Search for "Ron" returned 9743 results

27 min
Message generation at the info layer
Basic introduction in coding on unvirtual realities.
68 min
Data Retention Update
News and Perspectives on Implementation and Opposition

35 min
A "Box" Full of Tools and Distros
Toolbox and Distrobox on openSUSE MicroOS & Tumbleweed
51 min
Open Source Schlüssel und Schlösser
Offene Quellen zum Bösen und Guten: von downloadbaren…

39 min
KI – Macht – Ungleichheit.
Was ist die soziale Dimension von Nachhaltigkeit und warum…

57 min
Cybercrime Convention
Hacking on its way to become a criminal act?

42 min
Ecocide and (green) colonialism in Sápmi
Data centers on indigenous land in Northern Europe
52 min
Turris: secure open source router
Who is the root on your router?
58 min
Is the SSLiverse a safe place?
An update on EFF's SSL Observatory project
45 min
Hopalong Casualty
On automated video analysis of human behaviour
31 min
Lightning Talks II
DeepVGI - Einsatz von Lowcost-Lidarsystemen für die…
64 min
Europäische Biometriestrategien
Die Automatisierung von Personenidentifizierung an der…
56 min
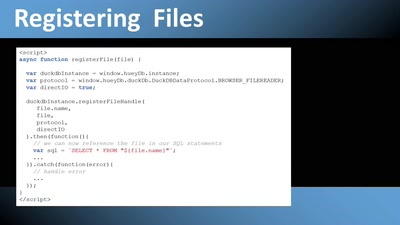
Huey: Pivoting hundreds of millions of rows in the Browser
Blazing fast in-browser Analytics based on DuckDB/WASM
14 min
From Concept to Deployment: Creating an openSUSE based external-dns solution for k3s
A virtual talk on using ExternalDNS with Kubernetes

42 min
Was wollen die Regierungen im Internet?
Neue Entwicklungen in der internationalen…
29 min
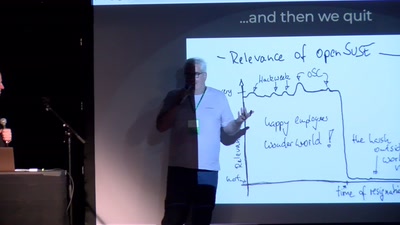
openSUSE's different shades of green
a view on openSUSE from two benevolent ex-SUSE guys

42 min
Free Software and Platform Regulation
The impact of the Digital Market Act on Free Software

34 min
Lightning Talks I
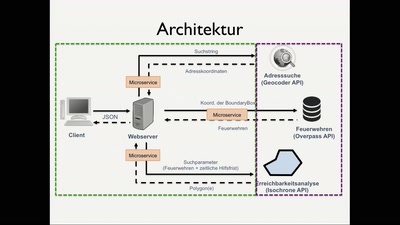
Routenplanung durch Flächen - Interaktive Visualisierung…
55 min
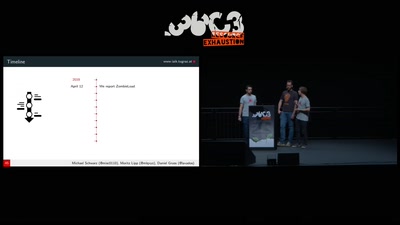
ZombieLoad Attack
Leaking Your Recent Memory Operations on Intel CPUs

50 min
Ceph Explained - With Raspberry Pis
Demonstration of Ceph on a Raspberry Pi cluster
52 min
Practical Mac OS X Insecurity
Security Concepts, Problems, and Exploits on Your Mac
58 min