Search for person "Walter van Holst" returned 143 results
40 min
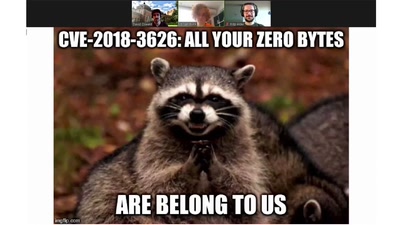
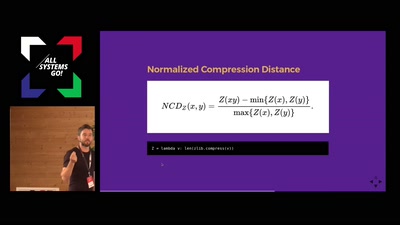
Fuzz Everything, Everywhere, All at Once
Advanced QEMU-based fuzzing
43 min
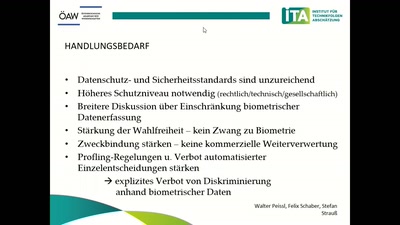
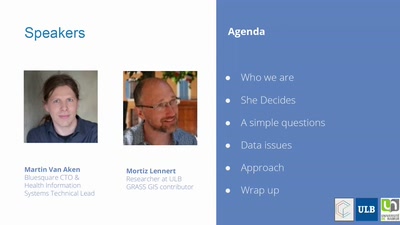
#NoPNR – Let’s kill the next Data Retention Law
How to Stop the Dubious Use of Passenger Name Records by…

49 min