Search for "Evan Roth" returned 986 results

36 min
Parkour communications
How you can communicate, free running style, using nothing…
21 min
Create a complete Tor .onion site with Docker and OpenSUSE in less than 15 minutes.
Doing something cool with minimum time.
57 min
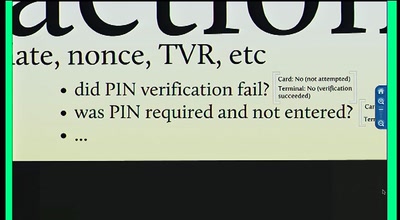
Chip and PIN is Broken
Vulnerabilities in the EMV Protocol
41 min
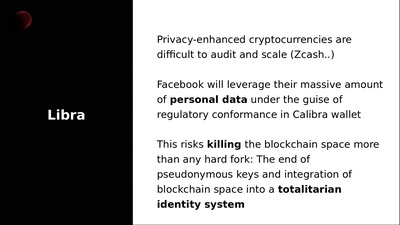
Fighting back against Libra - Decentralizing Facebook Connect
Nym Anonymous Authentication Credentials

73 min