58 min
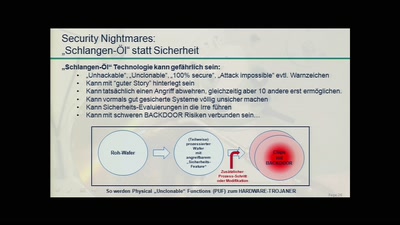
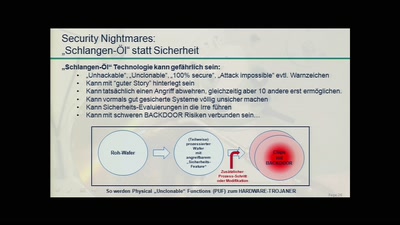
Physically Unclonable Functions for Hardware Tamper…

62 min
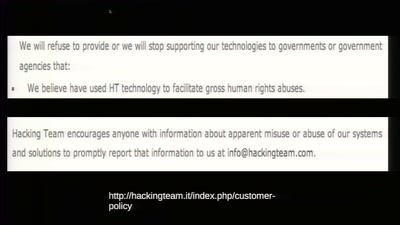
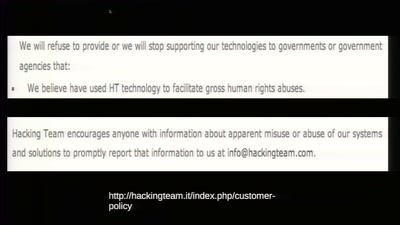
The militarization of the Internet
45 min
The militarization of the Internet
56 min
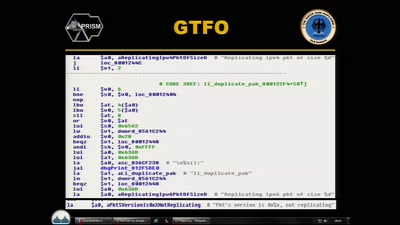
what is the winning move?
59 min
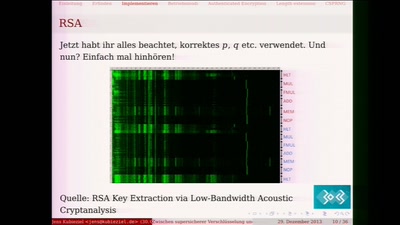
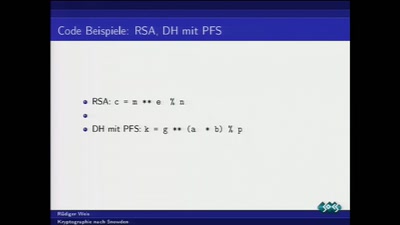
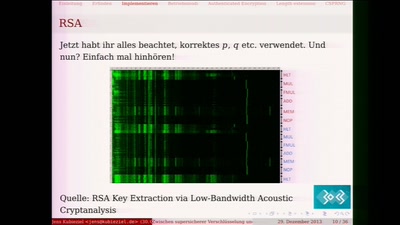
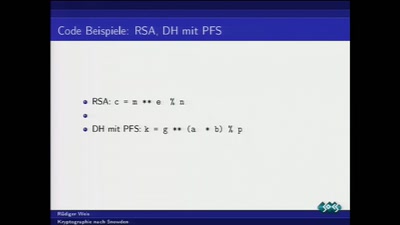
Ein Streifzug durch die Fehler in der Kryptografie
47 min
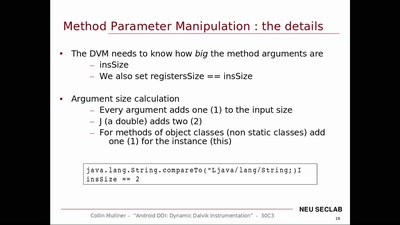
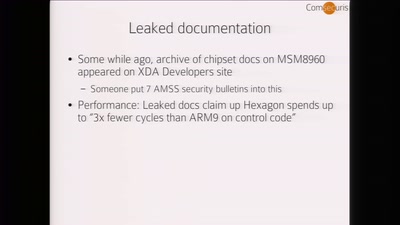
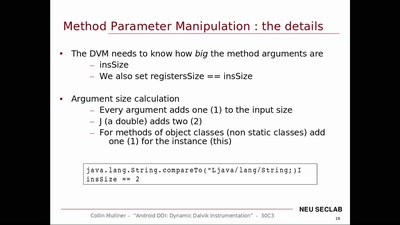
Dynamic Dalvik Instrumentation of Android Applications and…
58 min
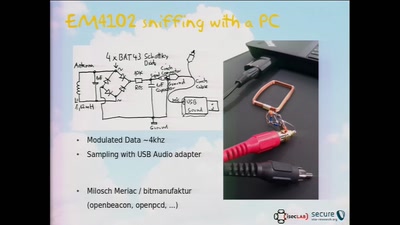
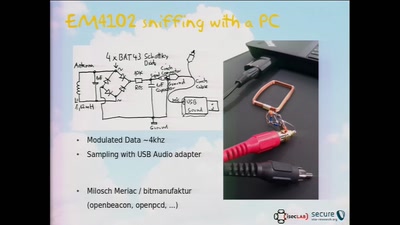
Hacking City-Wide Access Control Systems
61 min
Von der Historie zur Zukunft

