Search for "Kat" returned 5621 results
59 min
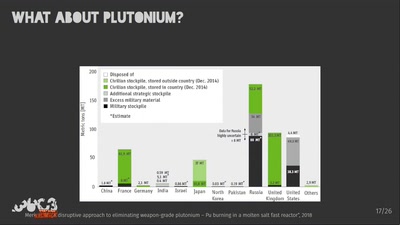
Megatons to Megawatts
Military warheads as a source of nuclear fuel
31 min
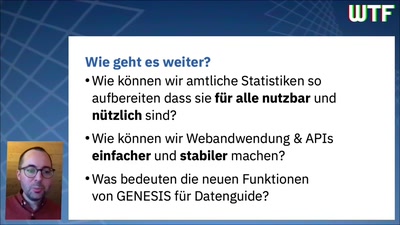
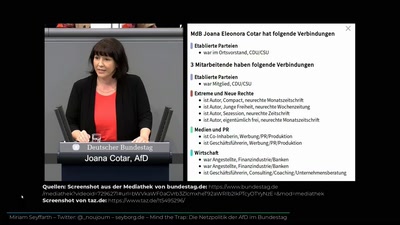
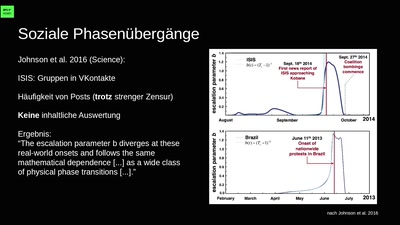
Berechnete Welt
Unsere Daten, die Zukunft und die zerstörte Demokratie

47 min
Netzpolitik in der Schweiz
Die aktuellen Auseinandersetzungen über digitale…

32 min
Finding the Weak Crypto Needle in a Byte Haystack
Automatic detection of key-reuse vulnerabilities
31 min
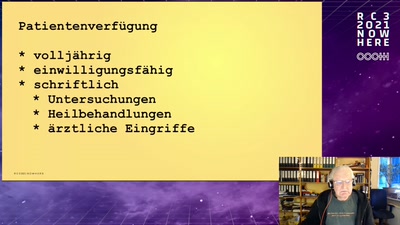
Access To Bodies
Ein Leitfaden für post-humane Computer- und…
26 min
Eine kleine Geschichte der Parlamentsschlägerei
Schlagende Argumente, fliegende Fäuste
60 min
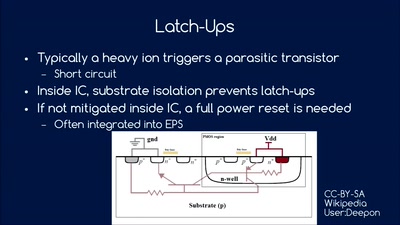
So you want to build a satellite?
How hard can it be? An introduction into CubeSat development

61 min