Search for "Emploi"
next

59 min
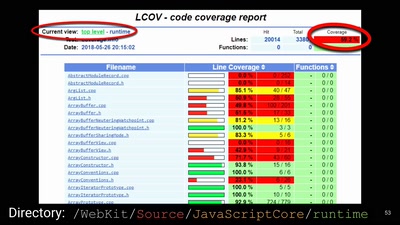
The future of IC analysis
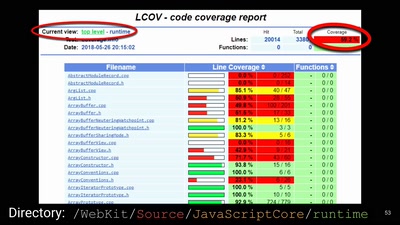
57 min
A demystification of the exploit development lifecycle

58 min
How do we do it at MySQL?
45 min
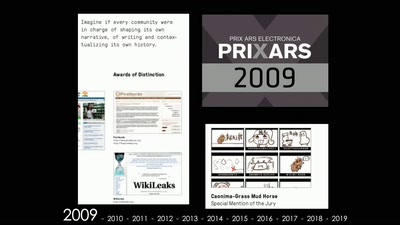
A Peek at Chinese Online Culture under the Censorship
20 min
A peer-to-peer, end-to-end encrypted social networking…
46 min
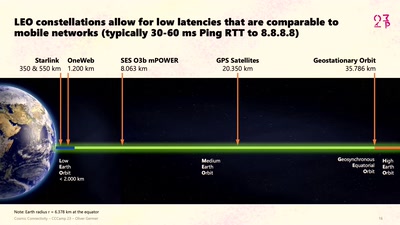
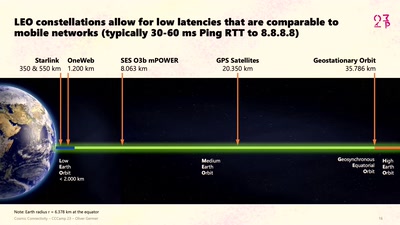
Starlink, Satellite Swarms, and the Hackers' Final Frontier
37 min
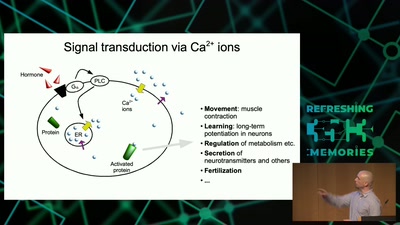
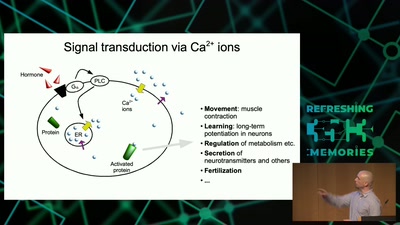
From cells to dynamic models of biochemical pathways and …

45 min
Spotting (digital) tech fictions as replacement for social…
38 min
Uncovering fake base stations on iOS devices
60 min
A semantics based approach

46 min
And a promising alternative for Public Communication and…

26 min
The struggle for security for all.
next