Search for "Benks" returned 123 results
61 min
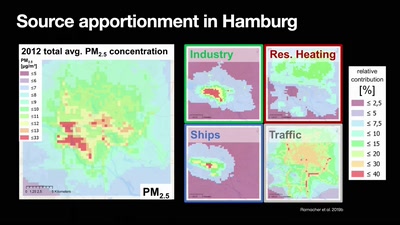
Numerical Air Quality Modeling Systems
a journey from emissions to exposure

61 min
Ten years after ‚We Lost The War‘
The future does not look much brighter than ten years ago.…
61 min
Code Pointer Integrity
... or how we battle the daemons of memory safety
44 min
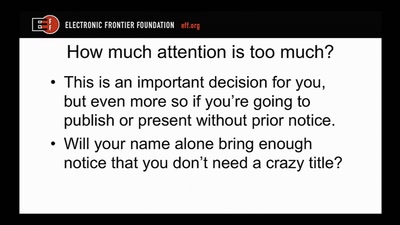
Disclosure DOs, Disclosure DON'Ts
Pragmatic Advice for Security Researchers
61 min
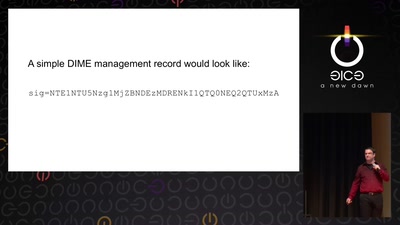
Now I sprinkle thee with crypto dust
Internet reengineering session
65 min
35C3 Infrastructure Review
Up and to the right: All the statistics about this event…
44 min
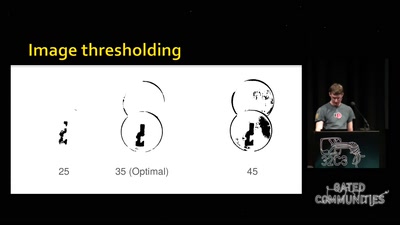
Replication Prohibited
3D printed key attacks
64 min
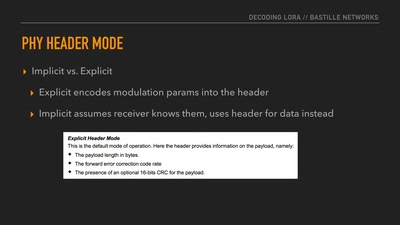
Decoding the LoRa PHY
Dissecting a Modern Wireless Network for the Internet of…
49 min
Key-logger, Video, Mouse
How to turn your KVM into a raging key-logging monster
60 min
Breaking Baryons
On the Awesomeness of Particle Accelerators and Colliders
58 min
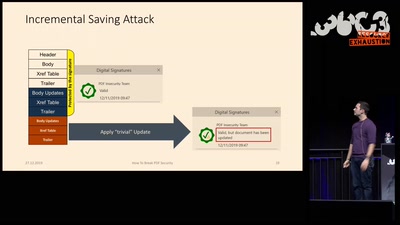
How to Break PDFs
Breaking PDF Encryption and PDF Signatures
69 min
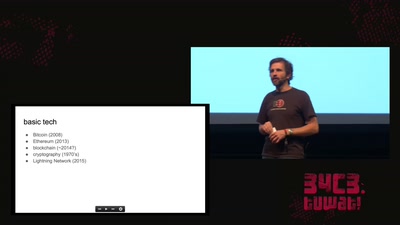
cryptocurrencies, smart contracts, etc.: revolutionary tech?
short answer: Yes!
60 min
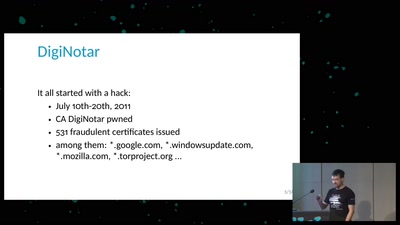
Everything you always wanted to know about Certificate Transparency
(but were afraid to ask)
55 min
Graphs, Drones & Phones
The role of social-graphs for Drones in the War on Terror.
51 min