59 min
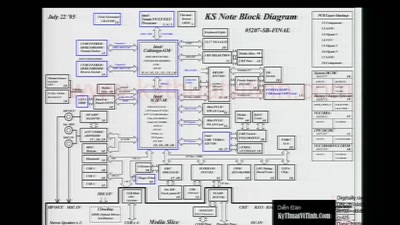
The future of IC analysis

41 min
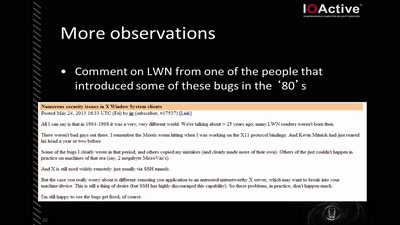
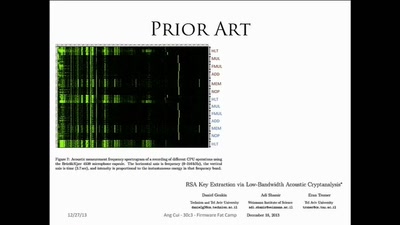
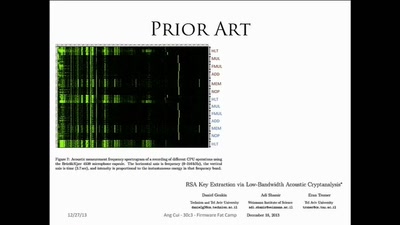
Side-Channel (and other) Attacks in Practice

55 min
Attribute Based Credentials in Practice
57 min
Was tun nach der mittelmäßigen Kryptographie-Apokalypse?
47 min
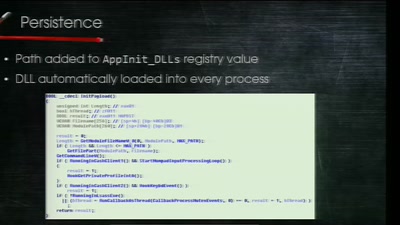
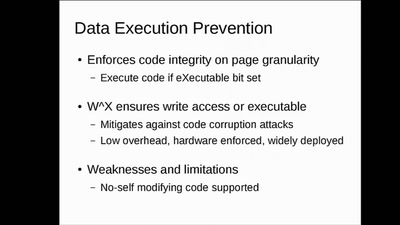
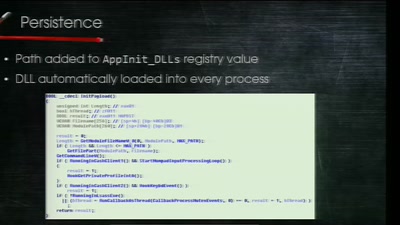
Clean boot every boot - rejecting persistence of malicious…
42 min
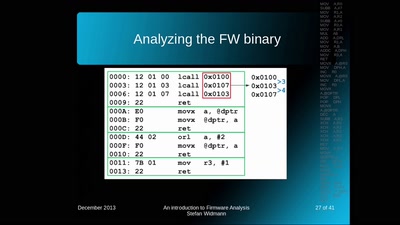
Embedded Security Using Binary Autotomy
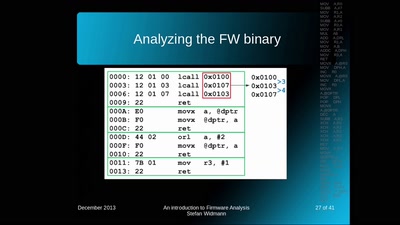
40 min
Techniques - Tools - Tricks

45 min
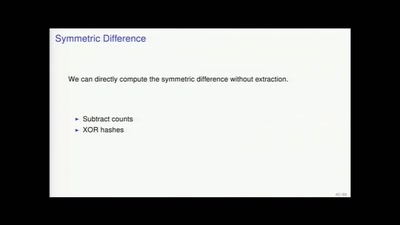
Deep program analysis without the headache
47 min
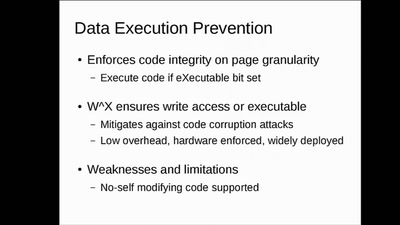
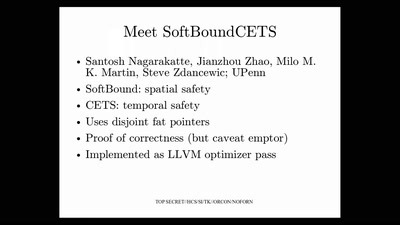
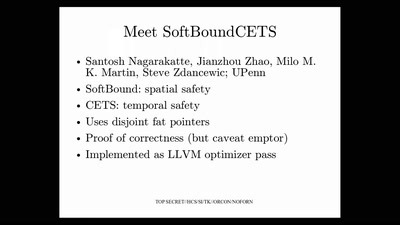
Applying science to eliminate 100% of buffer overflows

45 min
OMG - my Smart TV got pr0wn3d
56 min
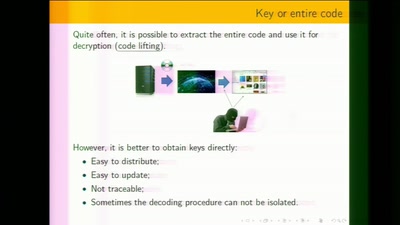
Stealing Money from ATMs with Malware
51 min
A Decentralized PKI For Social Movements