Search for "ths" returned 9236 results

61 min
Correcting copywrongs
European copyright reform is finally on the horizon
64 min
"Exploit" in theater
post-existentialism is the question, not post-privacy

59 min
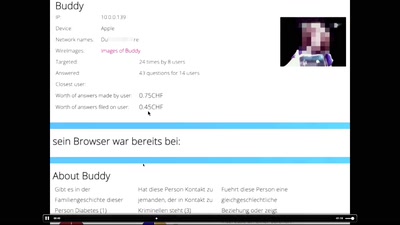
Say hi to your new boss: How algorithms might soon control our lives.
Discrimination and ethics in the data-driven society
59 min
SmartMeter
A technological overview of the German roll-out
35 min
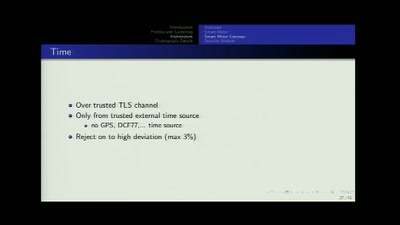
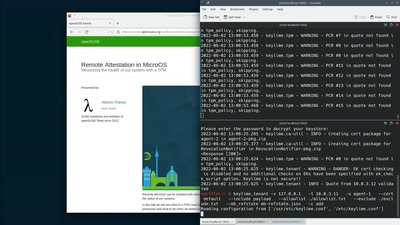
Remote Attestation in MicroOS
Measuring the health of our system with a TPM
41 min
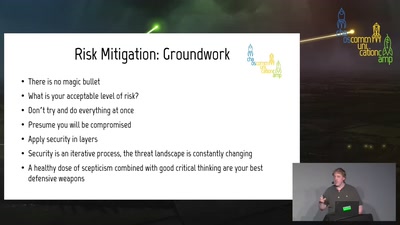
Introduction to (home) network security.
A beginner-friendly guide to network segmentation for…
32 min
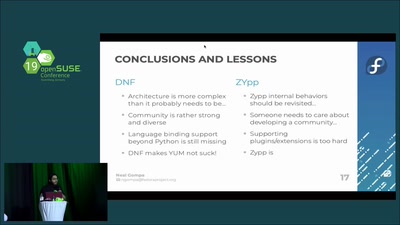
DNF vs ZYpp: Fight!
A comparison of the two major RPM package managers
25 min
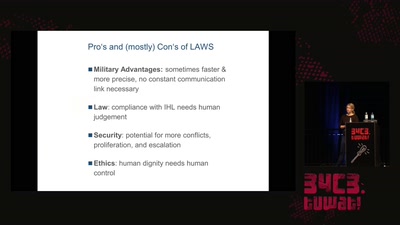
Regulating Autonomous Weapons
The time travelling android isn’t even our biggest problem
33 min
Social cooling
How the reputation economy is turning us into conformists

66 min
Podjournalism
The Role of Podcasting in Critical and Investigative…
82 min
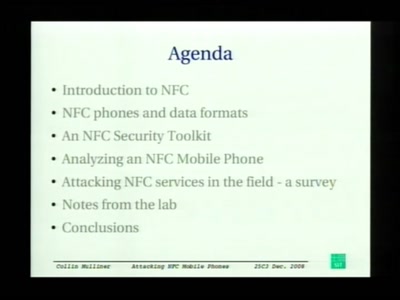
Attacking NFC mobile phones
First look at the security of NFC mobile phones
30 min
NexMon - Make Wi-Fi hacking on smartphones great again!
Reverse engineering of the Nexus 5 Wi-Fi chip

25 min
Uyuni: introduction, last year's updates and future
What is Uyuni? - What's been going on the last year? -…
38 min
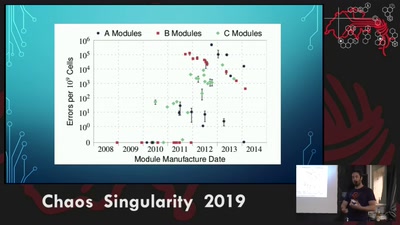
Rowhammer exploit
Viability of the Rowhammer Attack when ECC memory is used
40 min
LibreRouter demo
Lessons learned developing open source hardware for the…
44 min
Legacy Crypto Never Dies
Cracking DES nearly 20 years after the EFF DES Cracker
29 min
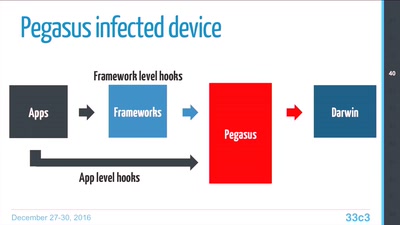
Pegasus internals
Technical Teardown of the Pegasus malware and Trident…

48 min
Oil Into Digits
A short exploration of the relation between energy and…
68 min
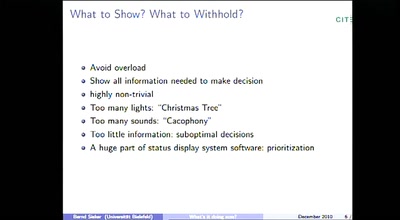
"Spoilers, Reverse Green, DECEL!" or "What's it doing now?"
Thoughts on the Automation and its Human interfaces on…
45 min
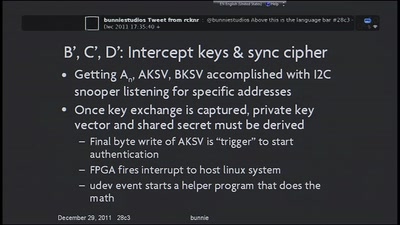
Implementation of MITM Attack on HDCP-Secured Links
A non-copyright circumventing application of the HDCP…
56 min
Blackbox JTAG Reverse Engineering
Discovering what the hardware architects try to hide from…
51 min
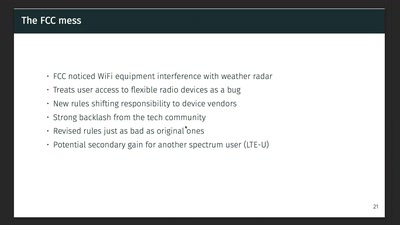
Wireless Drivers: Freedom considered harmful?
An OpenWrt perspective on the development of Linux 802.11…
60 min
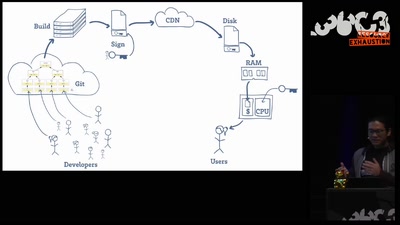
Open Source is Insufficient to Solve Trust Problems in Hardware
How Betrusted Aims to Close the Hardware TOCTOU Gap
30 min
Love, CyBorgs, Art and Open Source – an artistic approach on how to stay golden
How to educate society through the language of art
45 min