93 min
Bluetooth Hacking - The State of The Art
A roundup and live demonstrations of all currently known…
113 min
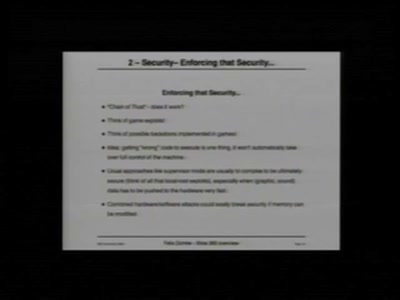
"Xbox" and "Xbox 360" Hacking
17 Mistakes Microsoft Made in the Xbox Security System &…

64 min
Security Nightmares 2006
Oder: worüber wir nächstes Jahr lachen werden
59 min
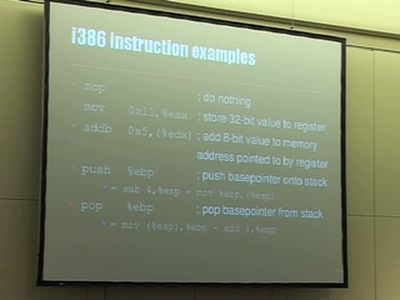
Understanding buffer overflow exploitation
The fascinating interplay of CPU, stack, C-compiler and…

52 min
Hacking into TomTom Go
Reverse-Engineering des Embedded-Linux-Navigationssystems

52 min
Military intelligence for terrorists(tm)
A lamer's introduction to retrieving "sensitive"…
46 min
Atmel AVR für Dummies
Was ist denn nun eigentlich so ein 'Interrupt'?
46 min
Paper-Prototyping Workshop
Eine Usability-Methode

60 min
Black Ops Of TCP/IP 2005.5
New Explorations: Large Graphs, Larger Threats
51 min
I See Airplanes!
How to build your own radar system
56 min
Hacking CCTV
Watching the watchers, having fun with cctv cameras, making…

61 min
PyPy - the new Python implementation on the block
Language/VM R&D, whole program type inference, translation…

52 min
3G Investigations
Scanning your GPRS/UMTS IP network for fun and profit
52 min
WiFi Long Shots
Wireless connections of 20km and more
47 min
RFID - overview of protocols, librfid implementation and passive sniffing
ISO14443, ISO15693, their GPL librfid implementation and…
53 min
Private investigations in searching
How to find any book (and many other roadkills) on the…
51 min
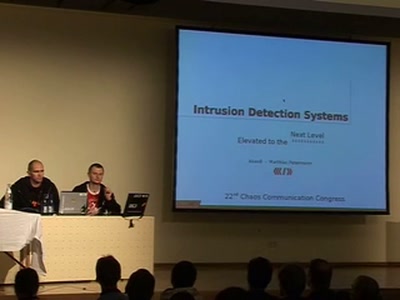
Intrusion Detection Systems
Elevated to the Next Level
54 min
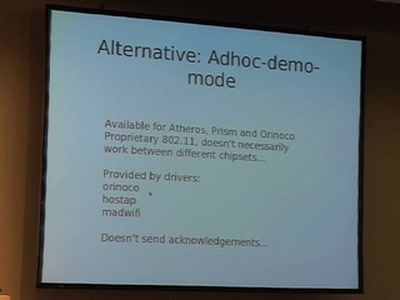
Community mesh networking
Ubiquitous wireless mesh clouds with olsrd from olsr.org

49 min
Syscall proxying fun and applications
Introduction to syscall proxying and applications for in…

66 min
COMPLETE Hard Disk Encryption with FreeBSD
Learn how to effectively protect not only your data but…

64 min
Covert Communication in a Dark Network
A major new version of freenet
59 min
Writing better code (in Dylan)
Fast development of object-oriented functional programs

45 min
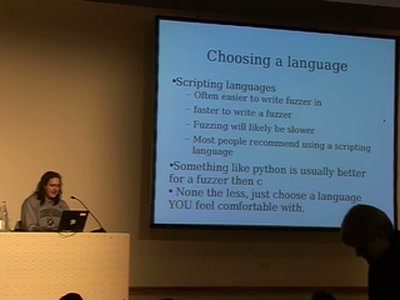
Finding and Preventing Buffer Overflows
An overview of static and dynamic approaches
![Advanced Buffer Overflow Methods [or] Smack the Stack](https://static.media.ccc.de/media/congress/2005/22C3-491-en-advanced_buffer_overflow_methods.jpg)
11 min
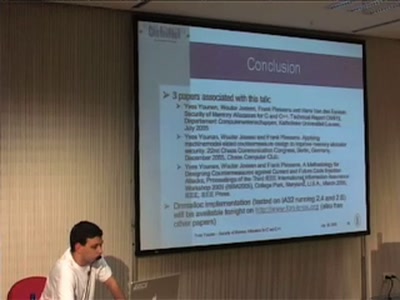
Advanced Buffer Overflow Methods [or] Smack the Stack
Cracking the VA-Patch

49 min
Old Skewl Hacking - InfraRed updated
MMIrDA - Major Malfunction's InfraRed Discovery Application
56 min
Towards the first Free Software GSM Phone
Reverse Engineering the Motorola EZX (A768,A780,E680)…
53 min
GNU/Linux für Blinde und Sehbehinderte
Erfahrungen aus der Praxis

43 min
Anonymous Data Broadcasting by Misuse of Satellite ISPs
An open-source project to develop a tool for broadband…
53 min
Blackberry: call to arms, some provided
Teach yourself upper management in 22 days
49 min
Lawful Interception in VoIP networks
Old Laws and New Technology the German Way

38 min
Autodafé: An Act of Software Torture
Presentation of an innovative buffer overflow uncovering…

49 min
VoIPhreaking
Introduction to SIP Hacking
42 min
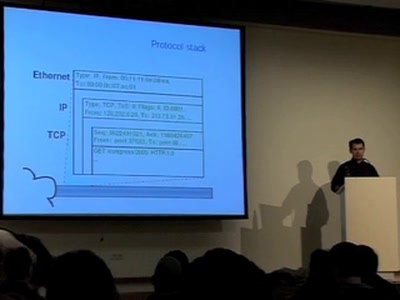
Covert channels in TCP/IP: attack and defence
Creation and detection of IP steganography for covert…
64 min
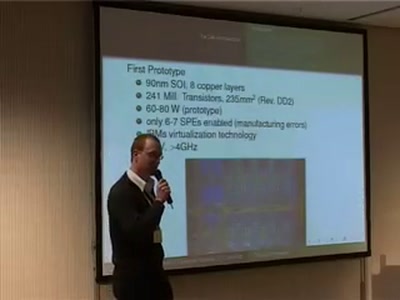
The Cell Processor
Computing of Tomorrow or Yesterday

47 min
Peer-to-peer under the hood
An in-depth look at p2p algorithmics

61 min
The Realtime Podcast
Everything you need to know about Podcasting

46 min
Honeymonkeys
Chasing hackers with a bunch of monkeys
53 min
WarTracking
Satellite Tracking, harvesting and security
44 min
The Realtime thing
What the heck is realtime - and what to do with it
57 min
Secure Code
Why developing Secure Software is like playing Marble…
56 min
Corp vs. Corp
Profiling Modern Espionage

55 min
The Future of Virtualization
The "anyOS" paradigm and its implications through…
54 min
Collateral Damage
Consequences of Spam and Virus Filtering for the E-Mail…

49 min
Hacking Data Retention
How bureaucrats fail to fight terror

60 min
Exploring Protocols and Services on Internet Connected Embedded Devices
Looking for Insecurities
45 min