Search for "crypto" returned 406 results
57 min
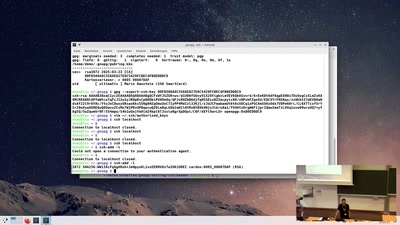
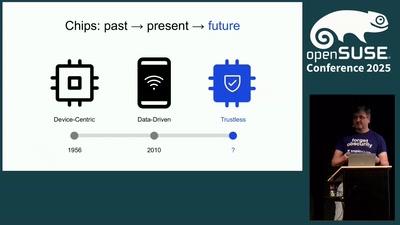
Kryptographie-Hardware: Von TPMs bis Nitrokeys
– was sie versprechen, was sie können und wo sie versagen

61 min
Trustworthy secure modular operating system engineering
fun(ctional) operating system and security protocol…

54 min
What Price the Upload Filter?
The history and costs of government exceptional access

119 min
CR235: I #WannaCry
Der Angriff der Cryptotrojaner

55 min
Because "use urandom" isn't everything: a deep dive into CSPRNGs in Operating Systems &…
Implementation, hazards and updates on use of RNGs in…
54 min
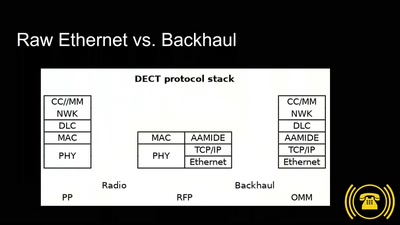
#mifail oder: Mit Gigaset wäre das nicht passiert!
DECT is korrekt.
57 min
TrustZone-M(eh): Breaking ARMv8-M's security
Hardware attacks on the latest generation of ARM Cortex-M…
47 min
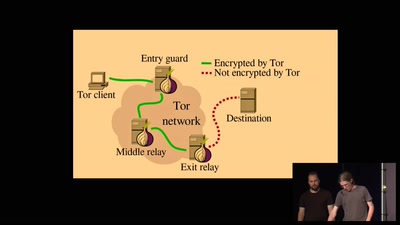
Introduction to Mix Networks and Katzenpost
a new anonymity movement
43 min
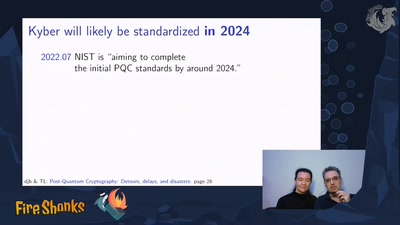
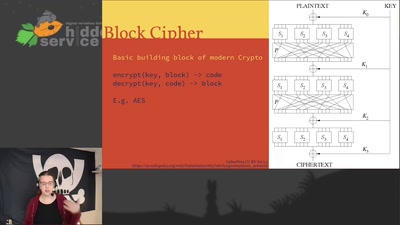
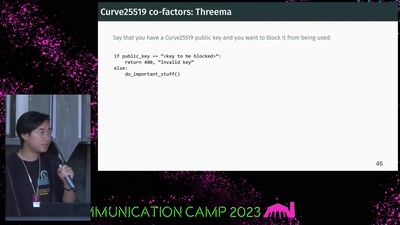
If It Ain't Broken, Do Fix It
Building Modern Cryptography
28 min