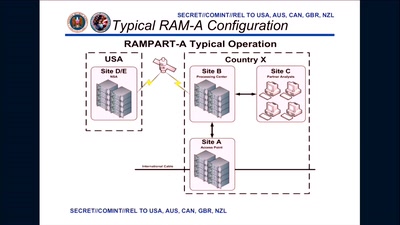
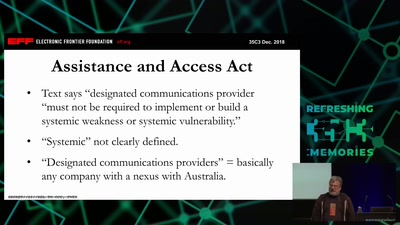
It Always Feels Like the Five Eyes Are Watching You
Five Eyes’ Quest For Security Has Given Us Widespread…

61 min
Correcting copywrongs
European copyright reform is finally on the horizon
62 min