Search for "llm" returned 319 results
40 min
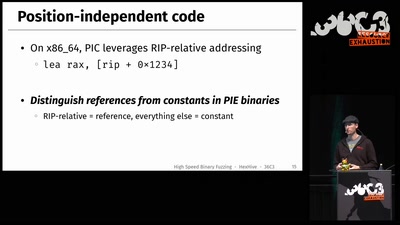
Fuzz Everything, Everywhere, All at Once
Advanced QEMU-based fuzzing
61 min
Code Pointer Integrity
... or how we battle the daemons of memory safety
47 min
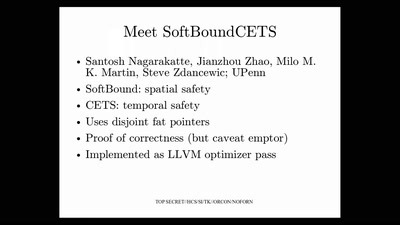
Bug class genocide
Applying science to eliminate 100% of buffer overflows
29 min
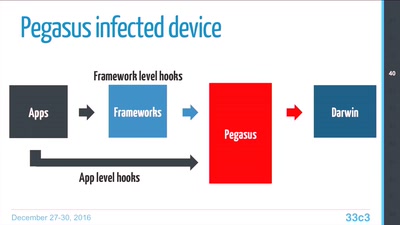
Pegasus internals
Technical Teardown of the Pegasus malware and Trident…
58 min
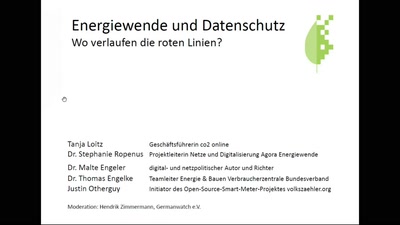
Energiewende & Datenschutz
Wo verlaufen die roten Linien bei der Energiewende"
54 min