Search for "Kat" returned 5621 results
60 min
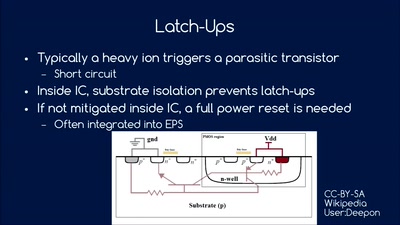
So you want to build a satellite?
How hard can it be? An introduction into CubeSat development

61 min
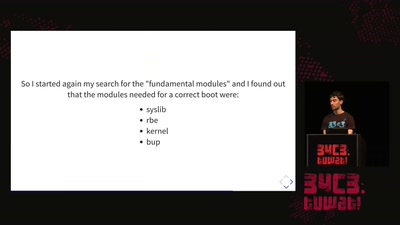
Trustworthy secure modular operating system engineering
fun(ctional) operating system and security protocol…
61 min
An Elevator to the Moon (and back)
Space Transportation and the Extraterrestrial Imperative

44 min
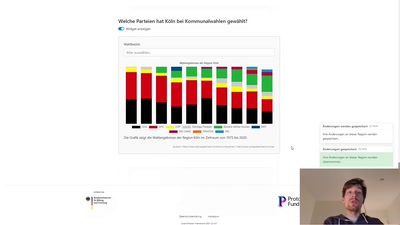
Fallstricke der Anonymisierung
Auf unserer Onlineplattform können Studierende…
62 min
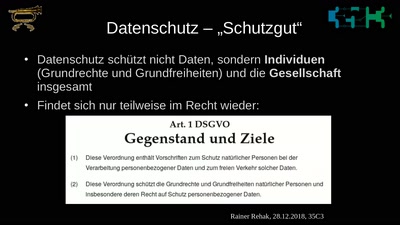
Was schützt eigentlich der Datenschutz?
Warum DatenschützerInnen aufhören müssen von individueller…

61 min
The Invisible Committee Returns with "Fuck Off Google"
Cybernetics, Anti-Terrorism, and the ongoing case against…
60 min
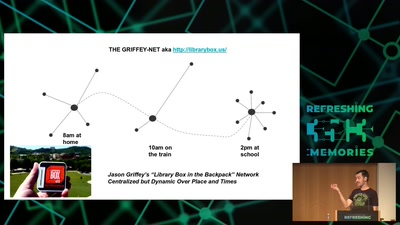
Wind: Off-Grid Services for Everyday People
Integrating nearby and offline connectivity with the…
61 min
The architecture of a street level panopticon
How drones, IMSI Catchers, and cameras are shaping our…

56 min
Rhetorische Selbstsabotage: Was eigentlich passiert, wenn wir reden
Einige Gedanken über Stimme und wie wir sagen können, was…
64 min
We only have one earth
A case for expansionistic space policy
58 min
Thwarting Evil Maid Attacks
Physically Unclonable Functions for Hardware Tamper…
60 min
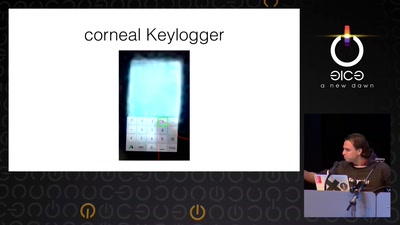
Ich sehe, also bin ich ... Du
Gefahren von Kameras für (biometrische)…
56 min


![[r3s] Erklärhaj züchtet Kristalle (Erklärhaj)](https://static.media.ccc.de/media/events/rc3/2021/874-6cc6dfb3-957b-56c2-ac3d-03067ebad2d8.jpg)