Search for "Ben H." returned 5991 results
38 min
The year of the Linux desktop
Why are we still waiting for the breakthrough?

37 min
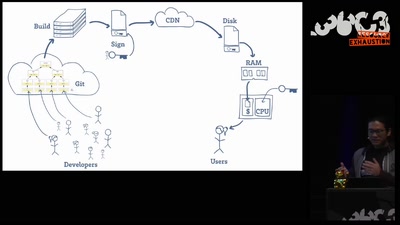
Hacking (with) a TPM
Don't ask what you can do for TPMs, Ask what TPMs can do…
60 min
Open Source is Insufficient to Solve Trust Problems in Hardware
How Betrusted Aims to Close the Hardware TOCTOU Gap
16 min
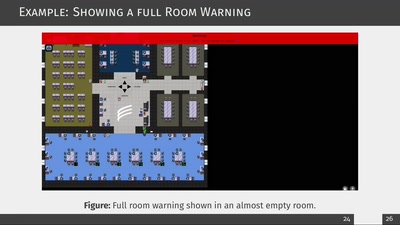
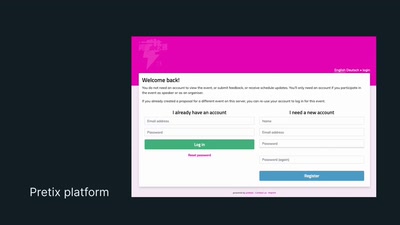
Decent Patterns
an Open UX Library for Decentralisation
59 min
Not your Grandfathers moon landing
Hell yeah, it's Rocket Science 3.1415926535897932384626!
62 min
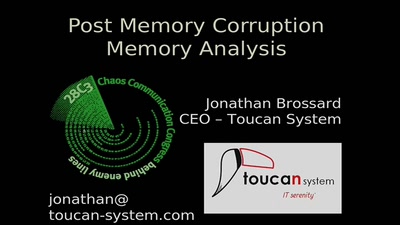
Post Memory Corruption Memory Analysis
Automating exploitation of invalid memory writes

139 min
Im Sandkasten wird nur gespielt
Das Suchtpotential von Antivirenprogrammen
63 min
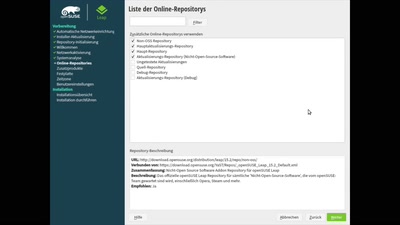
Video and QnA / Kanal LUG-VS : Installation von openSUSE Leap.15 KDE-Desktop
Mit der virtuellen Maschinenverwaltung (QUEMU/KVM)
27 min
making a switch from docker to podman in development environment
how to configure env to use podman
44 min