Search for "Kat" returned 5611 results

60 min
Quantum Cryptography
from key distribution to position-based cryptography

32 min
Why Do We Anthropomorphize Computers?...
...and dehumanize ourselves in the process?
54 min
How hackers grind an MMORPG: by taking it apart!
An introduction to reverse engineering network protocols
56 min
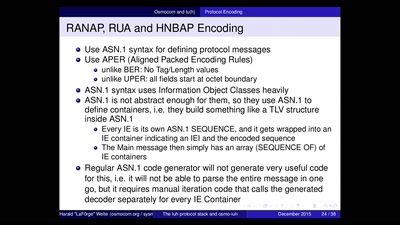
Running your own 3G/3.5G network
OpenBSC reloaded
43 min
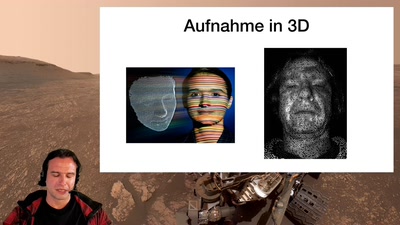
Hirne Hacken
Menschliche Faktoren der IT-Sicherheit
55 min
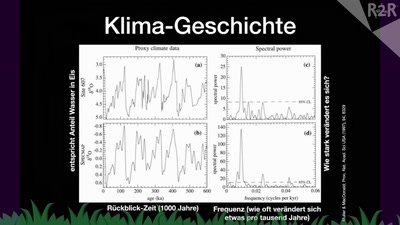
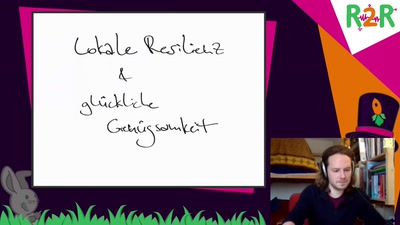
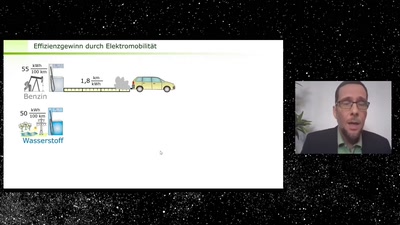
Nach der Coronakrise ist mitten in der Klimakrise
Wege aus der Klimakrise - Was uns droht und was getan…
58 min
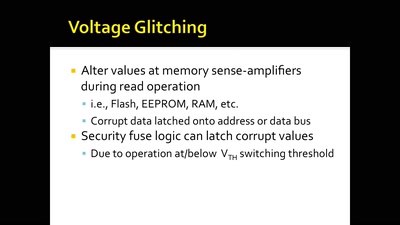
Glitching For n00bs
A Journey to Coax Out Chips' Inner Secrets
56 min
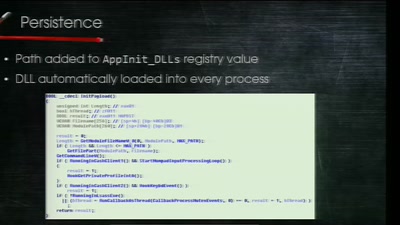
Electronic Bank Robberies
Stealing Money from ATMs with Malware
61 min
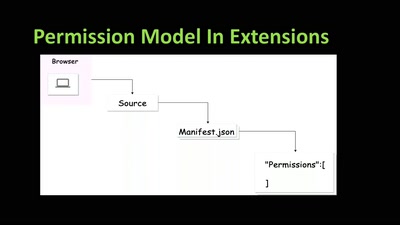
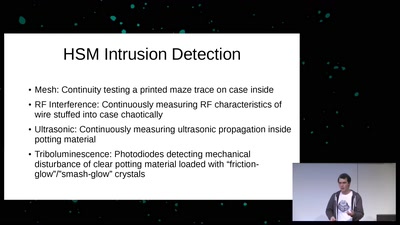
Untrusting the CPU
A proposal for secure computing in an age where we cannot…
60 min
The Perl Jam 2
The Camel Strikes Back
60 min