Search for "mm" returned 7354 results

60 min
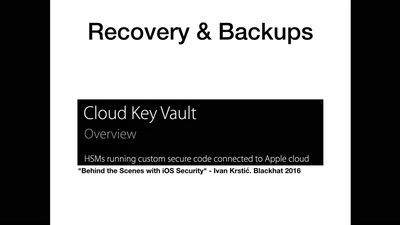
Quantum Cryptography
from key distribution to position-based cryptography
35 min
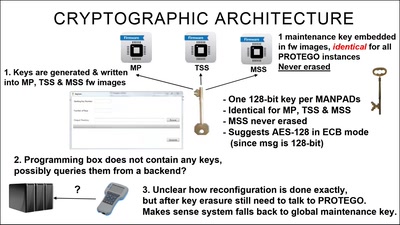
Harry Potter and the Not-So-Smart Proxy War
Taking a look at a covert CIA virtual fencing solution
40 min
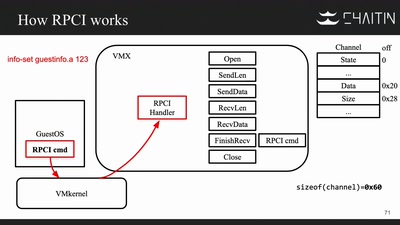
The Great Escape of ESXi
Breaking Out of a Sandboxed Virtual Machine
31 min
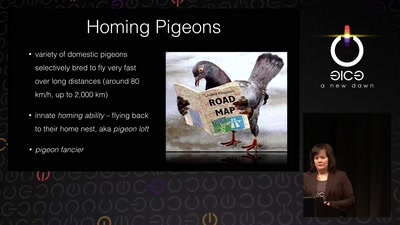
Living Drones
From war pigeons in 1914 to cyborg moths in 2014
60 min
Why is GPG "damn near unusable"?
An overview of usable security research

43 min
How Facebook tracks you on Android
(even if you don’t have a Facebook account)
56 min
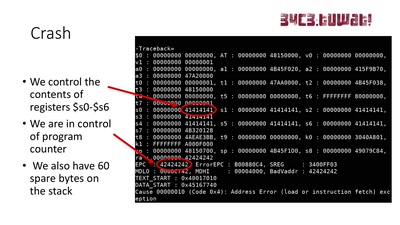
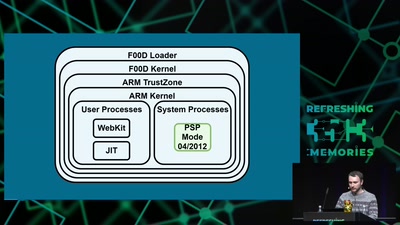
Viva la Vita Vida
Hacking the most secure handheld console
60 min
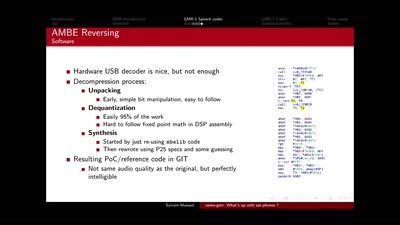
osmo-gmr: What's up with sat-phones ?
Piecing together the missing bits
31 min
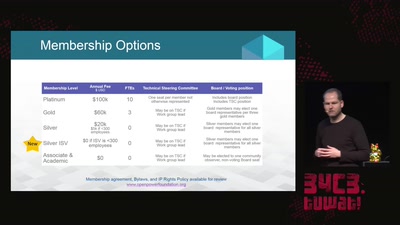
openPower - the current state of commercial openness in CPU development
is there no such thing as open hardware?
61 min
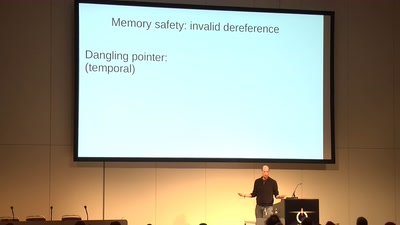
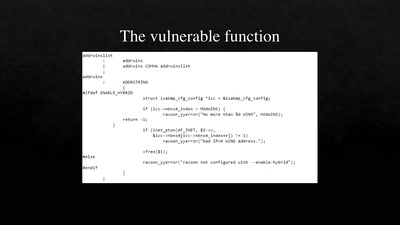
Code Pointer Integrity
... or how we battle the daemons of memory safety
39 min
Tales of old: untethering iOS 11
Spoiler: Apple is bad at patching

31 min
Extended DNA Analysis
Political pressure for DNA-based facial composites
30 min
Automatically Subtitling the C3
How speech processing helps the CCC subtitle project, and…
59 min
Fernvale: An Open Hardware and Software Platform, Based on the (nominally) Closed-Source…
A Lawful Method for Converting Closed IP into Open IP

54 min
What Price the Upload Filter?
The history and costs of government exceptional access
60 min