Search for "Max" returned 4737 results
60 min
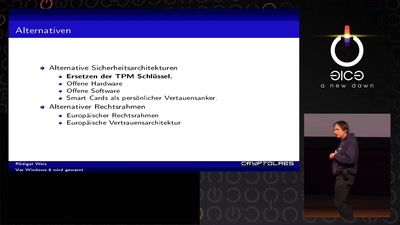
Vor Windows 8 wird gewarnt
Und nichts (Secure) Bootet mehr?

60 min
What does Big Brother see, while he is watching?
Uncovering images from the secret Stasi archives.
28 min
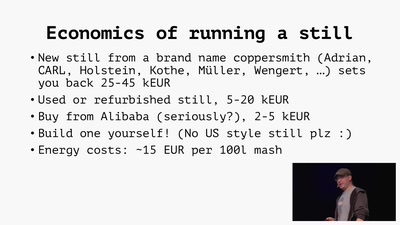
Home Distilling
Theory and practice of moonshining and legal distilling

38 min
Afroroutes: Africa Elsewhere
VR experience "Beyond Slavery"
60 min
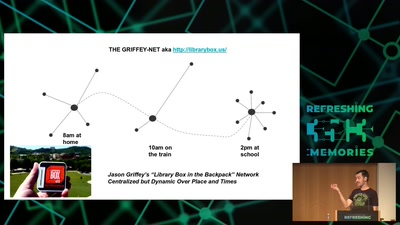
Wind: Off-Grid Services for Everyday People
Integrating nearby and offline connectivity with the…

61 min
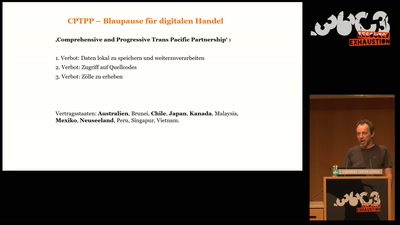
Avoiding kernel panic: Europe’s biggest fails in digital policy-making
How the institutions fuck up, and how we fuck it up as well
37 min
Music on Mars?
A Musical Adventure for Astronauts and the Space Cadets Who…
63 min
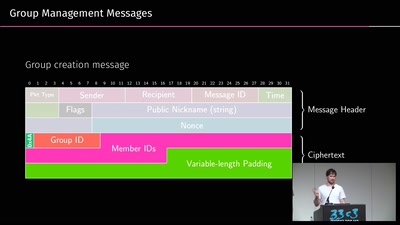
A look into the Mobile Messaging Black Box
A gentle introduction to mobile messaging and subsequent…
53 min
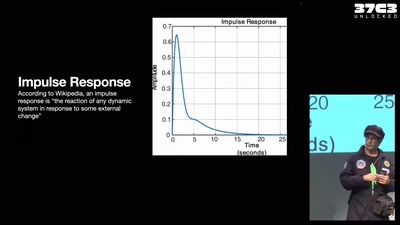
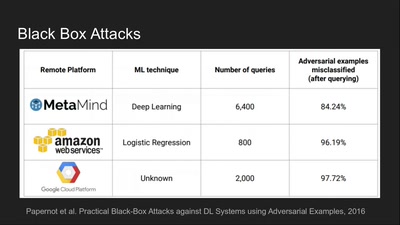
Deep Learning Blindspots
Tools for Fooling the "Black Box"

63 min
Das Assange-Auslieferungsverfahren
Als Prozessbeobachter in London
38 min
Gerechtigkeit 4.0
Makroökonomische Auswirkungen der Digitalisierung auf den…
61 min