Search for "sev" returned 2718 results

30 min
The Magical Secrecy Tour
A Bus Trip into the Surveillance Culture of Berlin One Year…
55 min
What could possibly go wrong with <insert x86 instruction here>?
Side effects include side-channel attacks and bypassing…
19 min
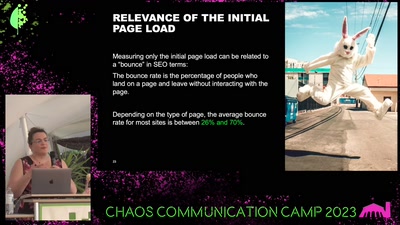
Fooled by the Website Carbon Calculator
Green Coding & Measuring the Environmental Impacts of IT
59 min
Fernvale: An Open Hardware and Software Platform, Based on the (nominally) Closed-Source…
A Lawful Method for Converting Closed IP into Open IP
55 min
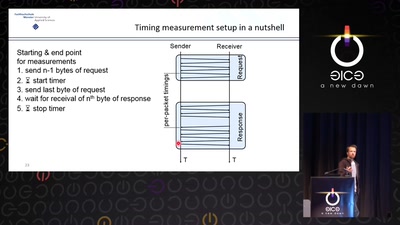
Revisiting SSL/TLS Implementations
New Bleichenbacher Side Channels and Attacks
61 min
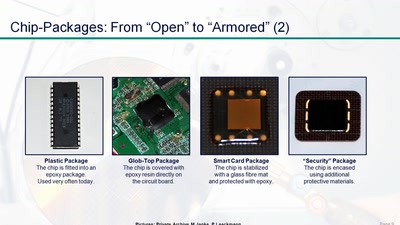
Uncaging Microchips
Techniques for Chip Preparation
60 min
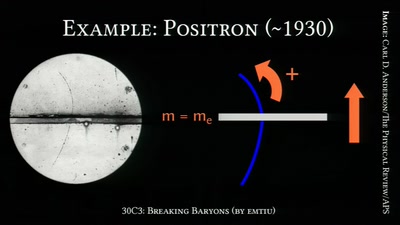
Breaking Baryons
On the Awesomeness of Particle Accelerators and Colliders
61 min
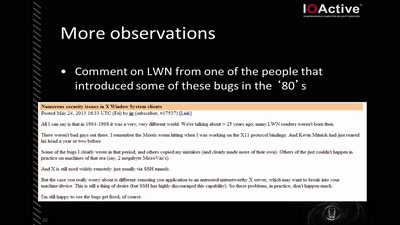
X Security
It's worse than it looks
21 min
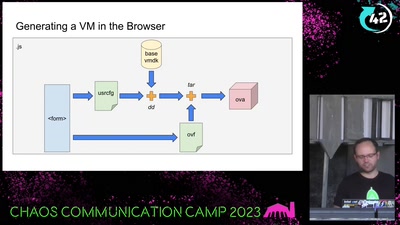
Bootloader Crimes
Building disposable Windows VMs

41 min
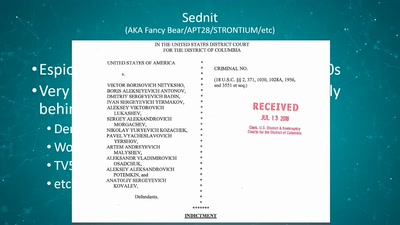
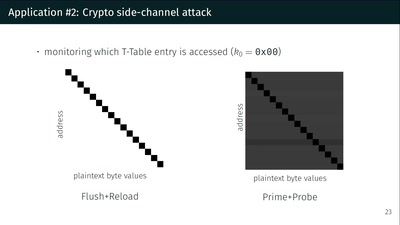
Extracting keys from FPGAs, OTP Tokens and Door Locks
Side-Channel (and other) Attacks in Practice
46 min
You can -j REJECT but you can not hide: Global scanning of the IPv6 Internet
Finding interesting targets in 128bit of entropy
57 min
TrustZone-M(eh): Breaking ARMv8-M's security
Hardware attacks on the latest generation of ARM Cortex-M…
39 min
Transmission Control Protocol
TCP/IP basics

38 min
Turning Chromebooks into regular laptops
With the power of open source!

43 min
Speaking Fiction To Power
Strategies and tactics to ‘hack’ public spaces and social…

59 min
Say hi to your new boss: How algorithms might soon control our lives.
Discrimination and ethics in the data-driven society

39 min