Search for "arma" returned 1247 results

55 min
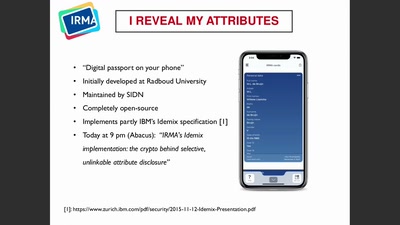
The Gospel of IRMA
Attribute Based Credentials in Practice
26 min
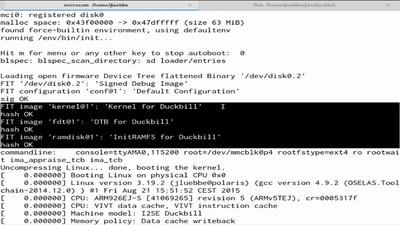
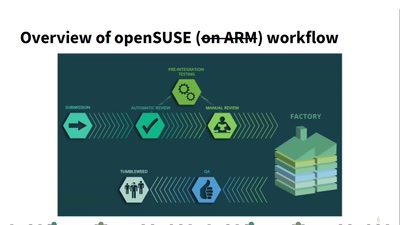
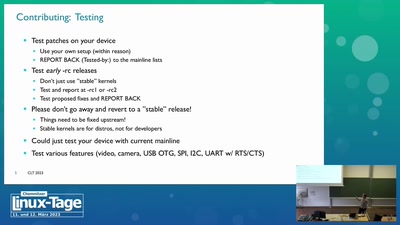
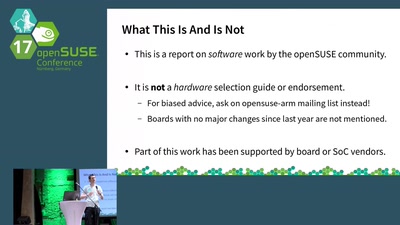
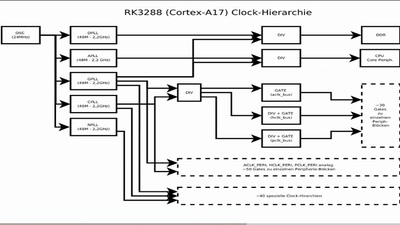
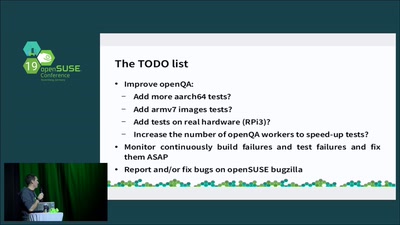
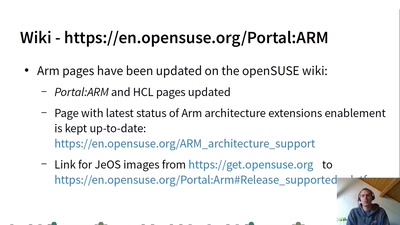
openSUSE on ARM
What happened since a year
15 min
openSUSE on Arm
The annual review
41 min
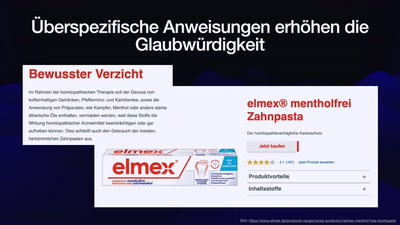
Fortbildung Cyber-Astrologie & KI-Karma
- Mit Teilnahmeurkunde zum Selbstausdrucken

60 min
the possibility of an army
phone verified accounts bringing the Hessian army back to…
36 min
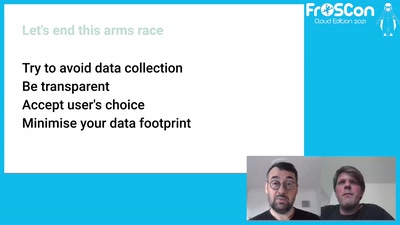
Let's end this arms race
Privacy on the internet is an arms race between legislators…
53 min
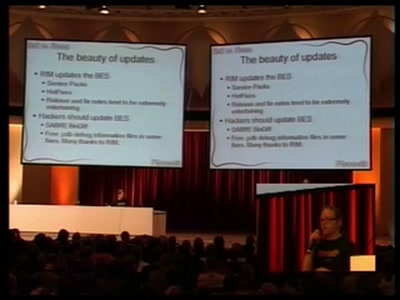
Blackberry: call to arms, some provided
Teach yourself upper management in 22 days

25 min