Search for "Ray" returned 3360 results

39 min
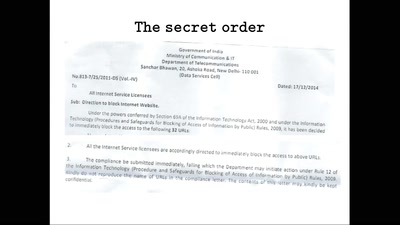
The Eye on the Nile
Egypt's Civil Society Under Attack

31 min
Buffered Daemons
Sound art performance exploring the concept of translation…
60 min
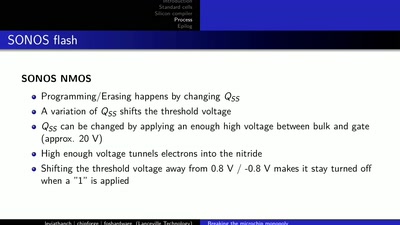
LibreSilicon
Decentralizing semiconductor manufacturing
29 min
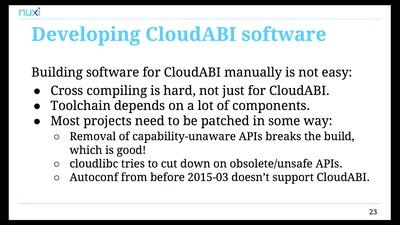
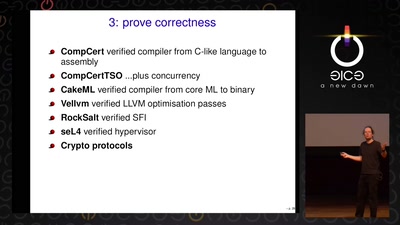
Infocalypse now: P0wning stuff is not enough
Several failure modes of the hacker scene
55 min
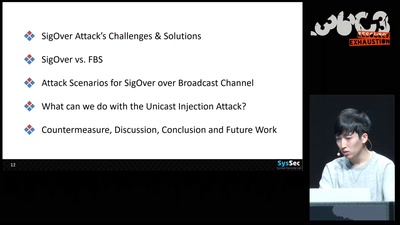
SigOver + alpha
Signal overshadowing attack on LTE and its applications
30 min
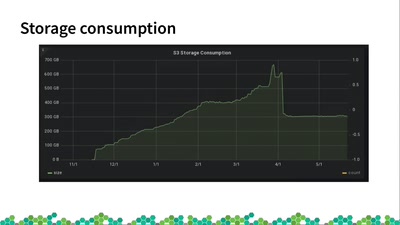
Tumbleweed Snapshots: Rolling With You
The missing link between fixed and rolling releases
40 min
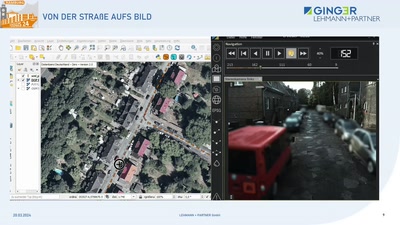
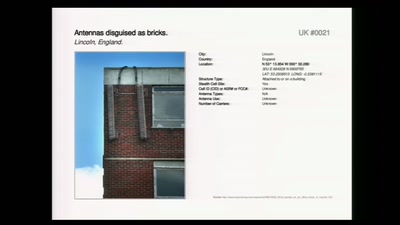
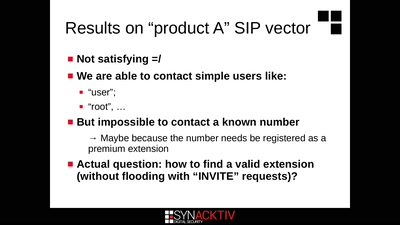
Intercoms Hacking
Call the frontdoor to install your backdoors
61 min
Programming FPGAs with PSHDL
Let's create the Arduino for FPGAs

41 min
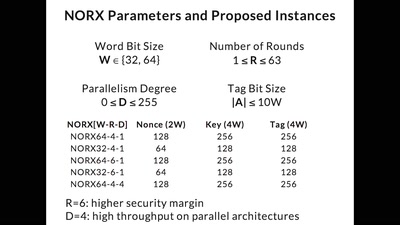
Extracting keys from FPGAs, OTP Tokens and Door Locks
Side-Channel (and other) Attacks in Practice

61 min
Deploying TLS 1.3: the great, the good and the bad
Improving the encrypted the web, one round-trip at a time
61 min