Search for "crypto" returned 406 results
46 min
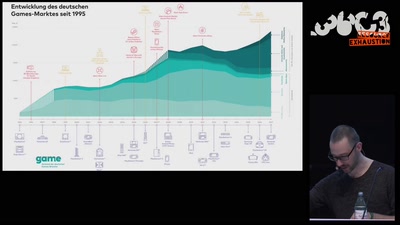
Let’s play Infokrieg
Wie die radikale Rechte (ihre) Politik gamifiziert
57 min
Quantum Mechanics
A Gentle Introduction
61 min
Nintendo Hacking 2016
Game Over
66 min
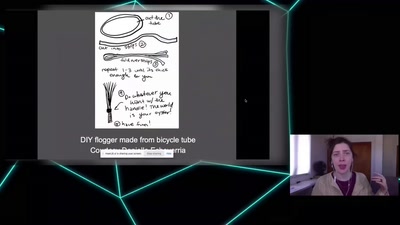
Hacking Diversity: The Politics of Inclusion in Open Technology Cultures
Christina Dunbar-Hester

55 min
What is Good Technology?
Answers & practical guidelines for engineers.
58 min
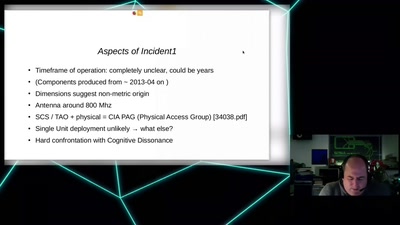
CIA vs. Wikileaks
Intimiditation surveillance and other tactics observed and…
61 min
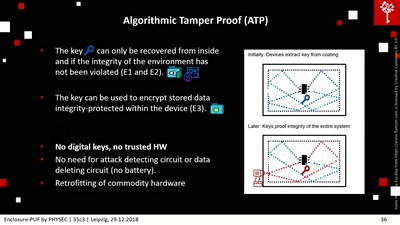
Enclosure-PUF
Tamper Proofing Commodity Hardware and other Applications

66 min
Keine Anhaltspunkte für flächendeckende Überwachung
Die Diskussion um NSA, PRISM, Tempora sprachlich und…
35 min
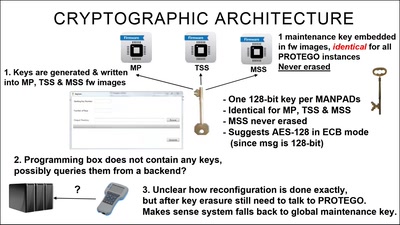
Harry Potter and the Not-So-Smart Proxy War
Taking a look at a covert CIA virtual fencing solution
49 min
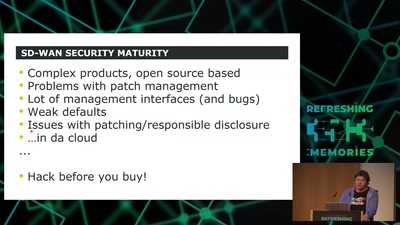
SD-WAN a New Hop
How to hack software defined network and keep your sanity?
28 min
Long war tactics
or how we learned to stop worrying and love the NSA

51 min

![Wie man zu[mr] System Ingenieur(in)? wird](https://static.media.ccc.de/media/events/rc3/133-ed57ba19-7686-55a9-b228-38c5a10b444b.jpg)