Search for "Ray" returned 3357 results
49 min
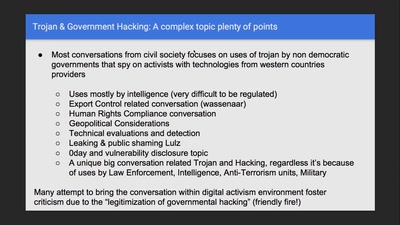
Regulating Law Enforcement use of Trojans
Implementing a Law to juridically, operationally and…

70 min
Attacking IoT Telemetry
A study of weaknesses in the pipeline of rapidly advancing…
39 min
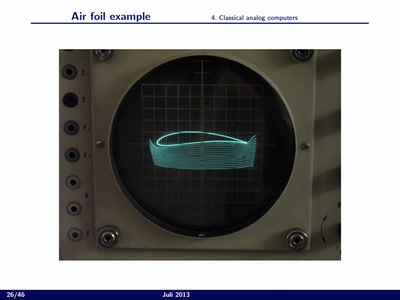
Analog Computing
High performance/low power computing based on the analog…

57 min
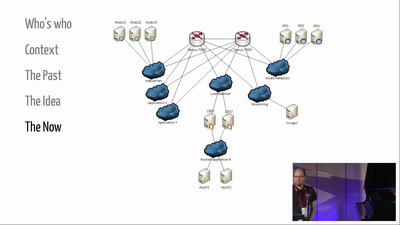
34C3 Infrastructure Review
How does the CCC run a conference?
57 min
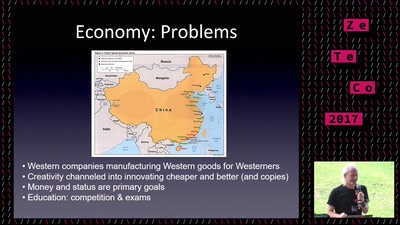
Hacking in China
What China has to offer
32 min
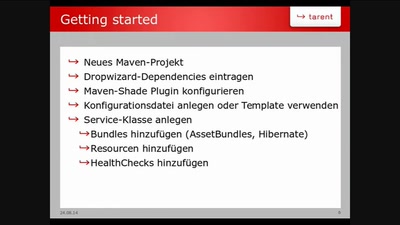
Dropwizard
Framework für Microservices
45 min
Further hacks on the Calypso platform
or how to turn a phone into a BTS
58 min
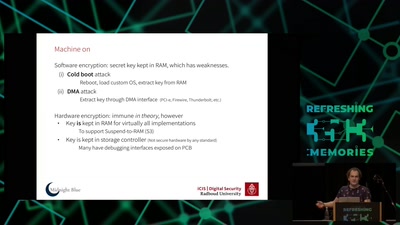
Self-encrypting deception
weaknesses in the encryption of solid state drives (SSDs)

31 min
Extended DNA Analysis
Political pressure for DNA-based facial composites
27 min
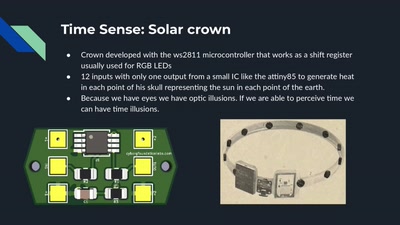
Cyborg Foundation
Transpecies Society
59 min
Micro Services
Vertical thinking for a simple architecture!
61 min




![[SPONSOR] Beyond Pushing Code: Lessons Learned from Dynatrace's Open Source Journey on GitHub](https://static.media.ccc.de/media/events/glt/2023/381-e370e02a-1cf3-5177-9397-26969f8b492e.jpg)