Search for "Kat" returned 5621 results

46 min
SELECT code_execution FROM * USING SQLite;
--Gaining code execution using a malicious SQLite database
60 min
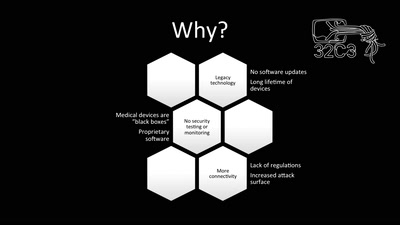
Unpatchable
Living with a vulnerable implanted device
32 min
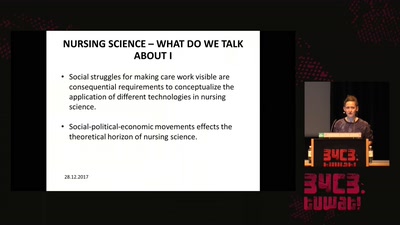
Think big or care for yourself
On the obstacles to think of emergent technologies in the…

22 min
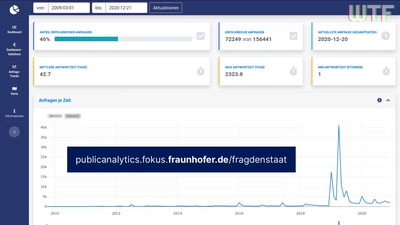
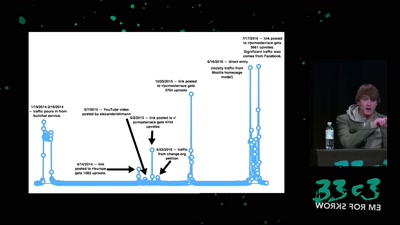
Trust us and our business will expand!
Net-activism strategies against fake web companies
58 min
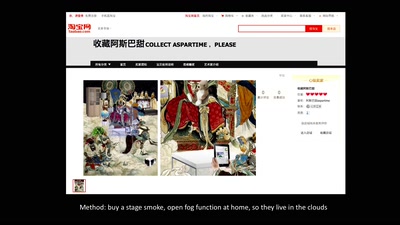
CHINTERNET ART
Creativity, Archives & Digital Media from the Chinese…
45 min
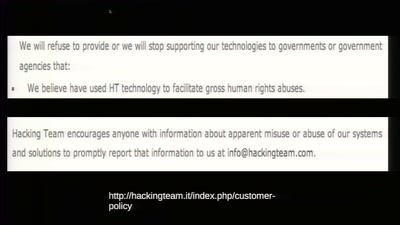
To Protect And Infect
The militarization of the Internet
55 min
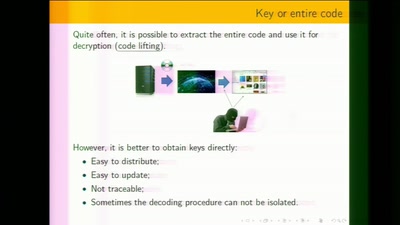
White-Box Cryptography
Survey
56 min
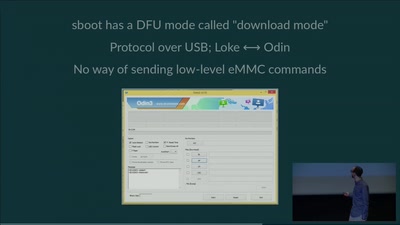
eMMC hacking, or: how I fixed long-dead Galaxy S3 phones
A journey on how to fix broken proprietary hardware by…
57 min
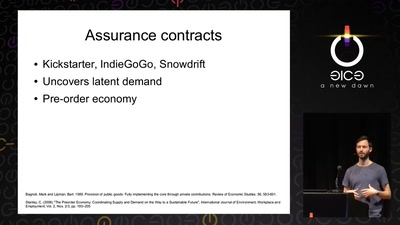
The Precariat: A Disruptive Class for Disruptive Times.
Why and How the Precariat will define the Global…
55 min
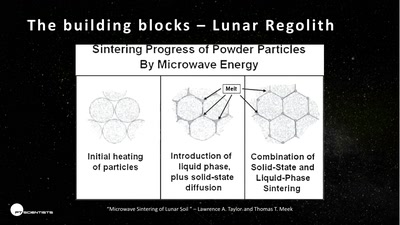
3D printing on the moon
The future of space exploration
46 min
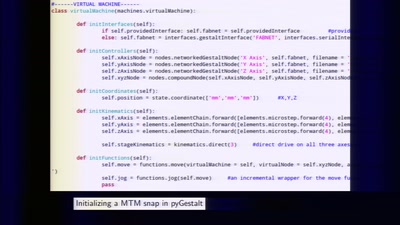
Making machines that make
rapid prototyping of digital fabrication and…
34 min
Ling - High level system programming
modular and precise resource management
30 min
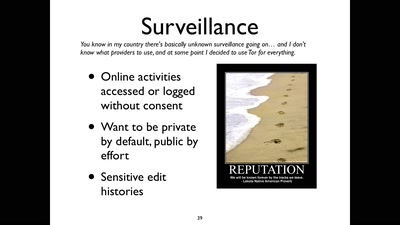
Privacy and Consumer Markets
Reversing the Surveillance Business Model

39 min
The Eye on the Nile
Egypt's Civil Society Under Attack
33 min
Turing Complete User
What can be done to protect the term, the notion and the…
62 min
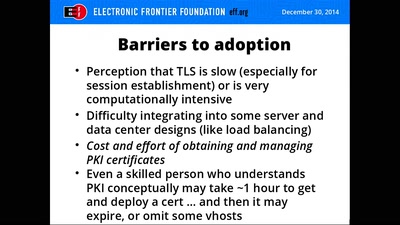
Let's Encrypt
A Free Robotic Certificate Authority
59 min
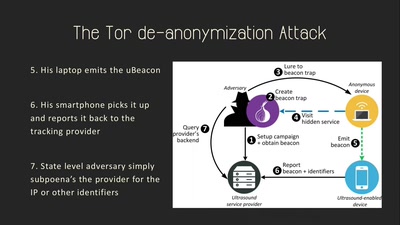
Talking Behind Your Back
On the Privacy & Security of the Ultrasound Tracking…
31 min