Search for ".dol" returned 2697 results
52 min
Leaving legacy behind
Reducing carbon footprint of network services with MirageOS…
40 min
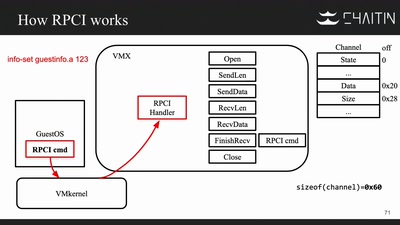
The Great Escape of ESXi
Breaking Out of a Sandboxed Virtual Machine

34 min
Scuttlebutt
The decentralized P2P gossip protocol
60 min
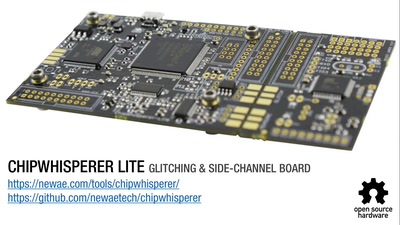
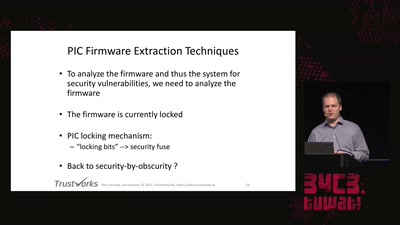
Opening Closed Systems with GlitchKit
'Liberating' Firmware from Closed Devices with Open Source…
60 min
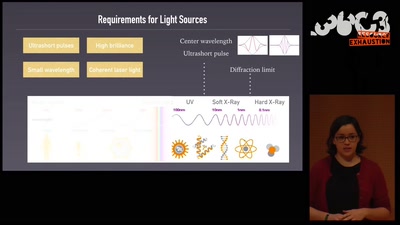
An ultrashort history of ultrafast imaging
Featuring the shortest movies and the largest lasers
60 min
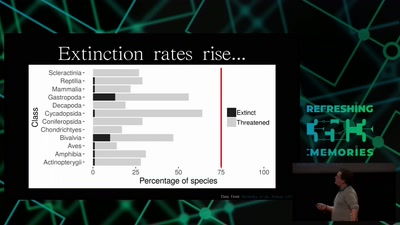
Hacking Ecology
How Data Scientists can help to avoid a sixth global…
57 min
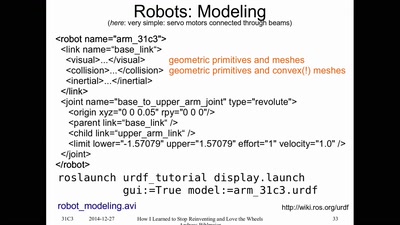
How I Learned to Stop Reinventing and Love the Wheels
or having FUN with (home/hackerspace) robotics
57 min
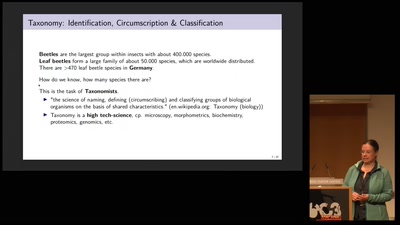
Protecting the Wild
Conservation Genomics between Taxonomy, Big Data,…

37 min
The foodsaving grassroots movement
How cooperative online structures can facilitate…
60 min
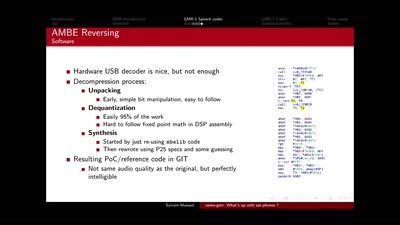
osmo-gmr: What's up with sat-phones ?
Piecing together the missing bits
29 min
The Urban Organism
Hacking [in] Hong Kong
58 min
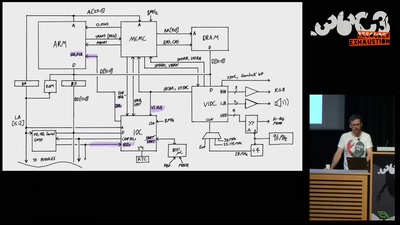
The Ultimate Acorn Archimedes talk
Everything about the Archimedes computer (with zero…
46 min
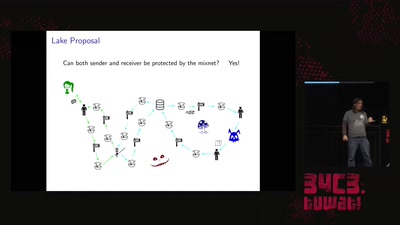
Practical Mix Network Design
Strong metadata protection for asynchronous messaging

60 min
Building a high throughput low-latency PCIe based SDR
Lessons learnt implementing PCIe on FPGA for XTRX Software…
59 min
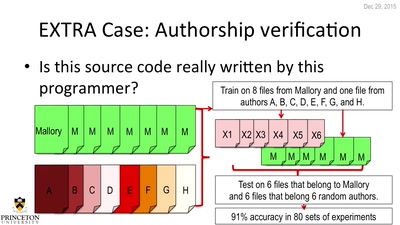
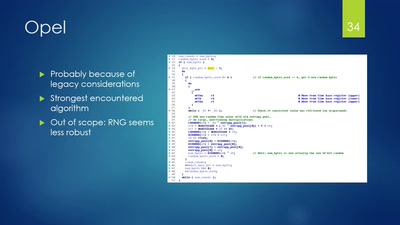
De-anonymizing Programmers
Large Scale Authorship Attribution from Executable Binaries…
51 min
Uncovering vulnerabilities in Hoermann BiSecur
An AES encrypted radio system
55 min