Search for "24" returned 4476 results
60 min
Concepts for global TSCM
getting out of surveillance state mode

26 min
Opening Event
35C3: Refreshing Memories
39 min
ID Cards in China: Your Worst Nightmare
In China Your ID Card Knows Everything
49 min
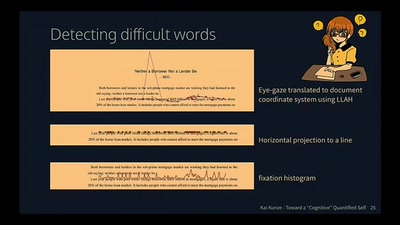
Toward a Cognitive "Quantified Self"
Activity Recognition for the Mind
51 min
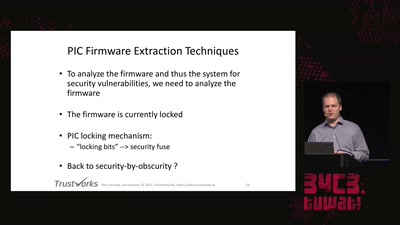
Uncovering vulnerabilities in Hoermann BiSecur
An AES encrypted radio system
51 min
Ecuador: how an authoritarian government is fooling the entire world
Guess what? The Government of Rafael Correa actually is…
32 min
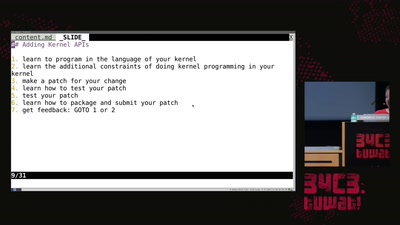
library operating systems
reject the default reality^W abstractions and substitute…
58 min
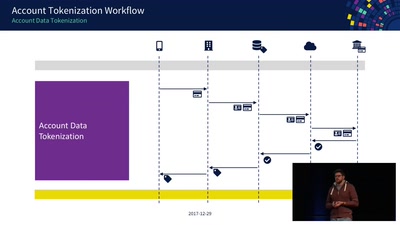
Decoding Contactless (Card) Payments
An Exploration of NFC Transactions and Explanation How…
58 min
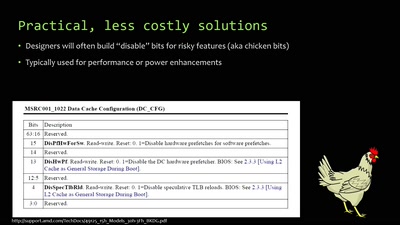
When hardware must „just work“
An inside look at x86 CPU design
57 min
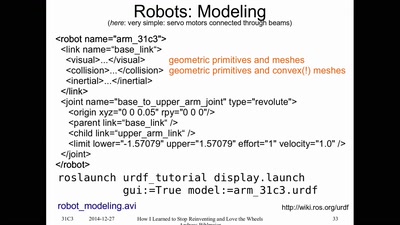
How I Learned to Stop Reinventing and Love the Wheels
or having FUN with (home/hackerspace) robotics
60 min
Beyond Anti Evil Maid
Making it easier to avoid low-level compromise, and why…
55 min
White-Box Cryptography
Survey

58 min
The Magic World of Searchable Symmetric Encryption
A brief introduction to search over encrypted data

62 min
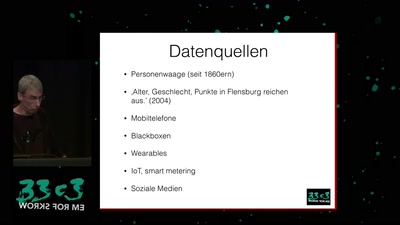
Corporate surveillance, digital tracking, big data & privacy
How thousands of companies are profiling, categorizing,…
58 min