Search for "Ray" returned 3357 results
49 min
Cyborg Teams
Happy humans, tired machines

23 min
Securing Home Automation with Tor
Be Safe. Be Secure
59 min
Here Be Electric Dragons
Preparing for the Emancipation of Machines

41 min
SCADA StrangeLove 2
We already know
60 min
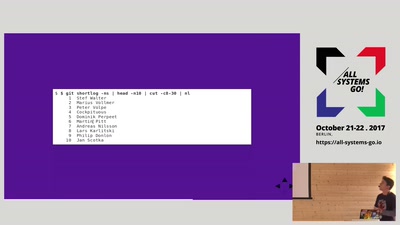
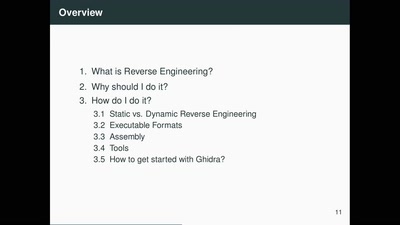
Ghidra - An Open Source Reverse Engineering Tool
How the NSA open-sourced all software in 2019
36 min
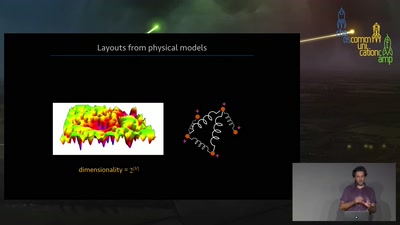
Visualization of networks using physics
How algorithms inspired by the laws of physics can create…

45 min
Triggering Deep Vulnerabilities Using Symbolic Execution
Deep program analysis without the headache
51 min
Reverse Engineering the MOS 6502 CPU
3510 transistors in 60 minutes
20 min